Attached files
| file | filename |
|---|---|
| EX-32.2 - EX-32.2 - Rapid7, Inc. | d319803dex322.htm |
| EX-32.1 - EX-32.1 - Rapid7, Inc. | d319803dex321.htm |
| EX-31.2 - EX-31.2 - Rapid7, Inc. | d319803dex312.htm |
| EX-31.1 - EX-31.1 - Rapid7, Inc. | d319803dex311.htm |
| EX-23.1 - EX-23.1 - Rapid7, Inc. | d319803dex231.htm |
| EX-21.1 - EX-21.1 - Rapid7, Inc. | d319803dex211.htm |
| EX-10.23 - EX-10.23 - Rapid7, Inc. | d319803dex1023.htm |
Table of Contents
UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
Washington, D.C. 20549
FORM 10-K
(Mark One)
| ☒ | ANNUAL REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 |
For the fiscal year ended December 31, 2016
OR
| ☐ | TRANSITION REPORT PURSUANT TO SECTION 13 OR 15(d) OF THE SECURITIES EXCHANGE ACT OF 1934 |
FOR THE TRANSITION PERIOD FROM TO
Commission File Number 001-37496
RAPID7, INC.
(Exact name of registrant as specified in its charter)
| Delaware | 35-2423994 | |
| (State or other jurisdiction of incorporation or organization) |
(I.R.S. Employer Identification No.) | |
| 100 Summer Street Boston, MA |
02110 | |
| (Address of principal executive offices) | (Zip Code) |
Registrant’s telephone number, including area code: (617) 247-1717
Securities registered pursuant to Section 12(b) of the Act:
| Title of each class |
Name of each exchange on which registered | |
| Common Stock, par value $0.01 per share | The NASDAQ Global Market |
Securities registered pursuant to Section 12(g) of the Act: None
Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act. YES ☐ NO ☒
Indicate by check mark if the registrant is not required to file reports pursuant to Section 13 or 15(d) of the Act. YES ☐ NO ☒
Indicate by check mark whether the registrant: (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities Exchange Act of 1934 during the preceding 12 months (or for such shorter period that the registrant was required to file such reports), and (2) has been subject to such filing requirements for the past 90 days. YES ☒ NO ☐
Indicate by check mark whether the registrant has submitted electronically and posted on its corporate Web site, if any, every Interactive Data File required to be submitted and posted pursuant to Rule 405 of Regulation S-T (§232.405 of this chapter) during the preceding 12 months (or for such shorter period that the registrant was required to submit and post such files). YES ☒ NO ☐
Indicate by check mark if disclosure of delinquent filers pursuant to Item 405 of Regulation S-K (§229.405) is not contained herein, and will not be contained, to the best of registrant’s knowledge, in definitive proxy or information statements incorporated by reference in Part III of this Form 10-K or any amendment to this Form 10-K. ☒
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, or a smaller reporting company. See the definition of “large accelerated filer”, “accelerated filer”, and “smaller reporting company” in Rule 12b-2 of the Exchange Act. (Check one):
| Large accelerated filer |
☐ |
Accelerated filer |
☒ | |||
| Non-accelerated filer |
☐ (Do not check if a small reporting company) |
Small reporting company |
☐ | |||
Indicate by check mark whether the registrant is a shell company (as defined in Rule 12b-2 of the Exchange Act). YES ☐ NO ☒
As of June 30, 2016, the aggregate market value of the registrant’s voting common stock held by non-affiliates of the registrant, based on a closing price of $12.58 per share of the registrant’s common stock as reported on The Nasdaq Global Market on June 30, 2016, was approximately $249,198,642. For purposes of this computation, all officers, directors and 10% beneficial owners of the registrant are deemed to be affiliates. Such determination should not be deemed to be an admission that such officers, directors or 10% beneficial owners are, in fact, affiliates of the registrant. The number of shares of registrant’s Common Stock outstanding as of March 1, 2017 was 42,640,674.
DOCUMENTS INCORPORATED BY REFERENCE
Portions of the registrant’s definitive Proxy Statement for its 2017 Annual Meeting of Stockholders to be filed with the Securities and Exchange Commission pursuant to Regulation 14A not later than 120 days after the end of the fiscal year covered by this Annual Report on Form 10-K are incorporated by reference in Part III, Items 10-14 of this Annual Report on Form 10-K.
Table of Contents
i
Table of Contents
PART I
Forward-Looking Statements
This Annual Report on Form 10-K, including the sections entitled “Business,” “Risk Factors,” and “Management’s Discussion and Analysis of Financial Condition and Results of Operations,” contains forward-looking statements that involve risks and uncertainties, as well as assumptions that, if they never materialize or prove incorrect, could cause our results to differ materially from those expressed or implied by such forward-looking statements. Statements that are not purely historical are forward-looking statements within the meaning of Section 27A of the Securities Act of 1933, as amended, and Section 21E of the Securities Exchange Act of 1934, as amended. Forward-looking statements are often identified by the use of words such as, but not limited to, “anticipate,” “believe,” “can,” “continue,” “could,” “estimate,” “expect,” “intend,” “may,” “plan,” “project,” “seek,” “should,” “target,” “will,” “would” and similar expressions or variations intended to identify forward-looking statements. These forward-looking statements include, but are not limited to, statements concerning the following:
• our ability to continue to add new customers, maintain existing customers and sell new products and professional services to new and existing customers;
• the effects of increased competition as well as innovations by new and existing competitors in our market;
• our ability to adapt to technological change and effectively enhance, innovate and scale our solutions;
• our ability to effectively manage or sustain our growth and to attain and sustain profitability;
• our ability to diversify our sources of revenue;
• potential acquisitions and integration of complementary business and technologies;
• our expected use of proceeds;
• our ability to maintain, or strengthen awareness of, our brand;
• perceived or actual security, integrity, reliability, quality or compatibility problems with our solutions, including related to security breaches in our customers; systems, unscheduled downtime or outages;
• statements regarding future revenue, hiring plans, expenses, capital expenditures, capital requirements and stock performance;
• our ability to meet publicly announced guidance or other expectations about our business, key metrics and future operating results;
• our ability to maintain an adequate rate of billings growth;
• our ability to attract and retain qualified employees and key personnel and further expand our overall headcount;
• our ability to grow, both domestically and internationally;
• our ability to stay abreast of new or modified laws and regulations that currently apply or become applicable to our business both in the United States and internationally including laws and regulations related to export compliance;
• our ability to maintain, protect and enhance our intellectual property;
• costs associated with defending intellectual property infringement and other claims; and
• the future trading prices of our common stock and the impact of securities analysts’ reports on these prices.
These statements represent the beliefs and assumptions of our management based on information currently available to us. Such forward-looking statements are subject to risks, uncertainties and other important factors
1
Table of Contents
that could cause actual results and the timing of certain events to differ materially from future results expressed or implied by such forward-looking statements. Factors that could cause or contribute to such differences include, but are not limited to, those identified below, and those discussed in the section titled “Risk Factors” included under Part I, Item 1A. Furthermore, such forward-looking statements speak only as of the date of this report. Except as required by law, we undertake no obligation to update any forward-looking statements to reflect events or circumstances that occur after the date of this report.
Overview
Rapid7 is a leading provider of analytics for security and IT operations that enable organizations to implement an active, analytics-driven approach to cyber security and IT operations. Our data and analytics platform was purpose-built for today’s increasingly complex and chaotic IT environment. We make it simple to collect and unify operational data from across the entire IT infrastructure, and our advanced analytics unlock the information required to securely operate, manage and develop today’s sophisticated applications and services.
We combine our extensive experience in collecting disparate data, deep insight into attacker behaviors and techniques and our purpose-driven analytics to make sense of the wealth of data available to organizations about their IT environments and users. Our powerful and proprietary analytics enable organizations to contextualize and prioritize the threats facing their physical, virtual and cloud assets, including those posed by the behaviors of their users. Leveraging our IT data and analytics platform, our solutions enable organizations to strategically and dynamically manage their cyber security exposure and manage IT operations. Our solutions empower organizations to prevent attacks by providing visibility into vulnerabilities, and allows them to rapidly detect compromises, respond to breaches and correct the underlying causes of attacks. By providing a unified IT and security platform, with automated workflow, we enable IT and security to work together more effectively to develop, operate and secure their environment. For example, our platform and proprietary technologies were developed to help customers identify the weaknesses and exposures in their environment and are designed to enable them to detect and respond to breaches immediately. We help them troubleshoot performance issues across their IT infrastructure, applications and endpoints. Our platform approach enables organizations to collect data once and use it for ongoing unlimited use and access to solve the specific problems their organization faces, reducing the costs and overhead associated with relying on point solutions, and enabling workflow between organizations that must work together to resolve issues, reduce risk and increase resiliency.
We offer analytic solutions across three core areas. Our Threat Exposure Management offerings include our industry-leading vulnerability management, web application security testing and attack simulation products, which we enhance with deep security analytics capabilities to quickly deliver contextual risk prioritization, critical threat awareness and impactful remediation guidance. Similarly, we added analytics and automation to traditional manual penetration testing to be able to deliver robust ongoing attack simulation solutions that provide organizations with visibility into real world threats. By providing and combining analytics, actionable insights and automated workflows related to both an organization’s attack surface and the dynamic threat landscape, our data and analytics platform enables organizations to manage their threat exposure above and beyond traditional vulnerability management products on the market. All of our products are designed with an intuitive user interface, focused on ease-of-use and fast time-to-value for our customers.
Further leveraging our data collection, analytics and attacker knowledge, we introduced our Incident Detection and Response solutions to provide organizations with the ability to rapidly detect and respond to cyber security incidents and breaches. We believe that the traditional approach to detecting and responding to incidents using Security Information and Event Management, or SIEM, Intrusion Detection System, or IDS, and Intrusion Prevention System, or IPS, technologies, among others, is not entirely effective. These technologies can burden an organization with unmanageable volumes of alerts and false positives. Our solutions use advanced analytics to help identify cyber threats to an organization and provide IT security teams with the ability to easily build incident timelines for faster investigations and more efficient resolution, as well as enabling search across the
2
Table of Contents
organization’s data from our Insight Platform. Proprietary behavioral and pattern-recognition analytics are central to this capability, which functions in part by automatically mapping an organization’s assets and users relative to the threat landscape, such that aberrant and risky user-specific and asset-specific behaviors are rapidly identified, escalated for investigation and prioritized by threat level. To complement our incident detection product, we offer a range of services. These include our recently introduced Managed Detection and Response (formerly known as “Analytic Response”) service, which provides our customers with a managed service for threat detection and response, and our incident response professional services through which we provide critical access to our security experts and experience to organizations that have identified a serious security incident, enabling them to accelerate incident response and containment. We also offer Security Advisory Services that help organizations develop a holistic approach to their cyber security programs, test their incident response preparedness and advance their cyber security program maturity.
Cyber security and infrastructure reliability have become a strategic imperative for organizations globally, driven by increased focus by boards of directors and senior management in the wake of numerous high profile breaches, data thefts and publicly visible IT outages. Three converging macro drivers are changing the cyber security landscape for organizations and driving the increase in cyber breaches. First, mobile and connected devices, cloud-based applications and more open and interconnected networks have increased IT complexity, expanding the exploitable attack surface across an organization and increasing the opportunities for system failure. Second, there has been a dramatic change in the tools available to cyber attackers. Attackers can now purchase, at very low cost, highly effective and easy-to-use software that is designed to circumvent traditional prevention-based tools, thereby lowering the bar for nearly anyone to launch advanced cyber attacks. Third, the economic motives for attackers are more compelling, with new, vibrant markets providing attackers an efficient and effective way to monetize stolen customer information and employee data.
The confluence of these factors has dramatically increased the need for IT and security staff to work together to prevent both cyber attacks and system failures, and to drive insight and automation from data. These factors also render the old model of “block and protect” prevention-based cyber security programs ineffective. These traditional “block and protect” approaches to cyber security typically rely disproportionately on network perimeter protection tools such as firewalls and antivirus software to stop attackers. However, as the network perimeter rapidly disappears, the effectiveness of these legacy solutions diminishes greatly. Prevention-centric models are often passive and implemented with a “deploy and forget” mentality, lacking a holistic cyber security and IT risk strategy. While these approaches can alert IT professionals to potentially suspicious activity or potential problems throughout the IT environment, the data generated is often raw and in “machine form,” and rarely comprehensive, making it difficult for an organization to develop actionable insights that reflect a real-time understanding of the organization’s assets, user behavior and the dynamic threat landscape that it faces. Developing these insights has historically been complex and resource intensive, requiring security expertise, data scientists and analytical modeling skills, which many organizations lack. The decreasing effectiveness of a traditional prevention-focused approach to IT and cyber security is causing a significant shift to a new model that uses an active, analytics-driven approach to reduce and manage risks to the organization. This new model disrupts the historical focus on “block and protect” solutions and balances organizations’ investments in prevention, detection and correction to reduce the likelihood of, and risks associated with, cyber attacks and system failures. Effective implementation of this new model demands data and analytics to assess the effectiveness of tools and programs, identify anomalous behaviors and prioritize and remediate exposures. We empower organizations to more securely and productively develop and manage their dynamic IT environments by providing the security data and analytics that are at the core of a holistic and active, analytics-driven approach to IT risk management.
As of December 31, 2016, we had more than 6,200 customers, including 38% of the organizations in the Fortune 1000. We have experienced strong revenue growth with revenue increasing from $46.0 million in 2012 to $157.4 million in 2016, representing a 36% compound annual growth rate. We have strong visibility to our revenue as 55% of the revenue recognized in 2016 was recorded on our balance sheet as deferred revenue as of December 31, 2015 and 86% of the revenue recognized in the fourth quarter of 2016 was recorded on our
3
Table of Contents
balance sheet as deferred revenue as of September 30, 2016. We incurred net losses of $49.0 million, $49.9 million and $32.6 million in 2016, 2015 and 2014, respectively, as we continued to invest for long-term growth.
Recent Developments
In November 2016, we announced the beta launch of InsightOps, a new IT operations solution designed to centralize machine data across organizations’ infrastructures. This solution is designed to provide IT teams with comprehensive operational awareness by pairing endpoint visibility and log analytics. With InsightOps, we believe that IT professionals will have the ability to easily search and ask questions of their data to gain insights regarding core issues related to their IT environments faster, which, we believe, will ultimately improve uptime and business productivity. InsightOps is currently being tested in a beta program, and we anticipate it will be ready for sale during the first half of 2017.
In November 2016, we announced the appointment of Jeff Kalowski as our new Chief Financial Officer, effective January 9, 2017. He replaced Steven Gatoff, who joined us at the beginning of 2013, announced his planned departure in August 2016 and formally transitioned from our company in January 2017.
In October 2016, we announced that Andrew Burton, who was formerly our senior vice president of Logentries, was promoted to the position of Chief Operating Officer.
Benefits of Our Solutions
We are a leading provider of analytics for security and IT operations that enable organizations to implement an active, analytics-driven approach to cyber security and IT operations. Key benefits of our solutions include:
Decreased Risk of Security Breach. Our technology platform and solutions provide IT security professionals with a more complete view of their dynamic attack surface and automatically assess an organization’s vulnerabilities relative to the evolving threat landscape. We provide robust and relevant analytics and insight into attacker behaviors and techniques so that IT security professionals are able to identify and prioritize risks effectively to reduce risks and ultimately create a more secure IT environment for their organization. Our solutions allow our customers to test their defenses by simulating real-world attacks on their IT environments, using the same techniques and exploits as attackers. Our solutions leverage our security data and analytics expertise as well as the insights from our community of thousands of active Metasploit users who provide us with real-time, real-world insight into attacker behavior across the global IT attack surface. Our data and analytics are coupled with our deep search technology that allows IT organizations the ability to deeply investigate risks such that they can be contained and remediated quickly. Our integrated workflows enable IT and security teams to work together more effectively to reduce risks across the entire ecosystem.
Fast, Effective and Confident Intrusion Response. Our product and service offerings can help mitigate the impact of a breach by automatically identifying the root cause of a breach and providing clear and actionable insight into effective mitigation and correction. Our technology automatically monitors each user and IT asset within an organization without the need to build and maintain complicated detection rules or data queries. Rather than sending numerous alerts and alarms that become an onslaught of overwhelming and unintelligible data, our solutions provide timely, prioritized and clear analysis and instructions to IT security professionals so that they can quickly, confidently and effectively respond to cyber security breaches. Furthermore, we couple our detection technology with our deep search capabilities, which can improve the time from compromise to containment. Complementing our products and managed services, when an organization is breached, our incident response professionals leverage our deep security expertise to help guide customers through critical breach response tactics and implementation of mitigation strategies.
Increased Uptime and Faster Resolution for IT and DevOps. By collecting and analyzing machine data from across an organization’s entire IT environment, our Insight Platform provides solutions for security, IT, and
4
Table of Contents
development operations. With real-time data collection and processing capabilities, IT and DevOps professionals can be instantly alerted to issues impacting their IT environments or production applications and perform immediate root cause analysis through search, data visualization, and reporting functionality. Our cloud-based Insight Platform eliminates the need for IT and DevOps to deploy and manage costly, complex servers and systems to store and manage data, thus reducing overall operating costs.
A Continually-Relevant and Effective Security Program. We serve as a trusted security advisor to our customers, providing both products and professional services that enable organizations to implement an active, analytics-driven approach to cyber security. Our solutions are continually relevant as they evolve with, and react to, the dynamic threat landscape. Guided by our holistic approach balancing prevention, detection and correction solutions, we provide strategic, technology-agnostic guidance tailored to an organization’s security maturity and optimized to an organization’s IT environment.
Our IT and Security Analytics Platform
Our Insight Platform is at the core of our IT and security analytics product offerings. The platform was built using our extensive experience in collecting and analyzing data to enable our customers to create and manage active, analytics-driven cyber security and IT operations management programs. There are two fundamental and competitively differentiating capabilities of our technology platform: (1) the breadth and depth of data that we collect and (2) the powerful analytics, and resulting correlation and context that we apply to the data. Our robust data collection architecture supports gathering a wide swath of organizational and environmental data from endpoints to the cloud, including key data about user-specific behavior. Further, by offering both agent and agentless data collection, we can provide IT professionals with seamless integration and automatic visibility into their dynamic and rapidly-expanding IT and applications infrastructure. By utilizing our powerful, proprietary analytics to assess and understand the context and relationships around users, IT assets and cyber threats within a customer’s environment, we can provide our customers with specific, actionable insights for both security and IT operations.
Our Insight Platform was architected from inception to be secure, reliable, scalable and extensible, enabling both us and third-party developers to create and add new applications that leverage our powerful data collection and analytics competencies. The design and development of our Insight Platform includes the following key attributes:
Holistic Dataset for Managing IT Operations and Cyber Security. Our Insight Platform collects information from multiple sources to provide a holistic view across an organization’s ecosystem from network and endpoint data, to enterprise cloud data, to user information. We collect data from the following sources: cyber security assets such as firewalls, intrusion detection systems, or IDS, intrusion prevention systems, or IPS, and security information and event management, or SIEM; user directories; endpoints such as computers, mobile and connected devices and servers; applications; cloud activity; IT environment permissions, policies and controls; and third parties, such as cloud-based email and business productivity solution providers. Our platform provides robust coverage of known vulnerabilities, exploits and threat intelligence to identify and prioritize threats to the organizations.
Robust Platform and Customer Data Security. Our Insight Platform was designed to provide a secure environment for both our data and that of our customers. We deploy a variety of technologies and industry-leading practices such as physical and logical customer data segregation, network segmentation, audited and monitored access level controls, data anonymization and separated development-staging-production environments to help ensure that the data collected from a customer’s environment remains proprietary and secure, including encrypting data when appropriate. Further, we regularly run penetration tests of our platform. We have achieved Service Organization Control (SOC) II Type 2 certification for the foundation of our platform and are continuing to expand the specific compliance regimes for which we are audited.
5
Table of Contents
Both Agentless and Endpoint Agent Based Architecture with Fast Search. We have designed our solutions to be easy to deploy with minimal manual input from our customers. We developed our platform with flexible processing technologies that employ both agentless data collection and our own internally-developed endpoint agent technology, which enables rapid and seamless integration of our products into our customers’ IT environments and provides IT professionals with instant visibility into their dynamic and rapidly-expanding IT ecosystem. Our agent technology automatically collects endpoint data valuable to vulnerability management, security incident detection and response and IT operations. Security and IT professionals then have the ability to directly query endpoints to collect forensic and other information critical to security incident and operational investigation. Our search technology enables IT and security professionals to search across the entire IT ecosystem including endpoints and, unlike other machine search solutions, provides live access without having to wait for lengthy indexing processes.
Enterprise-Grade Scalability. Our technology platform provides a high level of horizontal scalability. We leverage on premise deployment models and Amazon Web Services, or AWS, to achieve a high degree of redundancy, fault tolerance and cost-effective operations. We are currently deployed in two AWS regions, with plans to add additional geographies. Our automated deployment technologies enable us to add new AWS instances or additional services rapidly. Within our platform, we use a variety of SQL and NoSQL technologies to enable broad scalability, while keeping each customer’s data entirely separate. Our infrastructure architecture is designed to process large amounts of data and easily incorporate new data sources, including on premise, cloud and mobile. Our platform is designed to support customers with large numbers of users or with geographically dispersed environments, and we have scaled to meet the needs of customers with over 2.0 million active assets and 200,000 active users.
Extensible Modern Platform. Our technology platform provides a rich set of APIs and services that enable customers, partners and developers to import and export data and utilize our analytics capabilities. This allows us to easily integrate with other security tools in the customer’s environment and also enables customers to build bespoke applications and analysis on top of the data that we gather.
Our Products and Services
We offer products and professional services that leverage our analytics for security and IT operations. We typically engage with customers based on their current needs determined in large part by what is occurring in their IT environments, within their industries and the initiatives of their senior management and boards of directors. We offer three broad solution groups: Threat Exposure Management, Incident Detection and Response, and Security Advisory Services. With our Security Advisory Services, we offer a range of strategic services to assess current capabilities and advise organizations on how to best improve and optimize their security programs. An organization that has just detected that it has been breached, for example, may initially purchase our Incident Detection and Response products and services whereas a customer with a new chief information security officer looking to gain insight into the organization’s security environment may initially purchase our Threat Exposure Management solutions. A customer whose board of directors has mandated a security review may initially purchase our Security Advisory Services and an IT director interested in monitoring IT performance and troubleshooting may purchase our log and analytics solution.
Our Threat Exposure Management solutions reflect our evolution and enhancement of traditional vulnerability management tools to encompass a broader set of data, including real-world threat information, a robust application security testing capability, and analytics workflow that facilitate systematic remediation. By providing IT security professionals with a complete view of their changing attack surface and an automated way to assess the evolving threat landscape, our customers can implement a data and analytics-driven cyber security program to minimize high-priority risks.
Our Incident Detection and Response solutions offer customers a combination of product-based analytics as well as expert services to help detect attackers and respond to attacks once they are discovered. Additionally, these solutions enable information security teams to solve a broader range of security challenges, investigate incidents
6
Table of Contents
and more efficiently achieve their compliance requirements. Our IT operations optimization solutions centralize machine data to provide comprehensive visibility and control across the IT environment. These solutions provide real-time search across structured, unstructured and semi-structured data to investigate anomalies, troubleshoot issues and conduct root cause analysis.
We offer our products through a combination of perpetual and term software licenses, cloud-based subscriptions and managed services offerings. Our products have been designed with an intuitive user interface, focused on ease-of-use and fast time-to-value for our customers.
Our Security Advisory Services help organizations implement and manage an analytics-driven security approach by looking strategically and holistically at their security programs and providing them with advice related to prevention, detection and correction. We believe that our professional services drive incremental customer adoption and usage of our products.
Threat Exposure Management
Our Threat Exposure Management solutions help organizations systematically and dynamically manage cyber vulnerabilities, allowing them to understand their exposures and prevent attacks through insights into their IT and application IT environments. In building our Threat Exposure Management offerings, we brought security data and analytics capabilities to our core competencies around vulnerability management to drive insights into customer exposures, management and remediation. Our Threat Exposure Management offerings are available to customers through perpetual and term software licenses with content subscriptions that provide our customers with real-time access to the latest vulnerabilities and exploits, and also as a managed service. Additionally, we provide deployment support and training.
Our Threat Exposure Management offerings include:
Nexpose
Nexpose enables customers to assess and remediate their overall exposure to cyber risk across their increasingly complex IT environments. This includes analyzing vulnerabilities, detecting security misconfigurations and determining the effectiveness of controls across an IT environment. The key features of Nexpose include: automatic vulnerability updates; exception management, which allows organizations to track when risk is knowingly introduced into the IT environment; executive remediation and security testing reporting; interactive charting; scan scheduling and alerting; RealContext classification, which allows organizations to apply business context to threats including by identifying where sensitive data is stored; web application, virtual, unified vulnerability, perimeter and discovery scanning; policy compliance and management, including with standards such as PCI and HIPAA; report and scan customization; Open API and third-party integrations; advanced report templates and uploading; dynamic discovery; user role customization; integrated vulnerability validation; controls effectiveness testing; prioritized guidance based on customized threat models; dynamic live dashboards that are easily customizable and queried; lightweight cloud agents for continuous monitoring; and remediation workflow for assigning and tracking remediation progress live within the product. Nexpose is offered through perpetual and term software licenses or as a managed service. The managed service is known as Managed Vulnerability Management, which provide our resource constrained customers with a fully outsourced option for leveraging our innovation, expertise and technology. We handle the deployment and operational requirements of vulnerability scanning with regular assessments and concise reporting, enabling higher client productivity and access to highly skilled resources and our proprietary technology, without incurring the costs associated with a dedicated IT support team.
Metasploit
Metasploit is an industry-leading penetration testing software, developed on an open source framework. Metasploit can be used to safely simulate attacks on an organization’s network in order to uncover vulnerabilities
7
Table of Contents
before they are exploited by cyber attackers and assess the effectiveness of an organization’s existing defenses, security controls and mitigation efforts. The key features of Metasploit include: wizards for standard baseline audits; task chains for automated custom workflows; modules for discrete tasks, such as network segmentation testing; dynamic payloads, designed to evade leading antivirus solutions; closed-loop vulnerability validation to prioritize remediation; phishing awareness management and spear phishing; web-based interface; integrations via remote APIs; and a hardware bridge for testing IoT and hardware devices. We sell two editions of Metasploit: Metasploit Pro is our advanced penetration testing and security program solution targeted at penetration testers and IT security teams and Metasploit Express is our baseline penetration testing product targeted at IT generalists. Metasploit Pro integrates with Nexpose to enable IT security professionals to prioritize remediation efforts and understand the impact of an attack before it happens. We also offer a free community version of Metasploit for small companies and students, as well as the open source framework, which is geared toward developers and security researchers. Metasploit is offered through perpetual and term software licenses.
AppSpider
AppSpider is a comprehensive dynamic application security testing solution that continuously analyzes web applications for security vulnerabilities and enhances organizations’ ability to effectively reduce IT security risk. The key features of AppSpider include: a universal translator to enable IT security professionals to analyze complex applications, including rich internet applications built using AJAX or GWT and web services such as REST and JSON; customized attack simulation capabilities that allow IT security professionals to automatically test complex business workflows such as shopping carts; scanning automation; live vulnerability reports and attack replay, which allows IT security professionals to replay vulnerabilities in real time in order to verify that vulnerabilities are exploitable and that successful remediation has occurred; continuous site monitoring, which detects changes in application ecosystems and triggers a re-scan according to configurable settings; and integration with protection technologies to automatically generate web application firewalls, or WAFs, custom rules that help to protect vulnerable applications while the vulnerabilities are being remediated. AppSpider supports most leading WAFs, including F5, Sourcefire and Imperva. AppSpider is offered through perpetual and term software licenses, on a cloud-based subscription basis or as a managed service. The managed service is known as Managed Application Security, and provides a fully outsourced option for application scanning and security testing for both resource-constrained organizations and those seeking to supplement their own capabilities. Our services include scan management, vulnerability validation and penetration testing delivering a consistent application assessment process for our customers.
Incident Detection and Response
All of our Incident Detection and Response solutions are united by a common thread: a deep understanding of the attacker mindset. With our Metasploit community, research and incident response services, we are continually studying and identify the latest attacker methods. We have learned and continue to learn how attackers behave and how to detect them before they can inflict damage. We have found ways to increase accuracy, speed the process, and achieve greater confidence, even as attacker methods change. That real-world expertise directly informs the software and services we deliver to equip security professionals – from resource-strapped small teams to fully staffed 24/7 operations – with the capacity to swiftly thwart attackers. Our incident detection products are available to customers as a cloud-based subscription or as a managed service. We also provide incident response services to provide customers with critical expertise in the wake of a breach.
Our Incident Detection and Response offerings include:
InsightIDR
InsightIDR is a cloud-based Incident Detection and Response solution which unifies SIEM, user behavior analytics (UBA), and endpoint detection to detect stealthy attacks across today’s complex networks. It analyzes the billions of events that occur daily in organizations to reduce them down to the important notable behaviors
8
Table of Contents
and deliver only high-fidelity and prioritized alerts. In addition to identifying stealthy attacks often missed by other solutions, InsightIDR focuses the security team on issues that warrant investigation and reduces the time to investigate with its user correlation, powerful search and endpoint interrogation capabilities. InsightIDR became available in the first quarter of 2016, and incorporates our InsightUBA product into its feature set.
Managed Detection and Response
Managed Detection and Response is a managed service that combines our team of expert analysts with our leading incident detection and user behavior analytics technology, InsightIDR. With their extensive experience, our team of experts leverage attacker behavior analytics, machine learning algorithms, and threat intelligence to hunt attackers in our customers’ environments. When attacks are found, customers are promptly informed of all known details and our team moves to incident response, providing security teams with detailed, easy-to-follow remediation steps tailored to the environment.
Incident Response Services
When a breach occurs, our incident response services give our customers access to our industry-leading security experts and experience, enabling customers to accelerate incident investigation, forensics, and containment. Our incident response professionals collaborate with each organization’s IT security professionals on all stages of incident response from analysis through containment, remediation and cleanup.
Logentries
Logentries’ technology, acquired in October 2015, provides a powerful cloud-based solution for collecting, searching, visualizing and analyzing log data. Built-in tagging, alerting and reporting make it easy for customers to maintain a proactive view of their environment and identify anomalous events. Logentries’ scalable, cost-effective architecture enables organizations to store and search structured, semi-structured and unstructured data in real time, enabling DevOps and IT professionals to centralize, search and monitor their log data in order to investigate anomalies, troubleshoot issues and conduct root cause analysis. This offering can be used for application debugging and performance monitoring, infrastructure monitoring and troubleshooting, and secure log aggregation in support of compliance requirements.
InsightOps
InsightOps is a new IT operations solution designed to centralize machine data from across organizations’ IT environments for comprehensive operational awareness and control. By pairing endpoint visibility with log analytics, InsightOps will empower IT professionals to quickly identify issues and perform root cause analysis down to the individual endpoint. With InsightOps, we believe that IT professionals will have the ability to easily search and ask questions of their data, visualize trends, and produce reports that deliver key insights regarding their IT environments faster, and we believe, resulting in improved uptime and business productivity. InsightOps is the evolution of Logentries and is currently being tested in a beta program, and we anticipate it to be ready for sale during the first half of 2017.
Security Advisory Services
Our Security Advisory Services help customers transform their organizations’ security programs to be relevant, actionable and sustainable through a data and analytics-driven cyber security program. Our offerings include Cyber Security Maturity Assessment, Incident Response Program Development, Penetration Testing, Security Program Development, Virtual CISO, IoT Security Services and Threat Modeling. Customers can take control of their organizations’ security with help from our seasoned security professionals who have deep experience building and managing security programs, with expertise in security strategy, vulnerability management, fraud detection, threat intelligence and incident response.
9
Table of Contents
Our Security Advisory Services enhance our ability to serve as a trusted advisor in assisting organizations to think proactively about IT security and implement strategic, analytics-driven security strategies. We believe that our role as trusted advisor helps drive customer success and loyalty and further usage of our products.
Our Competitive Strengths
We have developed the following key competitive advantages that we believe will allow us to grow and maintain a leadership position in the market for analytics for security and IT operations:
Automated Data Collection from the Endpoint to the Cloud. We have deep technology expertise in data collection from 16 years of experience in vulnerability management. Our Insight Platform provides robust data collection capabilities across multiple data sources, from endpoint information, to user behaviors, to cloud activity. As an organization’s infrastructure evolves and expands, additional data sources are quickly and efficiently integrated into our platform. Further, our Insight Platform uses flexible collection methods including a lightweight, easy to deploy endpoint agent that provides instant endpoint visibility to support vulnerability management, security incident detection and IT operations. This allows our platform to amass data from multiple sources quickly and without significant customer installation expertise, while providing greater visibility to IT security professionals. We believe that the simplicity of integrating our products into a customer’s IT environment is a key competitive differentiator for us, as it provides a significant advantage for IT security professionals who may otherwise be unable to collect and process the necessary data from across their organization.
Customer and Use-case Specific Analytics. We understand that developing, managing and securing a modern IT infrastructure requires a combination of role specific analytics and automated workflow to enable success, and the ability to identify and adapt to the risks specific to each of our customer’s organizations. Our technology platform collects and organizes data from each customer’s unique IT environment, which allows us to systematically and automatically profile the key risks specific to each customer. By utilizing our powerful, proprietary analytics to assess and understand the context and relationships around users, IT assets and cyber threats within a customer’s environment, we can provide our customers with specific, actionable insights specific to their environments. The applications built on our Insight Platform allow our customers to collect data once, but use it to solve a range of challenges from reducing risk, to identifying and responding to security incidents to quickly resolving IT issues impacting user productivity. Our analytics are purpose built with an emphasis on accuracy, usability and relevance.
Robust and Relevant Knowledge of Attacker Activity. Our database of more than 85,000 known vulnerabilities is continuously expanding through the efforts of our internal security experts and the broader Metasploit community. Our ties to the security research community through Metasploit, an open source project with an active community of contributors and users that was downloaded over 160,000 times in 2016, provides us with real-time insight into new attacks and exploits. The size and accuracy of our exploit database and the speed at which our Threat Exposure Management offerings are updated provides significant value to IT security professionals looking to secure their networks in a dynamic and evolving threat environment. We also have a team of experienced security researchers who support our knowledge and security insights through threat intelligence research and attacker modeling.
Intuitive Product Design Focused on Speed to Insight. Our solutions are designed for ease-of-use by IT security professionals. Our underlying technology platform can easily become part of our customers’ operational fabric without requiring internal expertise in systems integration, data science or data scripting. Our solutions are designed to abstract the powerful underlying capabilities of our IT and security analytics platform so that users interact with a simple, elegant interface. We believe that this clean user interface and intuitive design of our products differentiate Rapid7 products from the competition and enables our customers to develop actionable insights quickly and with limited training. We believe that our solutions are resource efficient for our customers and provide them with a fast time-to-value, which makes it easy for organizations to understand the benefits of an active, analytics-driven approach to cyber security and IT operations analysis.
10
Table of Contents
Deep IT and Security Domain Expertise Across Technology, Operations and People. We leverage our deep domain expertise in IT and security analytics to better serve our customers, who frequently have limited ability to carry deep expertise in-house. We offer Security Advisory Services to help customers assess the quality of their security programs and implement changes to make them more effective and cost efficient. We also offer Incident Detection and Response services to help customers find and respond to attacks and compromises that they may be missing on their own. Ultimately, we serve as a trusted security advisor to our customers, encompassing a powerful combination of technology, services and operations expertise to support our customers’ success in managing their cyber security exposure. We believe that this differentiates our offerings, resulting in strong customer retention and our ability to expand our share of our customers’ security spending over time.
User Behavior Analytics. We believe that our user-centric approach to analytics is a key differentiator of our technology platform and offerings. Our software solutions automatically create a behavior profile for each user in a customer’s IT environment and automatically correlates every event and device with the correct user. Without this automated correlation, security and IT professionals must search through several technology systems to manually find and connect the information. In addition to saving precious time when things go wrong, our user behavior analytics vastly improve the efficacy of our security incident detection. We compare user profiles against dynamic attacker behavior profiles to distinguish normal user behavior from suspicious behavior and incorporate additional data about how systems are likely to respond when under real-world attack. Within our technology platform, our prioritization engine triangulates on the most important data to determine potentially compromised user credentials and reduce false signals and alerts. In addition, our ability to provide rapid context around users and assets involved in an incident can significantly reduce investigation time, enabling organizations to more quickly respond to, contain and mitigate breaches. These powerful user-centric analytics allow IT security professionals to make informed and proactive decisions.
Fast and Accessible Search Capabilities. We believe that our ability to enable fast search through an organization’s data and endpoints can enable IT security professionals to better investigate and operationalize data to quickly identify the root cause of issues. Our solutions allow IT security professionals to collect both structured and unstructured machine data and to obtain rapid access to their data. These capabilities, along with real time and easily accessible search across raw logs and endpoints for known patterns with intuitive search queries, can enable IT security professionals to access their data for operational purposes.
Our Growth Strategy
Our mission is to deliver insight from today’s broken IT data ecosystem with simple yet powerful solutions that make IT and security teams smarter, more secure and more productive. Key elements of our growth strategy include:
Drive New Customer Additions. We believe that most organizations with IT infrastructure would benefit from our products and services, regardless of size or industry, and we have a significant opportunity to increase our penetration across these organizations. In particular, we are focused on further penetrating large enterprises and middle-market businesses. We have principally sold our products and services through our direct inside sales team and address the Fortune 1000 customer with a direct field sales team. We intend to continue to invest in building our global sales and go-to-market organizations. See “Our Customers” for additional information regarding our markets.
Increase Customer Economics and Success. Our customer base includes more than 6,200 customers, as of December 31, 2016. We believe that these customers provide us with a significant opportunity to drive incremental sales by both selling larger volumes of the offerings that a customer is already purchasing from us and cross selling other offerings from our portfolio to these customers. For example, customers acquired in 2012 have spent, in the aggregate, 3.1 times their initial 2012 spend with us through 2016, which we believe reflects both our strong renewal rates and our ability to drive upsells and cross-sells. We believe that we currently only capture a percentage of the total cyber security budgets of our enterprise customers and we believe that they will
11
Table of Contents
increase their spending with us as they continue to shift their programs to security data and analytics-centric strategies. We have a dedicated customer success team focused on engagement and education to drive customer loyalty and increased purchases of our solutions.
Continue to Expand Internationally. In 2016, we generated 14% of our revenue from customers outside of North America. We believe that cyber attacks are increasingly global in nature and that organizations globally are increasingly shifting to an active, data and analytics-driven approach to cyber security. We plan to continue to increase our international sales, service and support organizations to target additional sales across Europe and Asia and will also continue to expand our number of channel partners internationally.
Continue to Innovate with Our Products and Technology Platform. We plan to build upon our current performance and technology leadership in security data and analytics to enhance our technology platform and product capabilities, and to add new products to address the needs of IT operations staff. For example, in early 2016 we announced InsightIDR, our comprehensive Incident Detection and Response solution that can enable organizations to go from compromise to containment quickly and can also meet their operational compliance needs. This new solution integrates our recently acquired Logentries machine data search technology. InsightIDR builds on our Insight Platform, and our deep understanding of attacker behavior, to provide organizations with actionable insights into security incidents. In late 2016, we announced the beta launch of InsightOps, which also integrates Logentries machine data search technology with the Insight Platform, to provide IT teams with comprehensive operational awareness by pairing endpoint visibility and log analytics. With InsightOps, we believe that IT professionals will have the ability to easily and quickly search and ask questions of their data to gain insight regarding cores issues, faster.
Serve as the Hub for IT and Security Analytics Our robust and comprehensive data collection capabilities, deep understanding of the attacker, analytics and workflow-driven approach and leadership within the industry position us to fundamentally change the way that organizations approach cyber security and IT operations. Moreover, our technology platform was developed with open application program interfaces, or APIs, to allow other developers to access the data that we collect and the powerful analytics that we provide. We expect to continue to offer new analytics-based solutions for both IT and cyber security operations and that third-party application developers will continue to leverage our data collection and analytics capabilities.
Our Customers
Our customer base has grown from approximately 2,260 customers at the end of 2012 to more than 6,200 customers as of December 31, 2016, in 117 countries, including 38% of the organizations in the Fortune 1000. We define a customer as any entity that has 1) an active Rapid7 contract or a contract that expired within 90 days or less of the applicable measurement date; and for Logentries products, those customers with a contract value equal to or greater than $2,400 per year, and 2) purchased Rapid7 professional services within the 12 months preceding the applicable measurement date. We provide products and services to customers of varying sizes, including enterprises, non-profit organizations, educational institutions and government agencies. 57% of our revenue in 2016 was generated by large enterprises, which we define as organizations that have either annual revenue greater than $1.0 billion or more than 2,500 employees, and the balance was generated by middle-market businesses. Our customers span a wide variety of industries including technology, energy, financial services, healthcare and life sciences, manufacturing, media and entertainment, retail, education, real estate, transportation, government and professional services, with customers in the finance industry representing our largest industry in 2016 at 15% of our revenue. Our revenue is not concentrated with any individual customer or group of customers, and no customer represented more than 2% of our revenue in 2016, 2015 or 2014.
Rapid7’s Community
Our online community provides us with a rapidly growing network of active users and influencers who promote the usage of our software, identify cyber risks and provide technical support to each other. Our community includes paid customers of our software, users of free “community” trial editions of our software, security
12
Table of Contents
researchers, and users and contributors to our open source Metasploit Framework, which is used to simulate attacks and test an organization’s defenses against real-world threats.
Our Metasploit project has an active community of contributors and users and the penetration testing tool was downloaded over 160,000 times in 2016. This online security community provides us with a robust and rapidly growing network of active users and influencers who promote the usage of our software. Security researchers contribute modules to the Metasploit Framework that serve as a resource about real-world attacker techniques. The community also provides us with near real-time visibility into new cyber attacks as they occur and a deep understanding of attacker behaviors.
We are also an established leader in security research and the disclosure of vulnerabilities. In recognition of this leadership through well-coordinated vulnerability disclosures to vendors and consumers alike, we were recently designated as one of the first companies to be named a third-party Common Vulnerability and Exposures (CVE) Numbering Authority by The MITRE Corporation, a not-for-profit organization that works in the public interest. In addition, through Project Sonar, we are providing actionable insight into the behavior of global adversaries plus critical information on the exposures and weaknesses of key internet services, based on weekly internet-wide active scans and daily passive activity monitoring via a large-scale network of highly customized honeypots. The intelligence gathered through these research projects is infused in all of our products and services, with certain excerpts provided to the broader research community through the University of Michigan, our academic research partner.
Technology Alliance Partnerships
Our IT and security analytics platform has the ability to leverage a broad partner ecosystem with over 80 technology platform integrations as of December 31, 2016. We allow other developers to access the data that we collect and the powerful analytics that we provide. We also built our platform with the ability to leverage APIs and data collection from other technologies. This allows us to integrate with other IT and security technologies that our customers may already have in place in three primary ways.
| • | Data Collaboration. Our data collaboration integrations provide two-way data sharing to enhance our platform value. For example, we can ingest data from an existing SIEM technology and also share our analysis of user behavior activity with the SIEM technology. |
| • | Data Workflow. Our data workflow integrations enable IT security integration to streamline the process of correction and improve efficiencies. For example, we make remediation data from our platform available to IT ticketing systems in order to drive operational efficiencies and tracking of IT performance. |
| • | Data Ingestion. Our data ingestion integrations enhance our analytical capabilities by funneling increased volumes of data to our platform. For example, we ingest firewall data into our platform, which allows us to better understand user activity in the context of attacks. |
We believe that these integrations with our technology alliance partners enhance the value of our platform to our customers.
Sales and Marketing
Our sales and marketing organizations collaborate to create brand preference, efficiently and effectively generate leads, build a strong sales pipeline and cultivate customer relationships to help drive revenue growth. Our go-to-market strategy consists of a strong thought-leadership program, digital marketing engine and a diversified sales organization designed to efficiently sell to organizations of all sizes.
Sales
We sell our products and services through direct inside and field sales team and indirect channel partner relationships. Our global sales teams focus on both new customer acquisition and up-selling and cross-selling
13
Table of Contents
additional offerings to our existing customers. Our sales teams are organized by geography, consisting of the Americas; Europe, the Middle East and Africa, or EMEA; and Asia Pacific, or APAC, as well as by target organization size. Our inside sales team focuses on small and middle-market transactions, while larger or more complex transactions are generally handled by our globally distributed direct field sales teams. Our highly technical sales engineers help define customer use cases, manage solution evaluations and train channel partners.
We maintain a global channel partner network that complements our sales organization. Our channel partner network expands our geographic sales reach by providing language support and broader distribution capabilities, particularly in EMEA, APAC and Latin America. Our channel partners also provide us with additional leverage by assisting in closing customer transactions as part of larger security purchases, sourcing new prospects and securing maintenance renewals. Our sales force works directly with, and is involved in sales to, substantially all of the end customers of our channel partners, and we sometimes engage a channel partner solely to assist with finalizing a purchase, for example, in the event a customer is working on broader software initiatives with that channel partner.
We intend to continue investing in our international sales organization to continue to drive market penetration. We also have a dedicated sales teams focused on government and education customers, which covers U.S. federal, state and local government, as well as educational entities.
Marketing
We focus our marketing efforts on increasing the strength of the Rapid7 brand, communicating product advantages and business benefits, generating leads for our sales force and channel partners and driving product adoption. We deliver targeted content to demonstrate our thought leadership in security and use digital advertising methods to drive downloads of our free community and trial software, which deliver opportunities to our sales organization. We engage with existing customers to provide community-based education and awareness and to promote expanded use of our software within these customers. We work with our own researchers, as well as the broader IT and security community, to share important information about vulnerabilities and threats. We share that research through our active online community, social media and traditional public relations. In addition, we host regional and national events to engage both customers and prospects, deliver product training and foster community collaboration.
Sales and marketing expense totaled $90.5 million, $67.4 million and $49.0 million for 2016, 2015 and 2014, respectively.
Research and Development
We invest substantial resources in research and development to enhance our core technology platform and products, develop new end market-specific solutions and applications, and conduct product and quality assurance testing. Our technical and engineering team monitors and tests our products on a regular basis, and we maintain a regular release process to refine, update, and enhance our existing products. We also have a team of experienced security researchers who work to keep us abreast of the latest developments in the cyber security landscape. Our research and development teams are distributed globally and are located in our offices in Cambridge, Austin, Los Angeles, Toronto, Dublin and Belfast providing us with a broad, worldwide reach to engineering talent. Research and development expense totaled $48.0 million, $38.7 million and $25.6 million for 2016, 2015 and 2014, respectively.
Our Competition
The market for cyber security solutions is highly fragmented, intensely competitive and constantly evolving. We compete with an array of established and emerging security software and services vendors. With the introduction of new technologies and market entrants, we expect the competitive environment to remain intense going forward. Our competitors include: vulnerability management and assessment vendors, including Qualys and Tenable Network Security; diversified security software and services vendors, including IBM and HP;
14
Table of Contents
compliance and monitoring solutions such as SIEM, including those provided by LogRhythm, Alienvault, and Sumo Logic; machine data analysis tools such as Splunk; security services specialists, including Mandiant (a subsidiary of FireEye); and providers of point solutions that compete with some of the features present in our solutions.
We compete on the basis of a number of factors, including:
| • | product functionality; |
| • | breadth of offerings; |
| • | performance; |
| • | brand name, reputation and customer satisfaction; |
| • | ease of implementation, use and maintenance; |
| • | total cost of ownership; and |
| • | scalability, reliability and security. |
We believe that we compete favorably with respect to all of these factors and that we are well positioned to lead with our focus on data analytics products and professional services.
Intellectual Property
Our future success and competitive position depend in part on our ability to protect our intellectual property and proprietary technologies. To safeguard these rights, we rely on a combination of patents, trademarks, copyrights, trade secrets, employee and third-party nondisclosure agreements, licensing arrangements and other contractual protections to protect our intellectual property in the United States and other jurisdictions.
We have multiple issued patents and a number of registered and unregistered trademarks. We believe that the duration of our issued patents is sufficient when considering the expected lives of our products. We file patent applications to protect our intellectual property and have a number of applications pending in the United States. We require our employees, consultants and other third parties to enter into confidentiality and proprietary rights agreements and control access to software, documentation and other proprietary information. Although we rely on intellectual property rights, including trade secrets, patents, copyrights and trademarks, as well as contractual protections to establish and protect our proprietary rights, we believe that factors such as the technological and creative skills of our personnel, creation of new modules, features and functionality, and frequent enhancements to our solutions are more essential to establishing and maintaining our technology leadership position.
We also license software from third parties for integration into our offerings, including open source software and other software available on commercially reasonable terms. We cannot assure you that such third parties will maintain such software or continue to make it available.
Despite our efforts to protect our proprietary technology and our intellectual property rights, unauthorized parties may attempt to copy or obtain and use our technology to develop products with the same functionality as our solution. Policing unauthorized use of our technology and intellectual property rights is difficult.
We expect that software and other solutions in our industry may be subject to third-party infringement claims as the number of competitors grows and the functionality of products in different industry segments overlaps. Any of these third parties might make a claim of infringement against us at any time.
15
Table of Contents
Employees
As of December 31, 2016, we had 887 full-time employees, including 164 in product delivery and support, 346 in sales and marketing, 251 in research and development and 126 in general and administrative. As of December 31, 2016, we had 669 full-time employees in the United States and 218 full-time employees internationally. None of our U.S. employees are covered by collective bargaining agreements. We believe our employee relations are good and we have not experienced any work stoppages.
Segments
We view our operations and manage our business as one operating segment. See our consolidated financial statements for a discussion of revenues, operating loss, net loss and total assets.
Corporate Information
We were initially incorporated in July 2000 in Delaware. Rapid7 LLC, a limited liability company organized under the laws of the Commonwealth of Massachusetts, was formed in January 2004. In August 2004, pursuant to an exchange agreement among Rapid7 LLC and the stockholders of Rapid7, Inc., the stockholders exchanged their shares in Rapid7, Inc. for equity interests in Rapid7 LLC, after which Rapid7, Inc. was dissolved. In August 2008, Rapid7 LLC was merged with and into Rapid7 LLC, a newly-formed Delaware limited liability company. Rapid7, Inc. was reincorporated in Delaware in October 2011. In a series of transactions in November 2011, equity holders of Rapid7 LLC exchanged their equity interests in Rapid7 LLC for capital stock in Rapid7, Inc. and Rapid7 LLC became a wholly-owned subsidiary of Rapid7, Inc.
Our principal executive offices are located at 100 Summer Street, Boston, Massachusetts. Our telephone number is (617) 247-1717. Our website address is www.rapid7.com.
“Rapid7,” the Rapid7 logo, and other trademarks or service marks of Rapid7, Inc. appearing in this Annual Report on Form 10-K are the property of Rapid7, Inc. This Annual Report on Form 10-K contains additional trade names, trademarks and service marks of others, which are the property of their respective owners. Solely for convenience, trademarks and trade names referred to in this Annual Report on Form 10-K may appear without the ® or TM symbols.
Geographic Information
For a description of our revenue and long-lived assets by geographic location, see Note 14 of the Notes to our Consolidated Financial Statements included in this Annual Report on Form 10-K.
Available Information
Our Annual Report on Form 10-K, Quarterly Reports on Form 10-Q, Current Reports on Form 8-K and amendments to reports filed pursuant to Sections 13(a) and 15(d) of the Securities Exchange Act of 1934, as amended, are made available free of charge on or through our website at investors.rapid7.com as soon as reasonably practicable after such reports are filed with, or furnished to, the SEC. The SEC also maintains a website, www.sec.gov, which contains reports and other information regarding issuers that file electronically with the SEC. The public may read and copy any files with the SEC Public Reference Room at 100 F Street, NE, Washington, DC 20549. The public may obtain information on the operation of the Public Reference Room by calling 1-800-SEC-0330. We are not, however, including the information contained on our website, or information that may be accessed through links on our website, as part of, or incorporating such information by reference into, this Annual Report on Form 10-K.
Our operations and financial results are subject to various risks and uncertainties including those described below. You should consider carefully the risks and uncertainties described below, in addition to other
16
Table of Contents
information contained in this Annual Report on Form 10-K, including our consolidated financial statements and related notes, as well as our other public filings with the Securities and Exchange Commission, or the SEC. The risks and uncertainties described below are not the only ones we face. Additional risks and uncertainties that we are unaware of, or that we currently believe are not material, may also become important factors that adversely affect our business. If any of the following risks or others not specified below materialize, our business, financial condition and results of operations could be materially adversely affected. In that event, the trading price of our common stock could decline.
Risks Related to Our Business and Industry
We are a rapidly growing company, which makes it difficult to evaluate our future prospects and may increase the risk that we will not be successful.
We are a rapidly growing company. Our ability to forecast our future operating results is subject to a number of uncertainties, including our ability to plan for and model future growth. We have encountered and will continue to encounter risks and uncertainties frequently experienced by growing companies in rapidly evolving industries. If our assumptions regarding these uncertainties, which we use to plan our business, are incorrect or change in reaction to changes in our markets, or if we do not address these risks successfully, our operating and financial results could differ materially from our expectations, our business could suffer and the trading price of our common stock may decline.
If we are unable to sustain our revenue growth rate, we may not achieve or maintain profitability in the future.
From the year ended December 31, 2012 to the year ended December 31, 2016, our revenue grew from $46.0 million to $157.4 million, which represents a compounded annual growth rate of approximately 36%. Although we have experienced rapid growth historically and currently have high renewal rates, we may not continue to grow as rapidly in the future and our renewal rates may decline. Any success that we may experience in the future will depend, in large part, on our ability to, among other things:
| • | maintain and expand our customer base; |
| • | increase revenues from existing customers through increased or broader use of our products and professional services within their organizations; |
| • | improve the performance and capabilities of our products through research and development; |
| • | continue to develop our cloud-based solutions; |
| • | maintain the rate at which customers purchase our content subscriptions and maintenance and support; |
| • | continue to successfully expand our business domestically and internationally; and |
| • | successfully compete with other companies. |
If we are unable to maintain consistent revenue or revenue growth, our stock price could be volatile, and it may be difficult to achieve and maintain profitability. You should not rely on our revenue for any prior quarterly or annual periods as any indication of our future revenue or revenue growth.
We have not been profitable historically and may not achieve or maintain profitability in the future.
We have posted a net loss in each year since inception, including net losses of $49.0 million, $49.9 million and $32.6 million in the years ended December 31, 2016, 2015 and 2014, respectively. As of December 31, 2016, we had an accumulated deficit of $389.3 million. While we have experienced significant revenue growth in recent periods, we are not certain whether or when we will obtain a high enough volume of sales of our products and
17
Table of Contents
professional services to sustain or increase our growth or achieve or maintain profitability in the future. We also expect our costs to increase in future periods, which could negatively affect our future operating results if our revenue does not increase. In particular, we expect to continue to expend financial and other resources on:
| • | research and development related to our offerings, including investments in our research and development team; |
| • | sales and marketing, including a significant expansion of our sales organization, both domestically and internationally; |
| • | continued international expansion of our business; |
| • | expansion of our professional services organization; and |
| • | general and administrative expenses as we continue to implement and enhance our administrative, financial and operational systems, procedures and controls. |
These investments may not result in increased revenue or growth in our business. If we are unable to increase our revenue at a rate sufficient to offset the expected increase in our costs, our business, financial position and results of operations will be harmed, and we may not be able to achieve or maintain profitability over the long term. Additionally, we may encounter unforeseen operating expenses, difficulties, complications, delays and other unknown factors that may result in losses in future periods. If our revenue growth does not meet our expectations in future periods, our financial performance may be harmed, and we may not achieve or maintain profitability in the future.
If our products or professional services fail to detect vulnerabilities or incorrectly detect vulnerabilities, or if our products contain undetected errors or defects, our brand and reputation could be harmed, which could have an adverse effect on our business and results of operations.
If our products or professional services fail to detect vulnerabilities in our customers’ cyber security infrastructure, or if our products or professional services fail to identify and respond to new and increasingly complex methods of cyber attacks, our business and reputation may suffer. There is no guarantee that our products or professional services will detect all vulnerabilities, especially in light of the rapidly changing security landscape to which we must respond. Additionally, our products may falsely detect vulnerabilities or threats that do not actually exist. For example, our Metasploit offering relies on information provided by an active community of security researchers who contribute new exploits, attacks and vulnerabilities. If the information from these third parties is inaccurate, the potential for false indications of security vulnerabilities increases. These false positives, while typical in the industry, may impair the perceived reliability of our offerings and may therefore adversely impact market acceptance of our products and professional services and could result in negative publicity, loss of customers and sales and increased costs to remedy any problem.
Our products may also contain undetected errors or defects when first introduced or as new versions are released. We have experienced these errors or defects in the past in connection with new products and product upgrades and we expect that these errors or defects will be found from time to time in the future in new or enhanced products after commercial release. Defects may cause our products to be vulnerable to attacks, cause them to fail to detect vulnerabilities, or temporarily interrupt customers’ networking traffic. Any errors, defects, disruptions in service or other performance problems with our products may damage our customers’ business and could hurt our reputation. If our products or professional services fail to detect vulnerabilities for any reason, we may incur significant costs, the attention of our key personnel could be diverted, our customers may delay or withhold payment to us or elect not to renew or other significant customer relations problems may arise. We may also be subject to liability claims for damages related to errors or defects in our products. A material liability claim or other occurrence that harms our reputation or decreases market acceptance of our products may harm our business and operating results.
18
Table of Contents
An actual or perceived security breach or theft of the sensitive data of one of our customers, regardless of whether the breach is attributable to the failure of our products or professional services, could adversely affect the market’s perception of our offerings and subject us to legal claims.
The market for cyber security data and analytics is new and unproven and may not grow.
We believe our future success will depend in large part on the growth, if any, in the market for cyber security data and analytics. This market is nascent, and as such, it is difficult to predict important market trends, including the potential growth, if any. To date, the majority of enterprise spend on cyber security has been on threat protection products, such as network, endpoint and web security that are designed to stop threats from penetrating corporate networks. Organizations that use these security products may believe that their existing security solutions sufficiently protect access to their sensitive business data. Therefore, they may continue allocating their cyber security budgets to these products and may not adopt our products and professional services in addition to, or in lieu of, such traditional products. Further, sophisticated cyber attackers are skilled at adapting to new technologies and developing new methods of gaining access to organizations’ sensitive business data, and changes in the nature of advanced cyber threats could result in a shift in IT budgets away from products and professional services such as ours. In addition, while recent high visibility attacks on prominent enterprises and governments have increased market awareness of the problem of cyber attacks, if cyber attacks were to decline, or enterprises or governments perceived that the general level of cyber attacks have declined, our ability to attract new customers and expand our sale to existing customers could be materially and adversely affected. If products and professional services such as ours are not viewed by organizations as necessary, or if customers do not recognize the benefit of our offerings as a critical layer of an effective cyber security strategy, our revenue may not grow as quickly as expected, or may decline, and the trading price of our stock could suffer. It is therefore difficult to predict how large the market will be for our solutions.
In addition, it is difficult to predict customer adoption and renewal rates, customer demand for our products and professional services, the size and growth rate of the market for cyber security data analytics, the entry of competitive products or the success of existing competitive products. Any expansion in our market depends on a number of factors, including the cost, performance and perceived value associated with our offerings and those of our competitors. If these offerings do not achieve widespread adoption or there is a reduction in demand for solutions in our market caused by a lack of customer acceptance, technological challenges, competing technologies and products, decreases in corporate spending, weakening economic conditions, or otherwise, it could result in reduced customer orders, early terminations, reduced renewal rates or decreased revenue, any of which would adversely affect our business operations and financial results. You should consider our business and prospects in light of the risks and difficulties we face in this new and unproven market.
If we are unable to successfully hire, train, manage and retain qualified personnel, especially those in sales and marketing and research and development, our business may suffer.
We continue to be substantially dependent on our sales force to obtain new customers and increase sales with existing customers. Our ability to successfully pursue our growth strategy will also depend on our ability to attract, motivate and retain our personnel, especially those in sales, marketing and research and development. We face intense competition for these employees from numerous technology, software and other companies, especially in certain geographic areas in which we operate, and we cannot ensure that we will be able to attract, motivate and/or retain sufficient qualified employees in the future. If we are unable to attract new employees and retain our current employees, we may not be able to adequately develop and maintain new products or professional services or market our existing products or professional services at the same levels as our competitors and we may, therefore, lose customers and market share. Our failure to attract and retain personnel, especially those in sales and marketing and research and development positions for which we have historically had a high turnover rate, could have an adverse effect on our ability to execute our business objectives and, as a result, our ability to compete could decrease, our operating results could suffer and our revenue could decrease. Even if we are able to identify and recruit a sufficient number of new hires, these new hires will require significant training before they achieve full productivity and they may not become productive as quickly as we would like or at all.
19
Table of Contents
Our sales cycle may be unpredictable.
The timing of sales of our offerings is difficult to forecast because of the length and unpredictability of our sales cycle, particularly with large enterprises and with respect to certain of our products. We sell our products primarily to IT departments that are managing a growing set of user and compliance demands, which has increased the complexity of customer requirements to be met and confirmed during the sales cycle and prolonged our sales cycle. Further, the length of time that potential customers devote to their testing and evaluation, contract negotiation and budgeting processes varies significantly, depending on the size of the organization and nature of the product or professional service under consideration. In addition, we might devote substantial time and effort to a particular unsuccessful sales effort, and as a result, we could lose other sales opportunities or incur expenses that are not offset by an increase in revenue, which could harm our business.
Organizations may be reluctant to purchase cyber security data analytics offerings that are cloud-based due to the actual or perceived vulnerability of cloud solutions.
Some organizations have been reluctant to use cloud solutions for cyber security, such as InsightIDR and Logentries, because they have concerns regarding the risks associated with the reliability or security of the technology delivery model associated with this solution. If we or other cloud service providers experience security incidents, breaches of customer data, disruptions in service delivery or other problems, the market for cloud solutions may be negatively impacted, which could harm our business.
If we do not continue to innovate and offer products and professional services that address the dynamic threat landscape, we may not remain competitive, and our revenue and operating results could suffer.
The cyber security market is characterized by rapid technological advances, changes in customer requirements, frequent new product introductions and enhancements and evolving industry standards. Our success also depends, in part, upon our ability to anticipate industry evolution and introduce or acquire new products and professional services to keep pace with technological developments and market requirements both within our industry and in related industries. While we continue to invest significant resources in research and development in order to ensure that our products continue to address the cyber security risks that our customers face, the introduction of products and services embodying new technologies could render our existing products or services obsolete or less attractive to customers. In addition, developing new products and product enhancements is expensive and time consuming, and there is no assurance that such activities will result in significant cost savings, revenue or other expected benefits. If we spend significant time and effort on research and development and are unable to generate an adequate return on our investment, our business and results of operations may be materially and adversely affected. Further, we may not be able to successfully anticipate or adapt to changing technology or customer requirements or the dynamic threat landscape on a timely basis, in a way that sufficiently differentiates us from competing solutions such that customers choose to purchase our solutions. If any of our competitors implement new technologies before we are able to implement them or better anticipate the innovation opportunities in related industries, those competitors may be able to provide more effective or more cost-effective solutions than ours. In addition, we may experience technical problems and additional costs as we introduce new products and product enhancements, deploy future iterations of our products and integrate new products with existing customer systems. If any of these problems were to arise, our business, financial condition and results of operations could be adversely affected.
To date, we have derived a substantial majority of our revenue from customers using our threat exposure management offerings. If we are unable to renew or increase sales of our threat exposure management offerings, or if we are unable to increase sales of our other offerings, our business and operating results could be adversely affected.
Although we have recently introduced new products and professional services, we derive and expect to continue to derive a substantial majority of our revenue from customers using certain of our threat exposure management
20
Table of Contents
offerings, Nexpose and Metasploit. Greater than half of our revenue was attributable to Nexpose in each of our last three fiscal years. As a result, our operating results could suffer due to:
| • | any decline in demand for our threat exposure management offerings; |
| • | failure of our threat exposure management offerings to detect vulnerabilities in our customers’ IT environments; |
| • | the introduction of products and technologies that serve as a replacement or substitute for, or represent an improvement over, our threat exposure management offerings; |
| • | technological innovations or new standards that our threat exposure management offerings do not address; |
| • | sensitivity to current or future prices offered by us or competing solutions; and |
| • | our inability to release enhanced versions of our threat exposure management offerings on a timely basis in response to the dynamic threat landscape. |
Our inability to renew or increase sales of our threat exposure management offerings, including content subscriptions and maintenance and support, or a decline in prices of our threat exposure management offerings would harm our business and operating results more seriously than if we derived significant revenues from a variety of offerings. For example, our Managed Detection and Response (formerly known as “Analytic Response”) and InsightIDR products for user behavior analytics and incident detection and response, respectively, are relatively new, and it is uncertain whether these products will gain market acceptance. We are also investing heavily in the expansion of our security advisory services offerings, which we believe will help drive demand for our other products in addition to being a stand-alone service. Any factor adversely affecting sales of our products or professional services, including release cycles, market acceptance, competition, performance and reliability, reputation and economic and market conditions, could adversely affect our business and operating results.
Our business and growth depend substantially on customers renewing their content subscriptions and maintenance and support agreements with us. Any decline in our customer renewals could adversely affect our future operating results.
Our maintenance and support agreements are sold on a term basis. In addition, we also enter into content subscription agreements for our offerings. In order for us to improve our operating results, it is important that our existing customers renew their content subscription agreements, if applicable, and maintenance and support agreements when the initial contract term expires. Our customers have no obligation to renew their content subscription or maintenance and support agreements with us after the initial terms have expired. Our customers’ renewal rates may decline or fluctuate as a result of a number of factors, including their satisfaction or dissatisfaction with our new or current product offerings, our pricing, the effects of economic conditions, competitive offerings or alterations or reductions in our customers’ spending levels. If our customers do not renew their agreements with us or renew on terms less favorable to us, our revenues and results of operations may be adversely impacted.
If Metasploit were to be used by attackers to exploit vulnerabilities in the cyber security infrastructures of third parties, our reputation and business could be harmed.
Although Metasploit is a penetration testing tool that is intended to allow organizations to test the effectiveness of their cyber security programs, Metasploit has in the past and may in the future be used to exploit vulnerabilities in the cyber security infrastructures of third parties. While we have incorporated certain features into Metasploit to deter misuse, there is no guarantee that these controls will not be circumvented or that Metasploit will only be used defensively or for research purposes. Any actual or perceived security breach, malicious intrusion or theft of sensitive data in which Metasploit is believed to have been used could adversely
21
Table of Contents
affect perception of, and demand for, our offerings. Further, the identification of new exploits and vulnerabilities by the Metasploit community may enhance the knowledge base of cyber attackers or enable them to undertake new forms of attacks. If any of the foregoing were to occur, we could suffer negative publicity and loss of customers and sales, as well as possible legal claims.
We face intense competition in our market.
The market for cyber security solutions is highly fragmented, intensely competitive and constantly evolving. We compete with an array of established and emerging security software and services vendors. With the introduction of new technologies and market entrants, we expect the competitive environment to remain intense going forward. Our competitors include: vulnerability management and assessment vendors, including Qualys and Tenable Network Security; diversified security software and services vendors, including IBM and HP; legacy compliance and monitoring solutions such as SIEM, provided by vendors including LogRhythm, Alienvault and Sumo Logic; machine data analysis tools such as those provided by Splunk; security services specialists, including Mandiant (a subsidiary of FireEye); and providers of point solutions that compete with some of the features present in our solutions.
Some of our actual and potential competitors have advantages over us, such as longer operating histories, significantly greater financial, technical, marketing or other resources, stronger brand and business user recognition, larger and more mature intellectual property portfolios and broader global distribution and presence. In addition, our industry is evolving rapidly and is becoming increasingly competitive. Larger and more established companies may focus on cyber security and could directly compete with us. Smaller companies could also launch new products and services that we do not offer and that could gain market acceptance quickly.
Our competitors may be able to respond more quickly and effectively than we can to new or changing opportunities, technologies, standards or customer requirements. With the introduction of new technologies, the evolution of our offerings and new market entrants, we expect competition to intensify in the future. In addition, some of our larger competitors have substantially broader product offerings and can bundle competing products and services with other software offerings. As a result, customers may choose a bundled product offering from our competitors, even if individual products have more limited functionality than our solutions. These competitors may also offer their products at a lower price as part of this larger sale, which could increase pricing pressure on our offerings and cause the average sales price for our offerings to decline. These larger competitors are also often in a better position to withstand any significant reduction in capital spending, and will therefore not be as susceptible to economic downturns.
Furthermore, our current and potential competitors may establish cooperative relationships among themselves or with third parties that may further enhance their resources and product and services offerings in the markets we address. In addition, current or potential competitors may be acquired by third parties with greater available resources. As a result of such relationships and acquisitions, our current or potential competitors might be able to adapt more quickly to new technologies and customer needs, devote greater resources to the promotion or sale of their products and services, initiate or withstand substantial price competition, take advantage of other opportunities more readily or develop and expand their product and service offerings more quickly than we do. For all of these reasons, we may not be able to compete successfully against our current or future competitors, or we may be required to expend significant resources in order to remain competitive. If our competitors are more successful than we are in developing new product and service offerings or in attracting and retaining customers, our business, financial condition and results of operations could be adversely affected.
A component of our growth strategy is dependent on our continued international expansion, which adds complexity to our operations.
We market and sell our products and professional services throughout the world and have personnel in many parts of the world. For the year ended December 31, 2016, international operations generated 14% of our
22
Table of Contents
revenue. Our growth strategy is dependent, in part, on our continued international expansion. We expect to conduct a significant amount of our business with organizations that are located outside the United States, particularly in Europe and Asia. We cannot assure you that our expansion efforts into international markets will be successful in creating further demand for our products and professional services or in effectively selling our products and professional services in the international markets that we enter. Our current international operations and future initiatives will involve a variety of risks, including:
| • | increased management, infrastructure and legal costs associated with having international operations; |
| • | reliance on channel partners; |
| • | trade and foreign exchange restrictions; |
| • | economic or political instability or uncertainty in foreign markets and around the world, such as related to the United Kingdom’s referendum in June 2016 in which voters approved an exit from the European Union, commonly referred to as “Brexit”; |
| • | foreign currency exchange rate fluctuations; |
| • | greater difficulty in enforcing contracts, accounts receivable collection and longer collection periods; |
| • | changes in regulatory requirements, including, but not limited to data privacy, data protection and data security regulations; |
| • | difficulties and costs of staffing and managing foreign operations; |
| • | the uncertainty and limitation of protection for intellectual property rights in some countries; |
| • | costs of compliance with foreign laws and regulations and the risks and costs of non-compliance with such laws and regulations; |
| • | costs of compliance with U.S. laws and regulations for foreign operations, including the Foreign Corrupt Practices Act, import and export control laws, tariffs, trade barriers, economic sanctions and other regulatory or contractual limitations on our ability to sell or provide our solutions in certain foreign markets, and the risks and costs of non-compliance; |
| • | heightened risks of unfair or corrupt business practices in certain geographies and of improper or fraudulent sales arrangements that may impact financial results and result in restatements of, and irregularities in, financial statements; |
| • | the potential for political unrest, acts of terrorism, hostilities or war; |
| • | management communication and integration problems resulting from cultural differences and geographic dispersion; |
| • | costs associated with language localization of our products; and |
| • | costs of compliance with multiple and possibly overlapping tax structures. |
Our business, including the sales of our products and professional services by us and our channel partners, may be subject to foreign governmental regulations, which vary substantially from country to country and change from time to time. Our failure, or the failure by our channel partners, to comply with these regulations could adversely affect our business. Further, in many foreign countries it is common for others to engage in business practices that are prohibited by our internal policies and procedures or U.S. regulations applicable to us. Although we have implemented policies and procedures designed to comply with these laws and policies, there can be no assurance that our employees, contractors, channel partners and agents have complied, or will comply, with these laws and policies. Violations of laws or key control policies by our employees, contractors, channel partners or agents could result in delays in revenue recognition, financial reporting misstatements, fines, penalties or the prohibition of the importation or exportation of our products and could have a material adverse effect on
23
Table of Contents
our business and results of operations. If we are unable to successfully manage the challenges of international expansion and operations, our business and operating results could be adversely affected.
We are also monitoring developments related to Brexit, which could have significant implications for our business. Brexit could lead to economic and legal uncertainty, including significant volatility in global stock markets and currency exchange rates, and differing laws and regulations as the United Kingdom determines which European Union laws to replace or replicate. Any of these effects of Brexit, among others, could adversely affect our operations in the United Kingdom and our financial results.
As a cyber security provider, we are a target of cyber attacks that could adversely impact our reputation and operating results.
We sell cyber security and data analytics products. As a result, we have been and will be a target of cyber attacks designed to impede the performance of our products, penetrate our network security or the security of our cloud platform or our internal systems, or that of our customers, misappropriate proprietary information and/or cause interruptions to our services. For example, because Metasploit serves as an introduction to hacking for many individuals, a successful cyber attack on us may be perceived as a victory for the cyber attacker, thereby increasing the likelihood that we may be a target of cyber attacks, even absent financial motives. Further, if our systems are breached, attackers could learn critical information about how our products operate to help protect our customers’ IT infrastructures from cyber risk, thereby making our customers more vulnerable to cyber attacks. In addition, if actual or perceived breaches of our network security occur, they could adversely affect the market perception of our products, negatively affecting our reputation, and may expose us to the loss of our proprietary information or information belonging to our customers, investigations or litigation and possible liability, including injunctive relief and monetary damages. Such security breaches could also divert the efforts of our technical and management personnel. In addition, such security breaches could impair our ability to operate our business and provide products to our customers. If this happens, our reputation could be harmed, our revenue could decline and our business could suffer.
We are dependent on the continued services and performance of our senior management and other key employees, the loss of any of whom could adversely affect our business, operating results and financial condition.
Our future performance depends on the continued services and contributions of our senior management, particularly Corey Thomas, our President and Chief Executive Officer, and other key employees to execute on our business plan and to identify and pursue new opportunities and product innovations. We maintain key man insurance on Mr. Thomas, but do not do so for any of our other executive officers or key employees. From time to time, there may be changes in our senior management team resulting from the termination or departure of our executive officers and key employees. Our senior management and key employees are generally employed on an at-will basis, which means that they could terminate their employment with us at any time. The loss of the services of our senior management, particularly Mr. Thomas, or other key employees for any reason could significantly delay or prevent our development or the achievement of our strategic objectives and harm our business, financial condition and results of operations.
Our business and operations are experiencing rapid growth, and if we do not appropriately manage our future growth, or are unable to scale our systems and processes, our operating results may be negatively affected.
We are a rapidly growing company. To manage future growth effectively we will need to continue to improve and expand our internal information technology systems, financial infrastructure, and operating and administrative systems and controls, which we may not be able to do efficiently, in a timely manner or at all. Any future growth would add complexity to our organization and require effective coordination across our organization. Failure to manage any future growth effectively could result in increased costs, harm our results of operations and lead to customers or investors losing confidence in our internal systems and processes, which could harm our results of operations and stock price.
24
Table of Contents
Our quarterly operating results may vary from period to period, which could result in our failure to meet expectations with respect to operating results and cause the trading price of our stock to decline.
Our operating results, including the levels of our revenue, billings, cash flow and deferred revenue, have historically varied from period to period, and we expect that they will continue to do so as a result of a number of factors, many of which are outside of our control, including:
| • | the level of demand for our products and professional services; |
| • | customer renewal rates and ability to attract new customers; |
| • | the extent to which customers purchase additional products, including content subscriptions and maintenance and support related to our Nexpose, Metasploit and AppSpider products, or professional services; |
| • | the ability to successfully grow our InsightIDR sales; |
| • | the level of perceived threats to organizations’ cyber security; |
| • | network outages, security breaches, technical difficulties or interruptions with our products; |
| • | changes in the growth rate of the markets in which we compete; |
| • | variations in our billings and sales of our products and services due to seasonality and customer demand; |
| • | the announcement or adoption of new regulations and policy mandates or changes to existing regulations and policy mandates; |
| • | the timing and success of new product or professional service introductions by us or our competitors or any other changes in the competitive landscape of our industry, including consolidation among our competitors; |
| • | the introduction or adoption of new technologies that compete with our offerings; |
| • | the mix of our products and professional services sold during a period; |
| • | decisions by potential customers to purchase cyber security products or services from other vendors; |
| • | the amount and timing of operating costs and capital expenditures related to the operations and expansion of our business; |
| • | the timing of sales commissions relative to the recognition of revenue and the timing of revenue recognition generally; |
| • | price competition; |
| • | our ability to successfully manage and integrate any future acquisitions of businesses, including without limitation the amount and timing of expenses and potential future charges for impairment of goodwill from acquired companies; |
| • | our ability to increase, retain and incentivize the channel partners that market and sell our products and professional services; |
| • | our continued international expansion and associated exposure to changes in foreign currency exchange rates, including any fluctuations caused by uncertainties relating to Brexit; |
| • | the amount and timing of operating expenses related to the maintenance and expansion of our business, operations and infrastructure; |
| • | unforeseen litigation and intellectual property infringement; |
| • | the announcement or adoption of new regulations and policy mandates or changes to existing regulations and policy mandates; |
25
Table of Contents
| • | the strength of regional, national and global economies; |
| • | the impact of natural disasters or manmade problems such as terrorism or war; and |
| • | future accounting pronouncements or changes in our accounting policies. |
Each factor above or discussed elsewhere in this Annual Report on Form 10-K or the cumulative effect of some of these factors may result in fluctuations in our operating results. This variability and unpredictability could result in our failure to meet expectations with respect to operating results, or those of securities analysts or investors, for a particular period. If we fail to meet or exceed expectations for our operating results for these or any other reasons, the market price of our stock could fall and we could face costly lawsuits, including securities class action suits.
We recognize substantially all of our revenue ratably over the term of our agreements with customers and, as a result, downturns or upturns in sales may not be immediately reflected in our operating results.
We recognize substantially all of our revenue ratably over the terms of our agreements with customers, which generally occurs over a one to three-year period. As a result, a substantial portion of the revenue that we report in each period will be derived from the recognition of deferred revenue relating to agreements entered into during previous periods. Consequently, a decline in new sales or renewals in any one period may not be immediately reflected in our revenue results for that period. This decline, however, will negatively affect our revenue in future periods. Accordingly, the effect of significant downturns in sales and market acceptance of our products and potential changes in our rate of renewals may not be fully reflected in our results of operations until future periods. Our model also makes it difficult for us to rapidly increase our revenue through additional sales in any period, as revenue from new customers generally will be recognized over the term of the applicable agreement.
We also intend to increase our investment in research and development, sales and marketing, and general and administrative functions and other areas to grow our business. We are likely to recognize the costs associated with these increased investments earlier than some of the anticipated benefits and the return on these investments may be lower, or may develop more slowly, than we expect, which could adversely affect our operating results.
We may be unable to rapidly and efficiently adjust our cost structure in response to significant revenue declines, which could adversely affect our operating results.
Our brand, reputation and ability to attract, retain and serve our customers are dependent in part upon the reliable performance of our products and network infrastructure.
Our brand, reputation and ability to attract, retain and serve our customers are dependent in part upon the reliable performance of our products and network infrastructure. We have experienced, and may in the future experience, disruptions, outages and other performance problems due to a variety of factors, including infrastructure changes, human or software errors, capacity constraints and fraud or security attacks. In some instances, we may not be able to identify the cause or causes of these performance problems within an acceptable period of time.
We utilize third-party data centers located in Boston, Massachusetts, in addition to operating and maintaining certain elements of our own network infrastructure. We also utilize Amazon Web Services for our InsightIDR and Logentries infrastructure. Some elements of this complex system are operated by third parties that we do not control and that could require significant time to replace. We expect this dependence on third parties to continue. More specifically, certain of our products, in particular our Managed Vulnerability Management (Nexpose), InsightIDR and Logentries products, are hosted on Amazon Web Services, which provides us with computing and storage capacity. Interruptions in our systems or the third-party systems on which we rely, whether due to system failures, computer viruses, physical or electronic break-ins, or other factors, could affect the security or availability of our products, network infrastructure and website.
26
Table of Contents
Prolonged delays or unforeseen difficulties in connection with adding capacity or upgrading our network architecture when required may cause our service quality to suffer. Problems with the reliability or security of our systems could harm our reputation. Damage to our reputation and the cost of remedying these problems could negatively affect our business, financial condition, and operating results.
Additionally, our existing data center facilities and third-party hosting providers have no obligations to renew their agreements with us on commercially reasonable terms or at all, and certain of the agreements governing these relationships may be terminated by either party at any time. If we are unable to maintain or renew our agreements with these providers on commercially reasonable terms or if in the future we add additional data center facilities or third-party hosting providers, we may experience costs or downtime as we transition our operations.
Any disruptions or other performance problems with our products could harm our reputation and business and may damage our customers’ businesses. Interruptions in our service delivery might reduce our revenue, cause us to issue credits to customers, subject us to potential liability and cause customers to not renew their purchases or our products.
If we fail to manage our operations infrastructure, our customers may experience service outages and/or delays.
Our future growth is dependent upon our ability to continue to meet the expanding needs of our customers and to attract new customers. As existing customers gain more experience with our products, they may broaden their reliance on our products, which will require that we expand our operations infrastructure. We also seek to maintain excess capacity in our operations infrastructure to facilitate the rapid provision of new customer deployments. In addition, we need to properly manage our technological operations infrastructure in order to support changes in hardware and software parameters and the evolution of our products, all of which require significant lead time. If we do not accurately predict our infrastructure requirements, our existing customers may experience service outages that may subject us to financial penalties, financial liabilities and customer losses. If our operations infrastructure fails to keep pace with increased sales, customers may experience delays as we seek to obtain additional capacity, which could adversely affect our reputation and our revenue.
If our products fail to help our customers achieve and maintain compliance with regulations and/or industry standards, our revenue and operating results could be harmed.
We generate a portion of our revenue from our threat exposure management offerings that help organizations achieve and maintain compliance with regulations and industry standards both domestically and internationally. For example, many of our customers subscribe to our threat exposure management offerings to help them comply with the security standards developed and maintained by the Payment Card Industry Security Standards Council, or the PCI Council, which apply to companies that process, transmit or store cardholder data. In addition, our threat exposure management offerings are used by customers in the health care industry to help them comply with numerous federal and state laws and regulations related to patient privacy. In particular, the Health Insurance Portability and Accountability Act of 1996, or HIPAA, and the 2009 Health Information Technology for Economic and Clinical Health Act include privacy standards that protect individual privacy by limiting the uses and disclosures of individually identifiable health information and implementing data security standards. The foregoing and other state, federal and international legal and regulatory regimes may affect our customers’ requirements for, and demand for, our products and professional services. Governments and industry organizations, such as the PCI Council, may also adopt new laws, regulations or requirements, or make changes to existing laws or regulations, that could impact the demand for, or value of, our products. If we are unable to adapt our products to changing legal and regulatory standards or other requirements in a timely manner, or if our products fail to assist with, or expedite, our customers’ cyber security defense and compliance efforts, our customers may lose confidence in our products and could switch to products offered by our competitors, or threaten or bring legal actions against us. In addition, if laws, regulations or standards related to data security,
27
Table of Contents
vulnerability management and other IT security and compliance requirements are relaxed or the penalties for non-compliance are changed in a manner that makes them less onerous, our customers may view government and industry regulatory compliance as less critical to their businesses, and our customers may be less willing to purchase our products. In any of these cases, our revenue and operating results could be harmed.
In addition, government and other customers may require our products to comply with certain privacy, security or other certifications and standards. If our products are late in achieving or fail to achieve or maintain compliance with these certifications and standards, or our competitors achieve compliance with these certifications and standards, we may be disqualified from selling our products to such customers, or may otherwise be at a competitive disadvantage, either of which would harm our business, results of operations, and financial condition.
If our customers are unable to implement our products successfully, customer perceptions of our offerings may be impaired or our reputation and brand may suffer.
Our products are deployed in a wide variety of IT environments, including large-scale, complex infrastructures. Some of our customers have experienced difficulties implementing our products in the past and may experience implementation difficulties in the future. If our customers are unable to implement our products successfully, customer perceptions of our offerings may be impaired or our reputation and brand may suffer.
In addition, in order for our products to achieve their functional potential, our products must effectively integrate into our customers’ IT infrastructures, which have different specifications, utilize varied protocol standards, deploy products from multiple different vendors and contain multiple layers of products that have been added over time. Our customers’ IT infrastructures are also dynamic, with a myriad of devices and endpoints entering and exiting the customers’ IT systems on a regular basis, and our products must be able to effectively adapt to and track these changes.
Any failure by our customers to appropriately implement our products or any failure of our products to effectively integrate and operate within our customers’ IT infrastructures could result in customer dissatisfaction, impact the perceived reliability of our products, result in negative press coverage, negatively affect our reputation and harm our financial results.
Recent and future acquisitions could disrupt our business and harm our financial condition and operating results.
In order to remain competitive, we have in the past and may in the future seek to acquire additional businesses, products or technologies. The environment for acquisitions in our industry is very competitive and acquisition candidate purchase prices will likely exceed what we would prefer to pay. We also may not find suitable acquisition candidates, and acquisitions we complete may be unsuccessful.
Achieving the anticipated benefits of future acquisitions will depend in part upon whether we can integrate acquired operations, products and technology in a timely and cost-effective manner. The integration process of a new business or technology requires, among other things, coordination of administrative, sales and marketing, accounting and finance functions, and expansion of information and management systems. Integration of any future acquisition may prove to be difficult due to the necessity of coordinating geographically separate organizations and integrating personnel with disparate business backgrounds and accustomed to different corporate cultures. The acquisition and integration processes are complex, expensive and time consuming, and may cause an interruption of, or loss of momentum in, product development, sales activities and operations of both companies. Further, we may be unable to retain key personnel of an acquired company following the acquisition. If we are unable to effectively execute or integrate acquisitions, our business, financial condition and operating results could be adversely affected.
28
Table of Contents
In addition, we may only be able to conduct limited due diligence on an acquired company’s operations, or may discover that the products or technology acquired were not as capable as we thought based upon the initial or limited due diligence. Following an acquisition, we may be subject to unforeseen liabilities arising from an acquired company’s past or present operations and these liabilities may be greater than the warranty and indemnity limitations that we negotiate. Any unforeseen liability that is greater than these warranty and indemnity limitations could have a negative impact on our financial condition.
If we are unable to maintain successful relationships with our channel partners, our business operations, financial results and growth prospects could be adversely affected.
Our success is dependent in part upon establishing and maintaining relationships with a variety of channel partners that we utilize to extend our geographic reach and market penetration. We anticipate that we will continue to rely on these partners in order to help facilitate sales of our offerings as part of larger purchases in the United States and to grow our business internationally. For 2016 and 2015, we derived approximately 37% and 39%, respectively, of our revenue from sales of products and professional services through channel partners, and the percentage of revenue derived from channel partners may increase in future periods. Our agreements with our channel partners are non-exclusive and do not prohibit them from working with our competitors or offering competing solutions, and some of our channel partners may have more established relationships with our competitors. If our channel partners choose to place greater emphasis on products of their own or those offered by our competitors or do not effectively market and sell our products and professional services, our ability to grow our business and sell our products and professional services, particularly in key international markets, may be adversely affected. In addition, our failure to recruit additional channel partners, or any reduction or delay in their sales of our products and professional services or conflicts between channel sales and our direct sales and marketing activities may harm our results of operations. Finally, even if we are successful, our relationships with channel partners may not result in greater customer usage of our products and professional services or increased revenue.
Failure to maintain high-quality customer support could have a material adverse effect on our business.
Once our products are deployed within our customers’ networks, our customers depend on our technical and other customer support services to resolve any issues relating to the implementation and maintenance of our products. If we do not effectively assist our customers in deploying our products, help our customers quickly resolve post-deployment issues or provide effective ongoing support, our ability to renew or sell additional products or professional services to existing customers would be adversely affected and our reputation with potential customers could be damaged. Further, to the extent that we are unsuccessful in hiring, training and retaining adequate technical and customer success personnel, our ability to provide adequate and timely support to our customers will be negatively impacted, and our customers’ satisfaction with our offerings will be adversely affected.
We rely on third-party software to operate certain functions of our business.
We rely on software vendors to operate certain critical functions of our business, including financial management and human resource management. If these services become unavailable due to extended outages or interruptions or because they are no longer available on commercially reasonable terms or prices, our expenses could increase, our ability to manage our finances could be interrupted and our processes for managing sales of our solutions and supporting our customers could be impaired until equivalent services, if available, are identified, obtained and integrated, all of which could harm our business.
We use third-party software and data that may be difficult to replace or that may cause errors or failures of our solutions, which could lead to lost customers or harm to our reputation and our operating results.
We license third-party software and security and compliance data from various third parties that are used in our solutions in order to deliver our offerings. In the future, this software or data may not be available to us on
29
Table of Contents
commercially reasonable terms, or at all. Any loss of the right to use any of this software or data could result in delays in the provisioning of our offerings until equivalent technology or data is either developed by us, or, if available, is identified, obtained and integrated, which could harm our business. In addition, any errors or defects in or failures of this third-party software could result in errors or defects in our products or cause our products to fail, which could harm our business and be costly to correct. Many of these providers attempt to impose limitations on their liability for such errors, defects or failures, and if enforceable, we may have additional liability to our customers or third-party providers that could harm our reputation and increase our operating costs.
We will need to maintain our relationships with third-party software and data providers, and to obtain software and data from such providers that do not contain errors or defects. Any failure to do so could adversely impact our ability to deliver effective solutions to our customers and could harm our operating results.
Our products contain third-party open source software components, and our failure to comply with the terms of the underlying open source software licenses could restrict our ability to sell our products.
Our products contain software licensed to us by third parties under so-called “open source” licenses, including the GNU General Public License, or GPL, the GNU Lesser General Public License, or LGPL, the BSD License, the Apache License and others. From time to time, there have been claims against companies that distribute or use open source software in their products and services, asserting that such open source software infringes the claimants’ intellectual property rights. We could be subject to suits by parties claiming that what we believe to be licensed open source software infringes their intellectual property rights. Use and distribution of open source software may entail greater risks than use of third-party commercial software, as open source licensors generally do not provide warranties or other contractual protections regarding infringement claims or the quality of the code. In addition, certain open source licenses require that source code for software programs that are subject to the license be made available to the public and that any modifications or derivative works to such open source software continue to be licensed under the same terms.
Although we monitor our use of open source software in an effort both to comply with the terms of the applicable open source licenses and to avoid subjecting our products to conditions we do not intend, the terms of many open source licenses have not been interpreted by U.S. courts, and there is a risk that these licenses could be construed in a way that could impose unanticipated conditions or restrictions on our ability to commercialize our products. The terms of certain open source licenses require us to release the source code of our applications and to make our applications available under those open source licenses if we combine or distribute our applications with open source software in a certain manner. In the event that portions of our applications are determined to be subject to an open source license, we could be required to publicly release the affected portions of our source code, re-engineer all, or a portion of, those applications or otherwise be limited in the licensing of our applications. Disclosing our proprietary source code could allow our competitors to create similar products with lower development effort and time and ultimately, could result in a loss of sales for us. Disclosing the source code of our proprietary software could also make it easier for cyber attackers and other third parties to discover vulnerabilities in or to defeat the protections of our products, which could result in our products failing to provide our customers with the security they expect. Any of these events could have a material adverse effect on our business, operating results and financial condition.
Our technology alliance partnerships expose us to a range of business risks and uncertainties that could have a material adverse impact on our business and financial results.
We have entered, and intend to continue to enter, into technology alliance partnerships with third parties to support our future growth plans, including with certain of our actual or potential competitors. For example, through these technology alliance partnerships, we integrate with certain third-party application program interfaces, or APIs, which enhance our data collection capabilities in our customers’ IT environments. If these third parties no longer allow us to integrate with their APIs, or if we determine not to maintain these integrations, the functionality of our products may be reduced and our products may not be as marketable to certain potential
30
Table of Contents
customers. Technology alliance partnerships require significant coordination between the parties involved, particularly if a partner requires that we integrate its products with our products. Further, we have invested and will continue to invest significant time, money and resources to establish and maintain relationships with our technology alliance partners, but we have no assurance that any particular relationship will continue for any specific period of time, result in new offerings that we can effectively commercialize or result in enhancements to our existing offerings. In addition, while we believe that entering into technology alliance partnerships with certain of our actual or potential competitors is currently beneficial to our competitive position in the market, such partnerships may also give our competitors insight into our offerings that they may not otherwise have, thereby allowing them to compete more effectively against us.
The continued utility of Metasploit depends in part on the continued contributions from security researchers.
Our Metasploit product relies on information provided by an active community of security researchers who contribute new exploits, attacks and vulnerabilities. We expect that the continued contributions from these third parties will both enhance the robustness of Metasploit and also support our sales and marketing efforts. However, to the extent that the information provided by these third parties is inaccurate or malicious, the potential for false indications of security vulnerabilities and susceptibility to attack increases, which could adversely impact market acceptance of our products and professional services and could result in negative publicity, loss of customers and sales and increased costs to remedy any problem. Further, to the extent that our community of third parties is reduced in size or participants become less active, we may lose valuable insight into the dynamic threat landscape and our ability to quickly respond to new exploits, attacks and vulnerabilities may be reduced.
A portion of our revenue is generated by sales to government entities, which are subject to a number of challenges and risks.
Selling to government entities can be highly competitive, expensive and time consuming, and often requires significant upfront time and expense without any assurance that we will win a sale. Government demand and payment for our products and professional services may also be impacted by public sector budgetary cycles and funding authorizations, with funding reductions or delays adversely affecting public sector demand for our offerings. Government entities also have heightened sensitivity surrounding the purchase of cyber security solutions due to the critical importance of their IT infrastructures, the nature of the information contained within those infrastructures and the fact that they are highly-visible targets for cyber attacks. Accordingly, increasing sales of our products and professional services to government entities may be more challenging than selling to commercial organizations. Further, in the course of providing our products and professional services to government entities, our employees and those of our channel partners may be exposed to sensitive government information. Any failure by us or our channel partners to safeguard and maintain the confidentiality of such information could subject us to liability and reputational harm, which could materially and adversely affect our results of operations and financial performance.
We are exposed to fluctuations in currency exchange rates, which could negatively affect our financial condition and results of operations.
Our reporting currency is the U.S. dollar and we generate a majority of our revenue in U.S. dollars. However, for the year ended December 31, 2016, we incurred approximately 13% of our expenses outside of the United States in foreign currencies, primarily the pound sterling (GBP) and Euro, principally with respect to salaries and related personnel expenses associated with our sales and research and development operations. Additionally, for the year ended December 31, 2016, approximately 5% of our revenue was generated in foreign currencies. Accordingly, changes in exchange rates may have an adverse effect on our business, operating results and financial condition. The exchange rate between the U.S. dollar and foreign currencies has fluctuated substantially in recent years and may continue to fluctuate substantially in the future. To date, we have not engaged in any hedging strategies, and any such strategies, such as forward contracts, options and foreign exchange swaps related to transaction exposures that we may implement to mitigate this risk may not eliminate our exposure to foreign exchange fluctuations.
31
Table of Contents
Changes in financial accounting standards may adversely impact our reported results of operations.
A change in accounting standards or practices, in particular with respect to revenue recognition, could harm our operating results and may even affect our reporting of transactions completed before the change is effective. New accounting pronouncements and varying interpretations of accounting pronouncements have occurred and may occur in the future. Changes to existing rules or the questioning of current practices may harm our operating results or the way we conduct our business.
We may require additional capital to support business growth, and this capital might not be available on acceptable terms, if at all.
We intend to continue to make investments to support our business growth and may require additional funds to respond to business challenges, including the need to develop new features or enhance our products, improve our operating infrastructure or acquire complementary businesses and technologies. Accordingly, we may need to engage in equity or debt financings to secure additional funds. If we raise additional funds through future issuances of equity or convertible debt securities, our existing stockholders could suffer significant dilution, and any new equity securities we issue could have rights, preferences and privileges superior to those of holders of our common stock. Any debt financing that we may secure in the future could involve restrictive covenants relating to our capital raising activities and other financial and operational matters, which may make it more difficult for us to obtain additional capital and to pursue business opportunities, including potential acquisitions. We may not be able to obtain additional financing on terms favorable to us, if at all. If we are unable to obtain adequate financing or financing on terms satisfactory to us when we require it, our ability to continue to support our business growth and to respond to business challenges could be significantly impaired, and our business may be adversely affected.
Risks Related to Government Regulation, Data Collection, Intellectual Property, Litigation and Catastrophic Events
We are subject to governmental export and import controls that could impair our ability to compete in international markets and/or subject us to liability if we are not in compliance with applicable laws.
Like other U.S.-based IT security products, our products are subject to U.S. export control and import laws and regulations, including the U.S. Export Administration Regulations and various economic and trade sanctions regulations administered by the U.S. Treasury Department’s Office of Foreign Assets Control. Exports of these products must be made in compliance with these laws and regulations. If we were to fail to comply with these laws and regulations, we and certain of our employees could be subject to substantial civil and criminal penalties, including fines for our company and responsible employees or managers, and, in extreme cases, incarceration of responsible employees and managers and the possible loss of export privileges. Complying with export control laws and regulations, including obtaining the necessary licenses or authorizations, for a particular sale may be time-consuming, is not guaranteed and may result in the delay or loss of sales opportunities. Changes in export or import laws and regulations, shifts in the enforcement or scope of existing laws and regulations, or changes in the countries, governments, persons, products or services targeted by such laws and regulations, could also result in decreased use of our products by, or in our decreased ability to export or sell our products to, existing or potential customers. A decreased use of our products or limitation on our ability to export or sell our products could adversely affect our business, financial condition and results of operations.
We also incorporate encryption technology into our products. These encryption products may be exported outside of the United States only with the required export authorizations, including by a license, a license exception or other appropriate government authorizations, including the filing of a product classification request. We previously deployed certain of our Metasploit products prior to obtaining the appropriate export authorizations. As such, we did not fully comply with applicable encryption controls in the U.S. Export Administration Regulations. Further, U.S. export control laws and economic sanctions prohibit the shipment of certain products and services to U.S. embargoed or sanctioned countries, governments or persons. Although we take precautions
32
Table of Contents
to prevent our products from being provided to those subject to U.S. sanctions, such measures may be circumvented. We are aware of previous exports in the form of downloads of certain of our Metasploit products by persons and organizations that appear to be located in countries that are the subject of U.S. embargoes, and by certain other persons and organizations without the requisite export authorizations. In September 2014, we initiated and filed a voluntary self-disclosure with the U.S. Department of Commerce’s Bureau of Industry and Security, or BIS, concerning our previous failure to obtain required authorizations for certain exports, as well as historical exports of free and trial software to embargoed countries. In March and August 2015, we filed supplements to the voluntary self-disclosure to BIS containing additional information regarding unauthorized exports. Also in March 2015, we filed a voluntary self-disclosure with the U.S. Department of Treasury’s Office of Foreign Assets Control, or OFAC, concerning exports of free and trial versions of our Metasploit products to embargoed countries, specifically Cuba, Iran, Sudan and Syria. As these transactions involved free downloads of our software, we did not derive any revenue from such transactions. On May 22, 2015, OFAC determined not to pursue a civil monetary penalty against us and issued us a Cautionary Letter to resolve our voluntary self-disclosure regarding the free downloads in embargoed countries. On January 12, 2017, BIS determined not to pursue a civil monetary penalty against us and issued us a warning letter to resolve our voluntary self-disclosure regarding our previous failure to obtain required authorizations for certain exports, as well as historical exports of free and trial software to embargoed countries.
In addition, various countries regulate the import and domestic use of certain encryption technology, including through import permitting and licensing requirements, and have enacted laws that could limit our ability to distribute our products or could limit our customers’ ability to implement our products in those countries.
Encryption products and the underlying technology may also be subject to export control restrictions. Governmental regulation of encryption technology and regulation of imports or exports of encryption products, or our failure to obtain required import or export approval for our products, when applicable, could harm our international sales and adversely affect our revenue. Compliance with applicable laws and regulations regarding the export and import of our products, including with respect to new products or changes in existing products, may create delays in the introduction of our products in international markets, prevent our customers with international operations from deploying our products globally or, in some cases, could prevent the export or import of our products to certain countries, governments, entities or persons altogether.
Finally, there are currently multinational efforts underway as part of the Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies, or the Wassenaar Arrangement, to impose additional restrictions on certain cyber security products. Such controls have been implemented by many Wassenaar members, but are not currently in effect in the United States and may undergo substantial modification before becoming effective. To implement the controls under the Wassenaar Arrangement in the United States, BIS would have to amend the EAR. Such amendments could include changes that impose new licensing, approval and other requirements on our commercial Metasploit products and thereby put us at a disadvantage in competing for international sales. We are closely monitoring the potential implications of the Wassenaar Arrangement on the commercial versions of Metasploit, and are actively working with BIS and other U.S. government stakeholders in connection with the implementation of the controls under the Wassenaar Arrangement.
Failure to comply with governmental laws and regulations could harm our business.
Our business is subject to regulation by various federal, state, local and foreign governments. In certain jurisdictions, these regulatory requirements may be more stringent than those in the United States. Noncompliance with applicable regulations or requirements could subject us to investigations, sanctions, mandatory product recalls, enforcement actions, disgorgement of profits, fines, damages, civil and criminal penalties, injunctions or other collateral consequences. If any governmental sanctions are imposed, or if we do not prevail in any possible civil or criminal litigation, our business, results of operations, and financial condition could be materially adversely affected. In addition, responding to any action will likely result in a significant
33
Table of Contents
diversion of management’s attention and resources and an increase in professional fees. Enforcement actions and sanctions could harm our business, reputation, results of operations and financial condition.
Because our products collect and store user and related information, domestic and international privacy and cyber security concerns, and other laws and regulations, could result in additional costs and liabilities to us or inhibit sales of our products.
We, and our customers, are subject to a number of domestic and international laws and regulations that apply to online services and the internet generally. These laws, rules and regulations address a range of issues including data privacy and cyber security, and restrictions or technological requirements regarding the collection, use, storage, protection, retention or transfer of data. The regulatory framework for online services, data privacy and cyber security issues worldwide can vary substantially from jurisdiction to jurisdiction, is rapidly evolving and is likely to remain uncertain for the foreseeable future. Many federal, state and foreign government bodies and agencies have adopted or are considering adopting laws, rules and regulations regarding the collection, use, storage and disclosure of information, web browsing and geolocation data collection, data analytics, cyber security and breach notification procedures. Interpretation of these laws, rules and regulations and their application to our products and professional services in the U.S. and foreign jurisdictions is ongoing and cannot be fully determined at this time.
In the United States, these include rules and regulations promulgated under the authority of the Federal Trade Commission, the Electronic Communications Privacy Act, Computer Fraud and Abuse Act, HIPAA, the Gramm Leach Bliley Act and state breach notification laws, as well as regulator enforcement positions and expectations reflected in federal and state regulatory actions, settlements, consent decrees and guidance documents. Internationally, virtually every jurisdiction in which we operate has established its own data security and privacy legal frameworks with which we, or our customers, must comply, including the Data Protection Directive 95/46/EC (“Directive”) established in the European Union (“EU”) and local EU Member State legislation implementing the Directive, such as the Data Protection Act in the UK. Further, many federal, state and foreign government bodies and agencies have introduced, and are currently considering, additional laws and regulations. If passed, we will likely incur additional expenses and costs associated with complying with such laws.
In addition, to facilitate the transfer of both customer and personnel data from the European Union to the United States, we signed up to the EU-U.S. Safe Harbor Framework, which required U.S.-based companies to provide assurance that they are adhering to relevant European standards for data protection. On October 6, 2015, the Court of Justice of the European Union, or CJEU, invalidated the EU-U.S. Safe Harbor Framework. In light of CJEU’s decision, we are reviewing our current operations to ensure that our EU-U.S. data transfers comply with EU data protection laws. The available legal basis for such transfers will depend on a number of factors, including, for example, the type of data and the European Economic Area country from which the data is being transferred, and may require that we obtain express consent from the customer or employee whose data is being transferred or include in our agreements with the applicable customer or European Economic Area employing entity the standard contractual clauses that have been approved by the EU Commission or adopt one of the other alternative mechanisms available in order to effect such transfers in compliance with the EU laws (although certain German regulators have expressed concerns in respect of the standard contractual clauses and the Irish DPA has commenced proceedings in the Irish High Court to seek a reference to the CJEU as to whether the standard contractual clauses can be used as a basis for data transfers to the U.S.). Our compliance actions may involve substantial time and expense; for example, if we enter into the standard contractual clauses with a customer, in some EU countries, including Belgium and Spain, executed clauses need to be lodged with or notified to the country’s data protection authority prior to the transfer of any data, and in other countries, including Austria, France, Ireland, Romania and Slovenia, the clauses need to be approved by the country’s data protection authority prior to use. Non-compliance could result in the EU data protection authorities imposing a number of different sanctions on us until we do, including fines and, ultimately, a prohibition on transfers.
In addition to government regulation, privacy advocates and industry groups may propose new and different self-regulatory standards that either legally or contractually apply to us. Because the interpretation and application of
34
Table of Contents
privacy and data protection laws are still uncertain, it is possible that these laws may be interpreted and applied in a manner that is inconsistent with our existing practices or the features of our products. We may also be subject to claims of liability or responsibility for the actions of third parties with whom we interact or upon whom we rely in relation to various services, including but not limited to vendors and business partners. If so, in addition to the possibility of fines, lawsuits and other claims, we could be required to fundamentally change our business activities and practices or modify our products, which could have an adverse effect on our business. Any inability to adequately address privacy concerns, even if unfounded, or comply with applicable privacy or data protection laws, regulations and policies, could result in additional cost and liability to us, damage our reputation, inhibit sales and adversely affect our business.
The costs of compliance with, and other burdens imposed by, the laws, rules, regulations and policies that are applicable to the businesses of our customers may limit the use and adoption of, and reduce the overall demand for, our software. Privacy or cyber security concerns, whether valid or not valid, may inhibit market adoption of our products particularly in certain industries and foreign countries.
Further, there are active legislative discussions regarding the implementation of laws or regulations that could restrict the manner in which security research is conducted and that could restrict or possibly bar the conduct of penetration testing and the use of exploits, which are an essential component of our Metasploit product and our business strategy more generally. Our failure to comply with existing laws, rules or regulations, changes to existing laws or their interpretation, or the imposition of new laws, rules or regulations, could have a material and adverse impact on our business, results of operations, and financial condition.
Failure to protect our proprietary technology and intellectual property rights could substantially harm our business and operating results.
Our future success and competitive position depend in part on our ability to protect our intellectual property and proprietary technologies. To safeguard these rights, we rely on a combination of patent, trademark, copyright and trade secret laws and contractual protections in the United States and other jurisdictions, all of which provide only limited protection and may not now or in the future provide us with a competitive advantage.
We cannot assure you that any patents will issue from any patent applications, that patents that issue from such applications will give us the protection that we seek or that any such patents will not be challenged, invalidated, or circumvented. Any patents that may issue in the future from our pending or future patent applications may not provide sufficiently broad protection and may not be enforceable in actions against alleged infringers. We have registered the “Rapid7,” “Nexpose” and “Metasploit” names and logos in the United States and certain other countries. We have registrations and/or pending applications for additional marks in the United States and other countries; however, we cannot assure you that any future trademark registrations will be issued for pending or future applications or that any registered trademarks will be enforceable or provide adequate protection of our proprietary rights. We also license software from third parties for integration into our products, including open source software and other software available on commercially reasonable terms. We cannot assure you that such third parties will maintain such software or continue to make it available.
In order to protect our unpatented proprietary technologies and processes, we rely on trade secret laws and confidentiality agreements with our employees, consultants, channel partners, vendors and others. Despite our efforts to protect our proprietary technology and trade secrets, unauthorized parties may attempt to misappropriate, reverse engineer or otherwise obtain and use them. In addition, others may independently discover our trade secrets, in which case we would not be able to assert trade secret rights, or develop similar technologies and processes. Further, the contractual provisions that we enter into may not prevent unauthorized use or disclosure of our proprietary technology or intellectual property rights and may not provide an adequate remedy in the event of unauthorized use or disclosure of our proprietary technology or intellectual property rights. Moreover, policing unauthorized use of our technologies, trade secrets and intellectual property is difficult, expensive and time-consuming, particularly in foreign countries where the laws may not be as
35
Table of Contents
protective of intellectual property rights as those in the United States and where mechanisms for enforcement of intellectual property rights may be weak. We may be unable to determine the extent of any unauthorized use or infringement of our solutions, technologies or intellectual property rights.
From time to time, legal action by us may be necessary to enforce our patents and other intellectual property rights, to protect our trade secrets, to determine the validity and scope of the intellectual property rights of others or to defend against claims of infringement or invalidity. Such litigation could result in substantial costs and diversion of resources and could negatively affect our business, operating results and financial condition.
Assertions by third parties of infringement or other violations by us of their intellectual property rights, whether or not correct, could result in significant costs and harm our business and operating results.
Patent and other intellectual property disputes are common in our industry. We are currently involved in a lawsuit brought by a non-practicing entity alleging that we have infringed upon a now-expired patent held by such entity and we may, from time to time, be involved in other such disputes in the ordinary course of our business. Some companies, including some of our competitors, own large numbers of patents, copyrights and trademarks, which they may use to assert claims against us. Third parties have in the past and may in the future assert claims of infringement, misappropriation or other violations of intellectual property rights against us. They may also assert such claims against our customers or channel partners, whom we typically indemnify against claims that our solutions infringe, misappropriate or otherwise violate the intellectual property rights of third parties. As the numbers of products and competitors in our market increase and overlaps occur, claims of infringement, misappropriation and other violations of intellectual property rights may increase. Any claim of infringement, misappropriation or other violation of intellectual property rights by a third party, even those without merit, could cause us to incur substantial costs defending against the claim and could distract our management from our business.
The patent portfolios of our most significant competitors are larger than ours. This disparity may increase the risk that they may sue us for patent infringement and may limit our ability to counterclaim for patent infringement or settle through patent cross-licenses. In addition, future assertions of patent rights by third parties, and any resulting litigation, may involve patent holding companies or other adverse patent owners who have no relevant product revenues and against whom our own patents may therefore provide little or no deterrence or protection. There can be no assurance that we will not be found to infringe or otherwise violate any third-party intellectual property rights or to have done so in the past.
An adverse outcome of a dispute may require us to:
| • | pay substantial damages, including treble damages, if we are found to have willfully infringed a third party’s patents or copyrights; |
| • | cease making, licensing or using solutions that are alleged to infringe or misappropriate the intellectual property of others; |
| • | expend additional development resources to attempt to redesign our solutions or otherwise develop non-infringing technology, which may not be successful; |
| • | enter into potentially unfavorable royalty or license agreements in order to obtain the right to use necessary technologies or intellectual property rights; and |
| • | indemnify our partners and other third parties. |
In addition, royalty or licensing agreements, if required or desirable, may be unavailable on terms acceptable to us, or at all, and may require significant royalty payments and other expenditures. Some licenses may also be non-exclusive, and therefore, our competitors may have access to the same technology licensed to us. Any of the foregoing events could seriously harm our business, financial condition and results of operations.
36
Table of Contents
Our intercompany relationships are subject to complex transfer pricing regulations, which may be challenged by taxing authorities.
We generally conduct our international operations through wholly-owned subsidiaries and report our taxable income in various jurisdictions worldwide based upon our business operations in those jurisdictions. In 2016, we completed the reorganization of our corporate structure and intercompany relationships to more closely align our corporate organization with the expansion of our international business activities. Although we anticipate achieving a reduction in our overall effective tax rate in the future as a result of this reorganized corporate structure, we may not realize any benefits. Our intercompany relationships are and will continue to be subject to complex transfer pricing regulations administered by taxing authorities in various jurisdictions. The relevant taxing authorities may disagree with our determinations as to the income and expenses attributable to specific jurisdictions. If such a disagreement were to occur, and our position were not sustained, we could be required to pay additional taxes, interest and penalties, which could result in one-time tax charges, higher effective tax rates, reduced cash flows and lower overall profitability of our operations. In addition, if the intended tax treatment of our reorganized corporate structure is not accepted by the applicable taxing authorities, changes in tax law negatively impact the structure or we do not operate our business consistent with the structure and applicable tax laws and regulations, we may fail to achieve any tax advantages as a result of the reorganized corporate structure, and our future operating results and financial condition may be negatively impacted.
Our ability to use net operating losses to offset future taxable income may be subject to certain limitations.
As of December 31, 2016, we had federal and state net operating loss carryforwards, or NOLs, of $93.8 million and $69.2 million, respectively, available to offset future taxable income, which expire in various years beginning in 2023 if not utilized. A lack of future taxable income would adversely affect our ability to utilize these NOLs before they expire. Under the provisions of the Internal Revenue Code of 1986, as amended, or the Internal Revenue Code, substantial changes in our ownership may limit the amount of pre-change NOLs that can be utilized annually in the future to offset taxable income. Section 382 of the Internal Revenue Code imposes limitations on a company’s ability to use NOLs if a company experiences a more-than-50-percent ownership change over a three-year testing period. Based upon our analysis as of December 31, 2016, we determined that although a small limitation on our historical NOLs exists, we do not expect this limitation to impair our ability to use our NOLs prior to expiration. However, if changes in our ownership occur in the future, our ability to use our NOLs may be further limited. For these reasons, we may not be able to utilize a material portion of the NOLs, even if we achieve profitability. If we are limited in our ability to use our NOLs in future years in which we have taxable income, we will pay more taxes than if we were able to fully utilize our NOLs. This could adversely affect our operating results and the market price of our common stock.
The enactment of legislation implementing changes in the U.S. taxation of international business activities or the adoption of other tax reform policies could materially impact our financial position and results of operations.
Recent changes to U.S. tax laws, including limitations on the ability of taxpayers to claim and utilize foreign tax credits and the deferral of certain tax deductions until earnings outside of the United States are repatriated to the United States, as well as changes to U.S. tax laws that may be enacted in the future, could impact the tax treatment of our foreign earnings. Due to expansion of our international business activities, any changes in the U.S. taxation of such activities may increase our worldwide effective tax rate and adversely affect our financial condition and operating results. Additionally, changes in foreign tax laws, in particular with regard to UK tax policy, may adversely impact our worldwide tax rate.
Our operating results may be harmed if we are required to collect sales and use or other related taxes for our products and professional services in jurisdictions where we have not historically done so.
Taxing jurisdictions, including state, local and foreign taxing authorities, have differing rules and regulations governing sales and use or other taxes, and these rules and regulations are subject to varying interpretations that
37
Table of Contents
may change over time. In particular, significant judgment is required in evaluating our tax positions and our worldwide provision for taxes. While we believe that we are in material compliance with our obligations under applicable taxing regimes, one or more states, localities or countries may seek to impose additional sales or other tax collection obligations on us, including for past sales. It is possible that we could face sales tax audits and that such audits could result in tax-related liabilities for which we have not accrued. A successful assertion that we should be collecting additional sales or other taxes on our offerings in jurisdictions where we have not historically done so and do not accrue for sales taxes could result in substantial tax liabilities for past sales, discourage customers from purchasing our offerings or otherwise harm our business and operating results.
In addition, our tax obligations and effective tax rates could be adversely affected by changes in the relevant tax, accounting and other laws, regulations, principles and interpretations, including those relating to income tax nexus, by recognizing tax losses or lower than anticipated earnings in jurisdictions where we have lower statutory rates and higher than anticipated earnings in jurisdictions where we have higher statutory rates, by changes in foreign currency exchange rates, or by changes in the valuation of our deferred tax assets and liabilities. Although we believe our tax estimates are reasonable, the final determination of any tax audits or litigation could be materially different from our historical tax provisions and accruals, which could have a material adverse effect on our operating results or cash flows in the period or periods for which a determination is made.
Our business is subject to the risks of earthquakes, fire, power outages, floods and other catastrophic events, and to interruption by manmade problems such as terrorism.
A significant natural disaster, such as an earthquake, fire or a flood, or a significant power outage could have a material adverse impact on our business, operating results and financial condition. In addition, natural disasters could affect our channel partners’ ability to perform services for us on a timely basis. In the event we or our channel partners are hindered by any of the events discussed above, our ability to provide our products or professional services to customers could be delayed.
In addition, our facilities and those of our third-party data centers and hosting providers are vulnerable to damage or interruption from human error, intentional bad acts, pandemics, earthquakes, hurricanes, floods, fires, war, terrorist attacks, power losses, hardware failures, systems failures, telecommunications failures and similar events. The occurrence of a natural disaster, power failure or an act of terrorism, vandalism or other misconduct, a decision by a third party to close a facility on which we rely without adequate notice, or other unanticipated problems could result in lengthy interruptions in provision or delivery of our products, potentially leaving our customers vulnerable to cyber attacks. The occurrence of any of the foregoing events could damage our systems and hardware or could cause them to fail completely, and our insurance may not cover such events or may be insufficient to compensate us for the potentially significant losses, including the potential harm to the future growth of our business, that may result from interruptions in our service as a result of system failures.
All of the aforementioned risks may be exacerbated if our disaster recovery plans or the disaster recovery plans established for our third-party data centers and hosting providers prove to be inadequate. To the extent that any of the above results in delayed or reduced customer sales, our business, financial condition and results of operations could be adversely affected.
Risks Related to our Common Stock
The market price of our common stock has been and is likely to continue to be volatile.
The market price of our common stock may be highly volatile and may fluctuate substantially as a result of a variety of factors, some of which are related in complex ways. Since shares of our common stock were sold in our initial public offering, or IPO, in July 2015 at a price of $16.00 per share, our stock price has ranged from an intraday low of $9.05 to an intraday high of $27.45 through March 1, 2017. Factors that may affect the market price of our common stock include:
| • | actual or anticipated fluctuations in our financial condition and operating results; |
38
Table of Contents
| • | variance in our financial performance from expectations of securities analysts; |
| • | changes in the prices of our products and professional services; |
| • | changes in our projected operating and financial results; |
| • | changes in laws or regulations applicable to our products or professional services; |
| • | announcements by us or our competitors of significant business developments, acquisitions or new offerings; |
| • | our involvement in any litigation; |
| • | our sale of our common stock or other securities in the future; |
| • | changes in senior management or key personnel; |
| • | trading volume of our common stock; |
| • | changes in the anticipated future size and growth rate of our market; and |
| • | general economic, regulatory and market conditions. |
Recently, the stock markets have experienced extreme price and volume fluctuations that have affected and continue to affect the market prices of equity securities of many companies. These fluctuations have often been unrelated or disproportionate to the operating performance of those companies. Broad market and industry fluctuations, as well as general economic, political, regulatory and market conditions, may negatively impact the market price of our common stock. In the past, companies that have experienced volatility in the market price of their securities have been subject to securities class action litigation. We may be the target of this type of litigation in the future, which could result in substantial costs and divert our management’s attention.
An active public trading market for our common stock may not be sustained.
Prior to the completion of our IPO in July 2015, no public market for our common stock existed. Although our common stock is listed on The NASDAQ Global Market, we cannot assure you that an active public trading market for our common stock will continue to develop or be sustained. If an active market for our common stock does not continue to develop or is not sustained, it may be difficult for investors in our common stock to sell shares without depressing the market price for the shares or to sell the shares at all. An inactive market may also impair our ability to raise capital to continue to fund operations by selling shares and may impair our ability to acquire other companies or technologies by using our shares as consideration.
We may fail to meet our publicly announced guidance or other expectations about our business and future operating results, which would cause our stock price to decline.
We have provided and may continue to provide guidance about our business, key metrics and future operating results. In developing this guidance, our management must make certain assumptions and judgments about our future performance. Furthermore, analysts and investors may develop and publish their own projections of our business, which may form a consensus about our future performance. Our business results may vary significantly from such guidance or that consensus due to a number of factors, many of which are outside of our control, and which could adversely affect our operations and operating results. Furthermore, if we make downward revisions of our previously announced guidance, or if our publicly announced guidance of future operating results fails to meet expectations of securities analysts, investors or other interested parties, the price of our common stock would decline.
If securities or industry analysts do not publish research or reports about our business, or publish negative reports about our business, our stock price and trading volume could decline.
The trading market for our common stock will depend, in part, on the research and reports that securities or industry analysts publish about us or our business. We do not have any control over these analysts. If our
39
Table of Contents
financial performance fails to meet analyst estimates or one or more of the analysts who cover us downgrade our shares or change their opinion of our shares, our share price would likely decline. If one or more of these analysts cease coverage of our company or fail to regularly publish reports on us, we could lose visibility in the financial markets, which could cause our share price or trading volume to decline.
We do not intend to pay dividends for the foreseeable future and, as a result, your ability to achieve a return on your investment will depend on appreciation in the price of our common stock.
We have never declared or paid any cash dividends on our common stock and do not intend to pay any cash dividends in the foreseeable future. We anticipate that we will retain all of our future earnings for use in the development of our business and for general corporate purposes. Any determination to pay dividends in the future will be at the discretion of our board of directors. Accordingly, investors must rely on sales of their common stock after price appreciation, which may never occur, as the only way to realize any future gains on their investments.
Concentration of ownership among our existing directors, executive officers and holders of 10% or more of our outstanding common stock may prevent minority investors from influencing significant corporate decisions.
As of March 1, 2017, our directors, executive officers and holders of more than 10% of our common stock, some of whom are represented on our board of directors, together with their affiliates, beneficially owned 52% of the voting power of our outstanding capital stock. As a result, these stockholders will be able to determine the outcome of matters submitted to our stockholders for approval. This concentration of ownership by itself may have the effect of delaying, deferring or preventing a change in control of our company, impeding a merger, consolidation, takeover or other business combination involving us, or discouraging a potential acquirer from making a tender offer or otherwise attempting to obtain control, which in turn, could materially and adversely affect the market price of our common stock.
Future sales of our common stock in the public market could cause our share price to decline.
Sales of a substantial number of shares of our common stock in the public market, or the perception that these sales might occur, could depress the market price of our common stock and could impair our ability to raise capital through the sale of additional equity securities. We are unable to predict the effect that sales, particularly sales by our directors, executive officers, and significant stockholders, may have on the prevailing market price of our common stock. Additionally, the shares of common stock subject to outstanding options under our equity incentive plans and the shares reserved for future issuance under our equity incentive plans, as well as shares issuable upon vesting of restricted stock awards, will become eligible for sale in the public market in the future, subject to certain legal and contractual limitations.
Additionally, certain holders of our common stock have the right, subject to various conditions and limitations, to request we include their shares of our common stock in registration statements we may file relating to our securities.
In addition, in the future, we may issue common stock or other securities if we need to raise additional capital. The number of new shares of our common stock issued in connection with raising additional capital could constitute a material portion of our then-outstanding shares of our common stock.
We are an “emerging growth company” and we cannot be certain if the reduced disclosure requirements applicable to emerging growth companies will make our common stock less attractive to investors.
We are an “emerging growth company,” as defined in the JOBS Act. For as long as we qualify as an emerging growth company, we intend to take advantage of certain exemptions from various reporting requirements that are
40
Table of Contents
applicable to other public companies that are not “emerging growth companies” including, but not limited to, the auditor attestation requirements of Section 404 of the Sarbanes-Oxley Act, reduced disclosure obligations regarding executive compensation in our periodic reports and proxy statements, and exemptions from the requirements of holding a nonbinding advisory vote on executive compensation and stockholder approval of any golden parachute payments not previously approved. We cannot predict if investors will find our common stock less attractive because we will rely on these exemptions and provide reduced disclosure. If some investors find our common stock less attractive as a result, there may be a less active trading market for our common stock and our stock price may be more volatile.
We have and will continue to incur increased costs as a result of being a public company.
As a newly public company, and particularly after we are no longer an “emerging growth company,” we have incurred and we will continue to incur significant legal, accounting and other expenses that we did not incur as a private company. The Sarbanes-Oxley Act, the Dodd-Frank Wall Street Reform and Consumer Protection Act, the listing requirements of the NASDAQ Stock Market and other applicable securities rules and regulations impose various requirements on public companies. We expect that compliance with these requirements will continue to increase certain of our expenses and make some activities more time-consuming than they have been in the past when we were a private company. Such additional costs going forward could negatively affect our financial results.
We are obligated and maintain proper and effective internal controls over financial reporting and any failure to maintain the adequacy of these internal controls may adversely affect investor confidence in our company and, as a result, the value of our common stock.
Commencing with this Annual Report, we are required, pursuant to Section 404 of the Sarbanes-Oxley Act, or Section 404, to furnish a report by management on, among other things, the effectiveness of our internal control over financial reporting on an annual basis. This assessment includes disclosure of any material weaknesses identified by our management in our internal control over financial reporting. During the evaluation and testing process, if we identify one or more material weaknesses in our internal control over financial reporting, we will be unable to assert that our internal controls are effective. While we have established certain procedures and control over our financial reporting processes, we cannot assure you that these efforts will prevent restatements of our financial statements in the future.
Our independent registered public accounting firm will not be required to attest to the effectiveness of our internal control over financial reporting until our first annual report required to be filed with the SEC following the date we no longer qualify as an “emerging growth company,” as defined in the JOBS Act. At such time, our independent registered public accounting firm may issue a report that is adverse in the event it is not satisfied with the level at which our controls are documented, designed or operating. We may not be able to remediate any future material weaknesses, or to complete our evaluation, testing and any required remediation in a timely fashion. We will be required to disclose significant changes made in our internal control procedures on a quarterly basis.
Our compliance with Section 404 will require that we incur substantial accounting expense and expend significant management efforts. We currently do not have an internal audit group, and we may need to hire additional accounting and financial staff with appropriate public company experience and technical accounting knowledge and compile the system and process documentation necessary to perform the evaluation needed to comply with Section 404.
Any failure to maintain internal control over financial reporting could severely inhibit our ability to accurately report our financial condition or results of operations. If we are unable to assert that our internal control over financial reporting is effective or our independent registered public accounting firm is unable to express an opinion on the effectiveness of our internal controls when it is required to issue such opinion, we could lose
41
Table of Contents
investor confidence in the accuracy and completeness of our financial reports, the market price of our common stock could decline, and we could be subject to sanctions or investigations by the NASDAQ Stock Market, the SEC or other regulatory authorities. Failure to remedy any material weakness in our internal control over financial reporting, or to implement or maintain other effective control systems required of public companies, could also restrict our future access to the capital markets.
Anti-takeover provisions in our charter documents and under Delaware law could make an acquisition of us more difficult, limit attempts by our stockholders to replace or remove our current management and limit the market price of our common stock.
Provisions in our amended and restated certificate of incorporation and amended and restated bylaws may have the effect of delaying or preventing a change in control or changes in our management. Among other things, our amended and restated certificate of incorporation and amended and restated bylaws include provisions that:
| • | authorize our board of directors to issue preferred stock without further stockholder action and with voting liquidation, dividend and other rights superior to our common stock; |
| • | require that any action to be taken by our stockholders be effected at a duly called annual or special meeting and not by written consent, and limit the ability of our stockholders to call special meetings; |
| • | establish an advance notice procedure for stockholder proposals to be brought before an annual meeting, including proposed nominations of persons for director nominees; |
| • | establish that our board of directors is divided into three classes, with directors in each class serving three-year staggered terms; |
| • | require the approval of holders of two-thirds of the shares entitled to vote at an election of directors to adopt, amend or repeal our amended and restated bylaws or amend or repeal the provisions of our amended and restated certificate of incorporation regarding the election and removal of directors and the ability of stockholders to take action by written consent or call a special meeting; |
| • | prohibit cumulative voting in the election of directors; and |
| • | provide that vacancies on our board of directors may be filled only by a majority of directors then in office, even though less than a quorum. |
These provisions may frustrate or prevent any attempts by our stockholders to replace or remove our current management by making it more difficult for stockholders to replace members of our board of directors, who are responsible for appointing the members of our management. In addition, because we are incorporated in Delaware, we are governed by the provisions of Section 203 of the Delaware General Corporation Law, which generally prohibits a Delaware corporation from engaging in any of a broad range of business combinations with any “interested” stockholder for a period of three years following the date on which the stockholder became an “interested” stockholder. Any of the foregoing provisions could limit could limit the opportunity for our stockholders to receive a premium for their shares of our common stock, and could also affect the price that some investors are willing to pay for our common stock.
Our amended and restated certificate of incorporation designates the Court of Chancery of the State of Delaware as the exclusive forum for certain litigation that may be initiated by our stockholders, which could limit our stockholders’ ability to obtain a favorable judicial forum for disputes with us.
Pursuant to our amended and restated certificate of incorporation, unless we consent in writing to the selection of an alternative forum, the Court of Chancery of the State of Delaware is the sole and exclusive forum for (1) any derivative action or proceeding brought on our behalf, (2) any action asserting a claim of breach of a fiduciary duty owed by any of our directors, officers or other employees to us or our stockholders, (3) any action asserting a claim arising pursuant to any provision of the Delaware General Corporation Law, our amended and restated certificate of incorporation or our amended and restated bylaws or (4) any action asserting a claim governed by
42
Table of Contents
the internal affairs doctrine. Our amended and restated certificate of incorporation further provides that any person or entity purchasing or otherwise acquiring any interest in shares of our common stock is deemed to have notice of and consented to the foregoing provision. The forum selection clause in our amended and restated certificate of incorporation may limit our stockholders’ ability to obtain a favorable judicial forum for disputes with us.
Item 1B. Unresolved Staff Comments.
None.
Our corporate headquarters occupy approximately 75,000 square feet in Boston, Massachusetts under an operating lease that expires in August 2019. We have additional U.S. offices including Los Angeles, California; Cambridge, Massachusetts; Austin, Texas; and Alexandria, Virginia. We also lease various international offices including Toronto, Canada; Reading, United Kingdom; Belfast, Northern Ireland; Dublin, Ireland; and Singapore.
We believe that our current facilities are suitable and adequate to meet our current needs. We intend to add new facilities or expand existing facilities as we add employees, and we believe that suitable additional or substitute space will be available as needed to accommodate any such expansion of our operations.
From time to time, we may be a party to litigation or subject to claims incident to the ordinary course of business. Although the results of litigation and claims cannot be predicted with certainty, we currently believe that the final outcome of these ordinary course matters will not have a material adverse effect on our business. Regardless of the outcome, litigation can have an adverse impact on us because of defense and settlement costs, diversion of management resources and other factors.
Item 4. Mine Safety Disclosures.
Not applicable.
43
Table of Contents
PART II
Item 5. Market for Registrant’s Common Equity, Related Stockholder Matters and Issuer Purchases of Equity Securities.
Market Information
Our common stock has been listed on the NASDAQ Global Market under the symbol “RPD” since July 17, 2015. Prior to that date, there was no public trading market for our common stock. Our initial public offering was priced at $16.00 per share on July 16, 2015.
The following table sets forth the reported high and low sales prices of our common stock for the periods indicated, as quoted on the NASDAQ Global Market:
| Year Ended December 31, 2016: |
High | Low | ||||||
| First quarter |
$ | 16.75 | $ | 9.05 | ||||
| Second quarter |
$ | 14.82 | $ | 10.82 | ||||
| Third quarter |
$ | 19.29 | $ | 11.55 | ||||
| Fourth quarter |
$ | 18.30 | $ | 10.63 | ||||
| Year Ended December 31, 2015: | High | Low | ||||||
| Third Quarter (from July 17, 2015 to September 30, 2015) |
$ | 27.45 | $ | 16.50 | ||||
| Fourth Quarter |
$ | 24.76 | $ | 14.75 | ||||
As of December 31, 2016, there were 169 holders of record of our common stock. Because many of our shares are held by brokers and other institutions on behalf of stockholders, we are unable to estimate the total number of stockholders represented by these record holders.
Dividends
We have never declared or paid, and do not anticipate declaring or paying in the foreseeable future, any cash dividends on our common stock. Any future determination as to the declaration and payment of dividends, if any, will be at the discretion of our board of directors, subject to applicable laws, and will depend on then existing conditions, including our financial condition, operating results, contractual restrictions, capital requirements, business prospects and other factors our board of directors may deem relevant.
Stock Performance Graph
The following shall not be deemed incorporated by reference into any of our other filings under the Securities Exchange Act of 1934, as amended, or the Securities Act of 1933, as amended, except to the extent we specifically incorporate it by reference into such filings.
44
Table of Contents
The following graph shows a comparison from July 17, 2015 (the date our common stock commenced trading on the NASDAQ Global Market) through December 31, 2016 of the cumulative total return for an investment of $100 in our common stock, the NASDAQ Global Market and the NASDAQ Computer Index. Data for the NASDAQ Global Market and the NASDAQ Computer Index assume reinvestment of dividends.
The comparisons in the graph below are based upon historical data and are not indicative of, nor intended to forecast, future performance of our common stock.
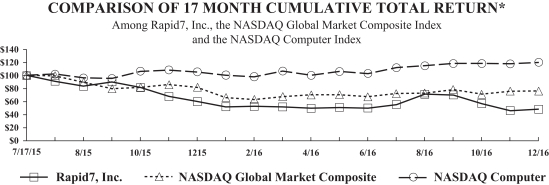
| July 17, 2015 |
July 31, 2015 |
August 31, 2015 |
October 31, 2015 |
December 31, 2015 |
February 28, 2016 |
April 30, 2016 |
June 30, 2016 |
August 31, 2016 |
October 31, 2016 |
December 31, 2016 |
||||||||||||||||||||||||||||||||||
| Rapid7, Inc. |
$ | 100.00 | $ | 90.90 | $ | 83.43 | $ | 81.33 | $ | 59.85 | $ | 52.57 | $ | 49.53 | $ | 49.76 | $ | 71.08 | $ | 56.69 | $ | 48.14 | ||||||||||||||||||||||
| NASDAQ Global Market Composite |
100.00 | 99.22 | 89.41 | 81.69 | 81.67 | 62.98 | 70.08 | 67.13 | 72.89 | 71.04 | 75.93 | |||||||||||||||||||||||||||||||||
| NASDAQ Computer |
100.00 | 101.89 | 96.18 | 106.23 | 105.13 | 97.85 | 99.92 | 102.79 | 114.67 | 118.25 | 119.77 | |||||||||||||||||||||||||||||||||
Recent Sales of Unregistered Securities
Not applicable.
Use of Proceeds from Public Offering of Common Stock
Our initial public offering of common stock was effected through the filing of a Registration Statement on Form S-1 (File No. 333-204874), which was declared or became effective on July 16, 2015. There has been no material change in the use of proceeds from our initial public offering as described in our final prospectus filed with the SEC pursuant to Rule 424(b) and other periodic reports previously filed with the SEC.
45
Table of Contents
Purchase of Equity Securities by the Issuer and Affiliated Purchasers
The following table provides information about our purchases of our equity securities during the three months ended December 31, 2016:
| Total Number of Shares Purchased (1) |
Average Price Paid per Share |
Total Number of Shares Purchased as Part of Publicly Announced Plans or Programs |
Approximate Dollar Value of Shares That May Yet Be Purchased Under the Plans or Programs (dollars in thousands) |
|||||||||||||
| October 1, 2016 to October 31, 2016 |
15,425 | $ | 15.42 | — | — | |||||||||||
| November 1, 2016 to November 30, 2016 |
— | — | — | — | ||||||||||||
| December 1, 2016 to December 31, 2016 |
— | — | — | — | ||||||||||||
|
|
|
|
|
|
|
|||||||||||
| Total |
15,425 | $ | 15.42 | — | — | |||||||||||
| (1) | Represents the total number of shares of our common stock delivered to us by an employee to satisfy the statutory tax withholding obligations owed in connection with the vesting of restricted stock awards granted to such employee under the Rapid7, Inc. 2015 Equity Incentive Plan, as amended. |
Securities Authorized for Issuance Under Equity Compensation Plans
Information about securities authorized for issuance under our equity compensation plan is incorporated herein by reference to Item 12 of Part III of this Annual Report on Form 10-K.
Item 6. Selected Financial Data.
The following selected historical financial data should be read in conjunction with Item 7, “Management’s Discussion and Analysis of Financial Condition and Results of Operations,” and our consolidated financial statements and the related notes appearing in Item 8, “Financial Statements and Supplementary Data,” of this Annual Report on Form 10-K to fully understand the factors that may affect the comparability of the information presented below.
The selected consolidated financial data in this section are not intended to replace the consolidated financial statements and are qualified in their entirety by the consolidated financial statements and related notes included elsewhere in this Annual Report on Form 10-K.
The following selected consolidated statements of operations data for the years ended December 31, 2016, 2015, and 2014, and the consolidated balance sheet data as of December 31, 2016 and 2015, have been derived from our audited consolidated financial statements included elsewhere in this Annual Report on Form 10-K. The consolidated statements of operations data for the year ended December 31, 2013 and 2012 and the consolidated balance sheet data as of December 31, 2014, 2013 and 2012 have been derived from our audited consolidated financial statements not included in this Annual Report on Form 10-K.
46
Table of Contents
| Year Ended December 31, | ||||||||||||||||||||
| 2016 | 2015 | 2014 | 2013 | 2012 | ||||||||||||||||
| (in thousands, except share and per share data) | ||||||||||||||||||||
| Consolidated Statement of Operations Data: |
||||||||||||||||||||
| Revenue: |
||||||||||||||||||||
| Products |
$ | 89,404 | $ | 63,407 | $ | 47,030 | $ | 38,633 | $ | 29,414 | ||||||||||
| Maintenance and support |
37,403 | 26,903 | 19,016 | 14,017 | 9,727 | |||||||||||||||
| Professional services |
30,630 | 20,216 | 10,834 | 7,380 | 6,903 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Total revenue |
157,437 | 110,526 | 76,880 | 60,030 | 46,044 | |||||||||||||||
| Cost of revenue(1): |
||||||||||||||||||||
| Products |
12,447 | 6,921 | 4,557 | 4,048 | 1,691 | |||||||||||||||
| Maintenance and support |
7,105 | 6,002 | 4,495 | 3,388 | 2,069 | |||||||||||||||
| Professional services |
20,173 | 16,321 | 9,420 | 5,442 | 4,462 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Total cost of revenue |
39,725 | 29,244 | 18,472 | 12,878 | 8,222 | |||||||||||||||
| Operating expenses(1): |
||||||||||||||||||||
| Research and development |
47,955 | 38,746 | 25,570 | 21,411 | 17,820 | |||||||||||||||
| Sales and marketing |
90,524 | 67,365 | 49,007 | 31,779 | 23,278 | |||||||||||||||
| General and administrative |
28,282 | 21,731 | 12,972 | 12,586 | 9,436 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Total operating expense |
166,761 | 127,842 | 87,549 | 65,776 | 50,534 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Loss from operations |
(49,049) | (46,560) | (29,141) | (18,624) | (12,712) | |||||||||||||||
| Interest income (expense), net |
131 | (2,523) | (2,802) | (122) | (71) | |||||||||||||||
| Other income (expense), net |
(109) | (278) | (305) | 43 | (29) | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Loss before income taxes |
(49,027) | (49,361) | (32,248) | (18,703) | (12,812) | |||||||||||||||
| Income tax (benefit) expense |
(27) | 496 | 379 | 170 | (418) | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Net loss |
(49,000) | (49,857) | (32,627) | (18,873) | (12,394) | |||||||||||||||
| Accretion of preferred stock to redemption value(2) |
— | (35,061) | (52,336) | (33,553) | (25,606) | |||||||||||||||
| Beneficial conversion feature relating to IPO participation payment |
— | (14,161) | — | — | — | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Net loss attributable to common stockholders |
$ | (49,000) | $ | (99,079) | $ | (84,963) | $ | (52,426) | $ | (38,000) | ||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Net loss per share attributable to common stockholders, basic and diluted |
$ | (1.19) | $ | (4.00) | $ | (6.65) | $ | (4.18) | $ | (3.09) | ||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Weighted-average common shares outstanding, basic and diluted |
41,248,473 | 24,740,480 | 12,770,916 | 12,549,266 | 12,308,428 | |||||||||||||||
47
Table of Contents
| (1) | Includes stock-based compensation expense and depreciation and amortization expense as follows: |
| Year Ended December 31, | ||||||||||||||||||||
| 2016 | 2015 | 2014 | 2013 | 2012 | ||||||||||||||||
| (in thousands) | ||||||||||||||||||||
| Stock-based compensation expense: |
||||||||||||||||||||
| Cost of revenue |
$ 610 | $ 532 | $ 167 | $ 67 | $ 61 | |||||||||||||||
| Research and development |
6,054 | 5,010 | 499 | 426 | 375 | |||||||||||||||
| Sales and marketing |
6,607 | 3,139 | 496 | 249 | 293 | |||||||||||||||
| General and administrative |
4,045 | 2,004 | 997 | 1,305 | 991 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Total stock-based compensation expense |
$ 17,316 | $ 10,685 | $ 2,159 | $ 2,047 | $ 1,720 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Depreciation and amortization expense: |
||||||||||||||||||||
| Cost of revenue |
$ 2,529 | $ 1,890 | $ 1,275 | $ 1,107 | $ 547 | |||||||||||||||
| Research and development |
1,080 | 1,138 | 1,093 | 649 | 406 | |||||||||||||||
| Sales and marketing |
1,842 | 1,617 | 1,396 | 675 | 444 | |||||||||||||||
| General and administrative |
1,274 | 707 | 376 | 200 | 132 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Total depreciation and amortization expense |
$ 6,725 | $ 5,352 | $ 4,140 | $ 2,631 | $ 1,529 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| (2) | See Note 11 to our consolidated financial statements appearing in Item 8 for further details on the calculation of accretion of preferred stock to redemption value and basic and diluted net loss per share attributable to common stockholders. |
| As of December 31, | ||||||||||||||||||||
| 2016 | 2015 | 2014 | 2013 | 2012 | ||||||||||||||||
| (in thousands) | ||||||||||||||||||||
| Consolidated Balance Sheet Data: |
||||||||||||||||||||
| Cash and cash equivalents |
$ | 53,148 | $ | 86,553 | $ | 36,823 | $ | 20,612 | $ | 7,667 | ||||||||||
| Working capital, excluding deferred revenue |
101,527 | 109,015 | 50,359 | 28,206 | 12,655 | |||||||||||||||
| Total assets |
243,303 | 230,561 | 86,966 | 59,855 | 41,782 | |||||||||||||||
| Total deferred revenue |
169,063 | 130,317 | 85,056 | 59,855 | 44,728 | |||||||||||||||
| Total debt |
— | — | 16,871 | 16,318 | 18 | |||||||||||||||
| Total liabilities |
201,265 | 162,486 | 122,230 | 92,432 | 58,797 | |||||||||||||||
| Redeemable convertible preferred stock |
— | — | 211,598 | 128,444 | 94,891 | |||||||||||||||
| Total stockholders’ equity (deficit) |
42,038 | 68,075 | (246,862) | (161,021) | (111,906) | |||||||||||||||
48
Table of Contents
Item 7. Management’s Discussion and Analysis of Financial Condition and Results of Operations.
The following discussion and analysis of our financial condition and results of operations should be read in conjunction with our consolidated financial statements and related notes appearing elsewhere in this Annual Report on Form 10-K. In addition to historical financial information, the following discussion contains forward-looking statements that reflect our plans, estimates and beliefs. Our actual results could differ materially from those contained in or implied by any forward-looking statements. Factors that could cause or contribute to these differences include those under “Risk Factors” included in Part I, Item 1A or in other parts of this Annual Report on Form 10-K.
Overview
Rapid7 is a leading provider of analytics for security and IT operations that enable organizations to implement an active, analytics-driven approach to cyber security and IT operations. Our data and analytics platform was purpose-built for today’s increasingly complex and chaotic IT environment. We make it simple to collect and unify operational data from across the entire IT infrastructure, and our advanced analytics unlock the information required to securely operate, manage and develop today’s sophisticated applications and services.
We combine our extensive experience in collecting disparate data, deep insight into attacker behaviors and techniques and our purpose-driven analytics to make sense of the wealth of data available to organizations about their IT environments and users. Our powerful and proprietary analytics enable organizations to contextualize and prioritize the threats facing their physical, virtual and cloud assets, including those posed by the behaviors of their users. Leveraging our IT data and analytics platform, our solutions enable organizations to strategically and dynamically manage their cyber security exposure and manage IT operations. Our solutions empower organizations to prevent attacks by providing visibility into vulnerabilities, and allow them to rapidly detect compromises, respond to breaches and correct the underlying causes of attacks. By providing a unified IT and security platform, with automated workflow, we enable IT and security to work together more effectively to develop, operate and secure their environment. For example, our platform and proprietary technologies were developed to help customers identify the weaknesses and exposures in their environment and are designed to enable them to detect and respond to breaches immediately. We help them troubleshoot performance issues across their infrastructure, applications and endpoints. Our platform approach enables organizations to collect data once and use it for ongoing unlimited use and access to solve the specific problems their organization faces, reducing the costs and overhead associated with relying on point solutions, and enabling workflow between organizations that must work together to resolve issues, reduce risk and increase resiliency.
We market and sell our products and professional services to global organizations of all sizes, including mid-market businesses, enterprises, non-profits, educational institutions and government agencies. Our customers span a wide variety of industries such as technology, energy, financial services, healthcare and life sciences, manufacturing, media and entertainment, retail, education, real estate, transportation, government and professional services. As of December 31, 2016, we had over 6,200 customers in 117 countries, including 38% of the Fortune 1000. Our revenue was not concentrated with any individual customer or group of customers, and no customer represented more than 2% of our revenue in 2016, 2015 or 2014.
We sell our products and services through direct inside and field sales team and indirect channel partner relationships. Our global sales teams focus on both new customer acquisition and up-selling and cross-selling additional offerings to our existing customers. Our sales teams are organized by geography, consisting of the Americas; Europe, the Middle East and Africa, or EMEA; and Asia Pacific, or APAC, as well as by target organization size. Our inside sales team focuses on small and middle-market transactions, while larger or more complex transactions are generally handled by our globally distributed direct field sales teams. Our highly technical sales engineers help define customer use cases, manage solution evaluations and train channel partners.
Recent Developments
In November 2016, we announced the beta launch of InsightOps, a new IT operations solution designed to centralize machine data across organizations’ infrastructures. This solution is designed to provide IT teams with
49
Table of Contents
comprehensive operational awareness by pairing endpoint visibility and log analytics. With InsightOps, we believe that IT professionals will have the ability to easily search and ask questions of their data to gain insights regarding core issues related to their IT environments faster, which, we believe, will ultimately improve uptime and business productivity. InsightOps is currently being tested in a beta program, and we anticipate it will be ready for sale during the first half of 2017.
In November 2016, we announced the appointment of Jeff Kalowski as our new Chief Financial Officer, effective January 9, 2017. He replaced Steven Gatoff, who joined us at the beginning of 2013, announced his planned departure in August 2016 and formally transitioned from our company in January 2017.
In October 2016, we announced that Andrew Burton, who was formerly our senior vice president of Logentries, was promoted to the position of Chief Operating Officer.
Our Business Model
We have three offerings: (1) threat exposure management, which includes our Nexpose, Metasploit and AppSpider products, (2) incident detection and response, which includes our InsightIDR, Managed Detection and Response (formerly known as “Analytic Response”) and Logentries products as well as our incident response services and (3) security advisory services.
We offer our products through a variety of delivery models to meet the needs of our diverse customer base, including:
| • | Licensed software, including both term and perpetual licenses, and the simultaneous sale of maintenance and support. Our Nexpose, Metasploit and AppSpider products are offered through perpetual or term software licenses, with a substantial majority of our customers selecting a perpetual license. Substantially all of our customers who purchase software licenses also purchase (1) an agreement for maintenance and support, which provides our customers with telephone and web-based support and ongoing bug fixes and repairs during the term of the maintenance and support agreement and (2) purchasers of Nexpose and Metasploit also purchase content subscriptions, which provide our customers with real-time access to the latest vulnerabilities and exploits. Our maintenance and support and content subscription agreements are typically for one to three-year terms. |
| • | Cloud-based subscriptions, where our software capabilities are provided to our customers through cloud access and on a Software as a Service, or SaaS, basis. Our InsightIDR, AppSpider and Logentries products are offered on a cloud-based subscription basis, generally with one to three-year terms. |
| • | Managed services, where we operate our software and provide our capabilities on behalf of our customers. Our Managed Vulnerability Management (Nexpose), Managed Application Security (AppSpider) and Managed Detection and Response (InsightIDR) products are offered on a managed service basis, generally pursuant to one to three-year agreements. |
We also offer various professional services across all of our offerings, including deployment and training services related to our Nexpose, Metasploit, AppSpider and InsightIDR software products, incident response services and security advisory services. Customers can purchase our professional services together with our product offerings or on a stand-alone basis pursuant to fixed fee or time-and-materials agreements.
An important component of our revenue growth strategy is to have our existing customers renew their agreements with us and purchase additional products from us. To assess our performance against this objective, we monitor the renewal rates of our existing customers. We calculate our renewal rate by dividing the dollar value of renewed customer agreements, including upsells and cross-sells of additional products, but excluding professional services, on a monthly basis in a trailing 12-month period by the dollar value of the corresponding
50
Table of Contents
expiring customer agreements. We also calculate an expiring renewal rate that does not take into account any upsells or cross-sells. As a result of this methodology, we would not expect our expiring renewal rate to exceed 100%. Our renewal rate was 120%, 126% and 111% in 2016, 2015 and 2014, respectively, and our expiring revenue renewal rate was 89%, 88% and 85% in 2016, 2015 and 2014, respectively. Our goal is to maintain what we believe are strong renewal rates, and work to increase them over time. However, our renewal rates may decline or fluctuate as a result of a number of factors, including customers’ satisfaction or dissatisfaction with our products and professional services, pricing, economic conditions or overall reductions in our customers’ spending levels.
We generate revenue from selling products, maintenance and support, and professional services. In 2016, 2015 and 2014, 81%, 82% and 86% of our revenue, respectively, was derived from sales of products and associated maintenance and support, while the remaining 19%, 18% and 14%, respectively, was derived from the sale of professional services.
In 2016, 2015 and 2014, recurring revenue, defined as sales of content subscriptions, managed services, cloud-based subscriptions and maintenance and support, made up 62% of total revenue. We generally bill customers and collect payment for both our products and services up front.
In 2016, 2015 and 2014, 55%, 53% and 53%, respectively, of our total revenue came from deferred revenue on the balance sheet at the beginning of the respective periods.
Key Metrics
We monitor the following key metrics to help us measure and evaluate the effectiveness of our operations:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (dollars in thousands) | ||||||||||||
| Total revenue |
$ | 157,437 | $ | 110,526 | $ | 76,880 | ||||||
| Year-over-year growth |
42.4% | 43.8% | 28.1% | |||||||||
| Operating cash flow |
$ | 9,112 | $ | (1,907 | ) | $ | (3,356 | ) | ||||
| Deferred revenue |
$ | 169,063 | $ | 130,317 | $ | 85,056 | ||||||
| Number of customers |
6,206 | 5,132 | 3,733 | |||||||||
Total Revenue and Growth. We are focused on driving continued revenue growth through increased sales of our products and professional services to new and existing customers.
Operating Cash Flow. We monitor our operating cash flow as a measure of our overall business performance, which enables us to analyze our financial performance without the effects of certain non-cash items such as stock-based compensation expenses and depreciation and amortization. Additionally, operating cash flow takes into account the increase in deferred revenue as a result of increases in sales of products and services, which reflects the receipt of cash payment for products before they are recognized into revenue. Our operating cash flow is significantly impacted by timing of commission and bonus payments and collections of accounts receivable.
Deferred Revenue. We believe that deferred revenue is an important metric as it provides visibility into the revenue to be recognized in future periods. Our deferred revenue consists of amounts that have been invoiced to customers but that have not yet been recognized as revenue. Our deferred revenue balance primarily consists of the portion of products, maintenance and support and professional services revenue that will be recognized ratably over the applicable maintenance and support contract period. Revenue from professional services that are sold on a stand-alone basis is recognized as those services are rendered.
51
Table of Contents
Number of Customers. We believe that the size of our customer base is an indicator of our global market penetration and that our net customer additions are an indicator of the growth of our business. We define a customer as any entity that has (1) an active Rapid7 contract or a contract that expired within 90 days or less of the applicable measurement date; and for Logentries products, those customers with a contract value equal to or greater than $2,400 per year, and (2) purchased Rapid7 professional services within the 12 months preceding the applicable measurement date.
Non-GAAP Financial Results
To supplement our consolidated financial statements, which are prepared and presented in accordance with generally accepted accounting principles in the United States, or GAAP, we provide investors with certain non-GAAP financial measures, including non-GAAP gross profit, non-GAAP operating loss, non-GAAP net loss, and non-GAAP net loss per share, which we collectively refer to as non-GAAP financial measures. These non-GAAP financial measures exclude all or a combination of the following (as reflected in the following reconciliation tables): stock-based compensation expense, amortization of acquired intangible assets, acquisition-related expenses and impairment of long-lived assets. The presentation of the non-GAAP financial measures is not intended to be considered in isolation or as a substitute for, or superior to, the financial information prepared and presented in accordance with GAAP. We use these non-GAAP financial measures for financial and operational decision-making purposes and as a means to evaluate period-to-period comparisons, and use certain non-GAAP financial measures as performance measures under our executive bonus plan. We believe that these non-GAAP financial measures provide useful information about our operating results, enhance the overall understanding of past financial performance and future prospects and allow for greater transparency with respect to metrics used by our management in its financial and operational decision making. While our non-GAAP financial measures are an important tool for financial and operational decision making and for evaluating our own operating results over different periods of time, you should review the reconciliation of our non-GAAP financial measures to the comparable GAAP financial measures included below, and not rely on any single financial measure to evaluate our business.
We exclude stock-based compensation expense because of varying available valuation methodologies, subjective assumptions and the variety of equity instruments that can impact our non-cash expense. We believe that providing non-GAAP financial measures that exclude stock-based compensation expense allow for more meaningful comparisons between our operating results from period to period. We believe that excluding the impact of amortization of intangible assets allows for more meaningful comparisons between operating results from period to period as the intangibles are valued at the time of acquisition and are amortized over several years after the acquisition. We also exclude the impact of costs directly related to acquisitions and asset impairments as these costs are unrelated to the current operations and neither comparable to the prior period nor predictive of future results, which we believe allows for a more meaningful comparison between the operating results from period to period. Accordingly, we believe that excluding these expenses provides investors and management with greater visibility into the underlying performance of our business operations, facilitates comparison of our results with other periods and may also facilitate comparison with the results of other companies in our industry.
Our non-GAAP financial measures may not provide information that is directly comparable to that provided by other companies in our industry, as other companies in our industry may calculate non-GAAP financial results differently, particularly related to non-recurring, unusual items. In addition, there are limitations in using non-GAAP financial measures because the non-GAAP financial measures are not prepared in accordance with GAAP, may be different from non-GAAP financial measures used by other companies and exclude expenses that may have a material impact upon our reported financial results. Further, stock-based compensation expense has been and will continue to be for the foreseeable future a significant recurring expense in our business and an important part of the compensation provided to our employees.
52
Table of Contents
The following tables reconcile GAAP gross profit to non-GAAP gross profit for the years ended 2016, 2015 and 2014:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| GAAP total gross profit |
$ | 117,712 | $ | 81,282 | $ | 58,408 | ||||||
| Stock-based compensation expense |
610 | 532 | 167 | |||||||||
| Amortization of intangible assets |
1,782 | 1,212 | 869 | |||||||||
|
|
|
|
|
|
|
|||||||
| Non-GAAP total gross profit |
$ | 120,104 | $ | 83,026 | $ | 59,444 | ||||||
|
|
|
|
|
|
|
|||||||
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| GAAP gross profit – products and maintenance and support |
$ | 107,255 | $ | 77,387 | $ | 56,994 | ||||||
| Stock-based compensation expense |
282 | 281 | 13 | |||||||||
| Amortization of intangible assets |
1,782 | 1,212 | 869 | |||||||||
|
|
|
|
|
|
|
|||||||
| Non-GAAP gross profit – products and maintenance and support |
$ | 109,319 | $ | 78,880 | $ | 57,876 | ||||||
|
|
|
|
|
|
|
|||||||
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| GAAP gross profit – professional services |
$ | 10,457 | $ | 3,895 | $ | 1,414 | ||||||
| Stock-based compensation expense |
328 | 251 | 154 | |||||||||
|
|
|
|
|
|
|
|||||||
| Non-GAAP gross profit – professional services |
$ | 10,785 | $ | 4,146 | $ | 1,568 | ||||||
|
|
|
|
|
|
|
|||||||
The following table reconciles GAAP loss from operations to non-GAAP loss from operations for the years ended 2016, 2015 and 2014:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| GAAP loss from operations |
$ | (49,049 | ) | $ | (46,560 | ) | $ | (29,141 | ) | |||
| Stock-based compensation expense |
17,316 | 10,685 | 2,159 | |||||||||
| Amortization of intangible assets |
2,438 | 1,286 | 869 | |||||||||
| Acquisition-related expenses |
— | 1,342 | — | |||||||||
| Impairment of long-lived assets |
— | 483 | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Non-GAAP loss from operations |
$ | (29,295 | ) | $ | (32,764 | ) | $ | (26,113 | ) | |||
|
|
|
|
|
|
|
|||||||
53
Table of Contents
The following table reconciles GAAP net loss attributable to common stockholders to non-GAAP net loss for the years ended 2016, 2015 and 2014:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands, except share and per share data) | ||||||||||||
| GAAP net loss attributable to common stockholders |
$ | (49,000 | ) | $ | (99,079 | ) | $ | (84,963 | ) | |||
| Accretion of preferred stock to redemption value |
— | 35,061 | 52,336 | |||||||||
| Beneficial conversion charge relating to IPO participation payment |
— | 14,161 | — | |||||||||
|
|
|
|
|
|
|
|||||||
| GAAP net loss |
(49,000 | ) | (49,857 | ) | (32,627 | ) | ||||||
| Stock-based compensation expense |
17,316 | 10,685 | 2,159 | |||||||||
| Amortization of intangible assets |
2,438 | 1,286 | 869 | |||||||||
| Acquisition-related expenses |
— | 1,342 | — | |||||||||
| Impairment of long-lived assets |
— | 483 | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Non-GAAP net loss |
$ | (29,246 | ) | $ | (36,061 | ) | $ | (29,599 | ) | |||
|
|
|
|
|
|
|
|||||||
| Non-GAAP net loss per share, basic and diluted |
$ | (0.71 | ) | $ | (1.46 | ) | $ | (2.32 | ) | |||
|
|
|
|
|
|
|
|||||||
| Weighted-average common shares outstanding, basic and diluted |
41,248,473 | 24,740,480 | 12,770,916 | |||||||||
|
|
|
|
|
|
|
|||||||
Components of Results of Operations
Revenue
We generate revenue primarily from selling products, maintenance and support and professional services through a variety of delivery models to meet the needs of our diverse customer base. We generally bill customers and collect payment for both our products and services up front.
Products
We generate products revenue from the sale of (1) perpetual or term software licenses for our Nexpose, Metasploit and AppSpider products, as well as associated content subscriptions for our Nexpose and Metasploit products, (2) managed services for our Nexpose, AppSpider and InsightIDR products and (3) cloud-based subscriptions for our InsightIDR, AppSpider and Logentries products. We also generate an immaterial amount of appliance revenue that is included in our products revenue and is associated with hardware sold as part of our Nexpose product to certain customers. Revenue for perpetual software licenses and related services that are sold along with the software license is deferred on our balance sheet and recognized as revenue on our consolidated statements of operations ratably over the contractual period of the maintenance and support, which is typically one to three years.
Maintenance and Support
We generate maintenance and support revenue when customers purchase or renew agreements for maintenance and support of their Nexpose, Metasploit and AppSpider software licenses. Substantially all of our customers purchase an agreement for maintenance and support in connection with their purchase of a Nexpose, Metasploit or AppSpider software license. Revenue from maintenance and support is recognized ratably over the term of the applicable agreement.
Professional Services
We generate professional service revenue from the sale of deployment and training services related to our products, incident response services and security advisory services. Revenue from professional services sold
54
Table of Contents
together with our other software product offerings is recognized ratably over the term of the applicable agreement. Revenue from professional services sold on a stand-alone basis is recognized as those services are rendered.
Cost of Revenue
Our total cost of revenue consists of the costs of products, maintenance and support and professional services revenue.
Cost of Products
Cost of products consists of personnel and related costs for our content, managed service and cloud operations team, including salaries and other payroll related costs, bonuses, stock-based compensation and allocated overhead costs, which consist of IT, information security, recruiting, facilities and depreciation and are allocated based on relative headcount. Also included in cost of products are software license fees, hardware, cloud computing costs and internet connectivity expenses directly related to delivering our products, as well as amortization of intangible assets.
Cost of Maintenance and Support
Cost of maintenance and support consists of personnel and related costs for our support team, including salaries and other payroll related costs, bonuses, stock-based compensation and allocated overhead.
Cost of Professional Services
Cost of professional services consists of personnel and related costs for our professional services team, including salaries and other payroll related costs, bonuses, stock-based compensation, costs of contracted third-party vendors, travel and entertainment expenses and allocated overhead.
We expect our cost of revenue to increase on an absolute dollar basis as we continue to grow our revenue.
Gross Margin
Gross margin, or gross profit as a percentage of revenue, has been and will continue to be affected by a variety of factors, including the average sales price of our products and services, transaction volume growth and the mix of revenue among products and services. We expect our gross margins to fluctuate over time depending on the factors described above.
Operating Expenses
Operating expenses consist of research and development, sales and marketing, and general and administrative expenses. Operating expenses include allocated overhead costs for depreciation, facilities, IT, information security and recruiting. Our allocated costs for IT include costs for compensation of IT personnel and costs associated with our IT infrastructure. All such costs are allocated based on relative headcount.
Research and Development Expense
Research and development expense consists of personnel costs for our research and development team, including salaries and other payroll related costs, bonuses and stock-based compensation. Additional expenses include subcontracting, travel and entertainment, consulting and professional fees for third-party development resources as well as allocated overhead.
55
Table of Contents
We expect research and development expense to increase on an absolute dollar basis in the near term as we continue to increase investments in our products and technology platform innovation, but to decrease as a percentage of total revenue.
Sales and Marketing Expense
Sales and marketing expense consists of personnel costs for our sales and marketing team, including salaries and other payroll related costs, commissions, bonuses and stock-based compensation. Additional expenses include marketing activities and promotional events, travel and entertainment, training costs, amortization of certain intangible assets and allocated overhead.
We expect sales and marketing expense to increase on an absolute dollar basis in the near term as we continue to increase investments to drive our revenue growth, but to decrease as a percentage of total revenue.
General and Administrative Expense
General and administrative expense consists of personnel costs for our administrative, legal, human resources, and finance and accounting teams, including salaries and other payroll related costs, bonuses and stock-based compensation. Additional expenses include travel and entertainment, subcontracting, professional fees, insurance, acquisition-related expenses, amortization of certain intangible assets and allocated overhead.
We expect general and administrative expense to increase on an absolute dollar basis in the near term as we continue to increase investments to support our growth and operations as a public company, but to decrease as a percentage of total revenue.
Interest Income (Expense), Net
Interest income (expense), net consists primarily of interest income on our cash and cash equivalents and our short and long-term investments, and in prior years, consisted primarily of interest expense incurred on our term loan obligation including amortization of the related discount.
Other Income (Expense), Net
Other income (expense), net consists primarily of unrealized and realized gains and losses related to changes in foreign currency exchange rates.
Income Tax (Benefit) Expense
Provision for income taxes relates to U.S. federal and state, as well as certain foreign jurisdiction, income taxes. Historically, we have generated net losses in the U.S. and Ireland and recorded a full valuation allowance against our U.S. and Ireland deferred tax assets. In 2016, we recorded a valuation allowance against our U.K. deferred tax assets due to expected losses in the future. We expect to maintain a full valuation allowance on our U.S., Ireland and U.K. deferred tax assets in the near term. Realization of our U.S., Ireland and U.K. deferred tax assets depends upon future earnings, the timing and amount of which are uncertain.
56
Table of Contents
Results of Operations
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| Consolidated Statement of Operations Data: |
||||||||||||
| Revenue: |
||||||||||||
| Products |
$ | 89,404 | $ | 63,407 | $ | 47,030 | ||||||
| Maintenance and support |
37,403 | 26,903 | 19,016 | |||||||||
| Professional services |
30,630 | 20,216 | 10,834 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total revenue |
157,437 | 110,526 | 76,880 | |||||||||
| Cost of revenue:(1) |
||||||||||||
| Products |
12,447 | 6,921 | 4,557 | |||||||||
| Maintenance and support |
7,105 | 6,002 | 4,495 | |||||||||
| Professional services |
20,173 | 16,321 | 9,420 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total cost of revenue |
39,725 | 29,244 | 18,472 | |||||||||
| Operating expenses:(1) |
||||||||||||
| Research and development |
47,955 | 38,746 | 25,570 | |||||||||
| Sales and marketing |
90,524 | 67,365 | 49,007 | |||||||||
| General and administrative |
28,282 | 21,731 | 12,972 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total operating expenses |
166,761 | 127,842 | 87,549 | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss from operations |
(49,049) | (46,560) | (29,141) | |||||||||
| Interest income (expense), net |
131 | (2,523) | (2,802) | |||||||||
| Other income (expense), net |
(109) | (278) | (305) | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss before income taxes |
(49,027) | (49,361) | (32,248) | |||||||||
| Income tax (benefit) expense |
(27) | 496 | 379 | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss |
(49,000) | (49,857) | (32,627) | |||||||||
| Accretion of preferred stock to redemption value |
— | (35,061) | (52,336) | |||||||||
| Beneficial conversion charge relating to IPO participation payment |
— | (14,161) | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss attributable to common stockholders |
$ | (49,000) | $ | (99,079) | $ | (84,963) | ||||||
|
|
|
|
|
|
|
|||||||
| (1) | Cost of revenue and operating expenses include stock-based compensation expense and depreciation and amortization expense as follows: |
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| Stock-based compensation expense: |
||||||||||||
| Cost of revenue |
$ | 610 | $ | 532 | $ | 167 | ||||||
| Research and development |
6,054 | 5,010 | 499 | |||||||||
| Sales and marketing |
6,607 | 3,139 | 496 | |||||||||
| General and administrative |
4,045 | 2,004 | 997 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total stock-based compensation expense |
$ | 17,316 | $ | 10,685 | $ | 2,159 | ||||||
|
|
|
|
|
|
|
|||||||
57
Table of Contents
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| Depreciation and amortization expense: |
||||||||||||
| Cost of revenue |
$ | 2,529 | $ | 1,890 | $ | 1,275 | ||||||
| Research and development |
1,080 | 1,138 | 1,093 | |||||||||
| Sales and marketing |
1,842 | 1,617 | 1,396 | |||||||||
| General and administrative |
1,274 | 707 | 376 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total depreciation and amortization expense |
$ | 6,725 | $ | 5,352 | $ | 4,140 | ||||||
|
|
|
|
|
|
|
|||||||
The following table sets forth our consolidated statements of operations data expressed as a percentage of revenue:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Consolidated Statement of Operations Data: |
||||||||||||
| Revenue: |
||||||||||||
| Products |
56.8% | 57.4% | 61.2% | |||||||||
| Maintenance and support |
23.8 | 24.3 | 24.7 | |||||||||
| Professional services |
19.4 | 18.3 | 14.1 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total revenue |
100.0 | 100.0 | 100.0 | |||||||||
| Cost of revenue: |
||||||||||||
| Products |
7.9 | 6.3 | 5.9 | |||||||||
| Maintenance and support |
4.5 | 5.4 | 5.8 | |||||||||
| Professional services |
12.8 | 14.8 | 12.3 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total cost of revenue |
25.2 | 26.5 | 24.0 | |||||||||
| Operating expenses: |
||||||||||||
| Research and development |
30.4 | 35.1 | 33.3 | |||||||||
| Sales and marketing |
57.5 | 60.9 | 63.7 | |||||||||
| General and administrative |
18.0 | 19.7 | 16.9 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total operating expenses |
105.9 | 115.7 | 113.9 | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss from operations |
(31.1) | (42.2) | (37.9) | |||||||||
| Interest income (expense), net |
0.1 | (2.3) | (3.6) | |||||||||
| Other income (expense), net |
(0.1) | (0.2) | (0.4) | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss before income taxes |
(31.1) | (44.7) | (41.9) | |||||||||
| Provision for income taxes |
— | 0.4 | 0.5 | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss |
(31.1) | (45.1) | (42.4) | |||||||||
| Accretion of preferred stock to redemption value |
— | (31.7) | (68.1) | |||||||||
| Beneficial conversion charge relating to IPO participation payment |
— | (12.8) | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss attributable to common stockholders |
(31.1)% | (89.6)% | (110.5)% | |||||||||
|
|
|
|
|
|
|
|||||||
58
Table of Contents
Year Ended December 31, 2016 Compared to the Year Ended December 31, 2015
Revenue
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Revenue: |
||||||||||||||||
| Products |
$ 89,404 | $ 63,407 | $ 25,997 | 41.0 | % | |||||||||||
| Maintenance and support |
37,403 | 26,903 | 10,500 | 39.0 | ||||||||||||
| Professional services |
30,630 | 20,216 | 10,414 | 51.5 | ||||||||||||
|
|
|
|
|
|
|
|||||||||||
| Total revenue |
$ 157,437 | $ 110,526 | $ 46,911 | 42.4 | % | |||||||||||
|
|
|
|
|
|
|
|||||||||||
The majority of our products and maintenance and support revenue and revenue associated with professional services in a multiple-element arrangement are recognized ratably over the related contractual period of maintenance and support (typically one to three years) and accordingly $87.3 million, or 55%, of our 2016 revenue was recorded as deferred revenue on the balance sheet as of December 31, 2015, as compared to $58.2 million, or 53%, of our 2015 revenue recorded on the balance sheet as of December 31, 2014. The remaining $70.1 million of 2016 revenue was recognized from 2016 billings as compared to $52.3 million of 2015 revenue recognized from 2015 billings. Total revenue increased by $46.9 million in 2016 compared to 2015 primarily due to the $29.1 million increase in revenue recognized from our deferred revenue balance, while the remaining increase of $17.8 million was recognized in same year in which it was billed. The $17.8 million increase is due to increased purchases of additional products and services in the amount of $12.3 million by our existing customers and $5.5 million in sales to customers that were new in 2016. The increase in total revenue in 2016 was comprised of $38.6 million generated from sales in North America and $8.3 million generated from sales from the rest of the world. We added 1,074 net new customers during 2016, bringing our total customer count to 6,206 as of December 31, 2016, as compared to adding 1,399 net new customers during 2015, resulting in a total customer count of 5,132 as of December 31, 2015. Products revenue increased by $26.0 million in 2016 compared to 2015, primarily due to increased sales of perpetual software licenses and associated content subscriptions. Maintenance and support revenue increased by $10.5 million in 2016 compared to 2015, due to a continued increase in our customer base. Professional services revenue increased by $10.4 million in 2016 compared to 2015, primarily due to increased demand for our assessment services, which are primarily sold on a standalone basis, and deployment and training services, which are primarily sold with software licenses as a multiple-element arrangement.
Cost of Revenue
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Cost of revenue: |
||||||||||||||||
| Products |
$ | 12,447 | $ | 6,921 | $ | 5,526 | 79.8 | % | ||||||||
| Maintenance and support |
7,105 | 6,002 | 1,103 | 18.4 | ||||||||||||
| Professional services |
20,173 | 16,321 | 3,852 | 23.6 | ||||||||||||
|
|
|
|
|
|
|
|||||||||||
| Total cost of revenue |
$ | 39,725 | $ | 29,244 | $ | 10,481 | 35.8 | % | ||||||||
|
|
|
|
|
|
|
|||||||||||
| Gross margin %: |
||||||||||||||||
| Products |
86.1 | % | 89.1 | % | ||||||||||||
| Maintenance and support |
81.0 | 77.7 | ||||||||||||||
| Professional services |
34.1 | 19.3 | ||||||||||||||
|
|
|
|
|
|||||||||||||
| Total gross margin % |
74.8 | % | 73.5 | % | ||||||||||||
|
|
|
|
|
|||||||||||||
59
Table of Contents
Total cost of revenue increased by $10.5 million in 2016 compared to 2015, primarily due to a $5.6 million increase in personnel costs, primarily as a result of our increase in headcount from 140 as of December 31, 2015 to 164 as of December 31, 2016 as well as the timing effect of when our headcount additions were hired in 2016 and 2015, to support our growing customer base. Our increase in total cost of revenue also included a $2.8 million increase in cloud computing costs, a $0.9 million increase in allocated overhead driven largely by IT costs, a $0.6 million increase in amortization of intangible assets largely due to the Logentries acquisition, a $0.2 million increase in travel and entertainment expense and a $0.1 million increase in the costs of licenses and permits. The increase in cost of revenue in 2016 also included a write-off of obsolete appliance inventory in the amount of $0.3 million.
The total gross margin percentage increase was driven by the increase in gross margin for professional services and maintenance and support, partially offset by the decrease in gross margin for products. The increase in professional services gross margin was driven by higher utilization as well as a higher percentage of our services bookings coming from services that are sold on a standalone basis, which are recognized as delivered. The increase in maintenance and support gross margin was driven by our ability to scale as our revenue continues to grow. The decrease in products gross margin was due to an increase in revenue from cloud-based subscriptions and managed services which have lower gross margins than our software license product sales.
Operating Expenses
Research and Development Expense
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Research and development |
$ | 47,955 | $ | 38,746 | $ | 9,209 | 23.8% | |||||||||
| % of revenue |
30.4% | 35.1% | ||||||||||||||
Research and development expense increased by $9.2 million in 2016 compared to 2015 primarily due to a $6.1 million increase in personnel costs as a result of our increase in headcount of our research and development teams from 205 as of December 31, 2015 to 251 as of December 31, 2016 as well as the timing effect of when our headcount additions were hired in 2016 and 2015, to support our product innovation. Included in the increase in personnel cost was a $1.0 million increase in stock-based compensation expense and $3.1 million of additional cost attributable to the NT OBJECTives, Inc. (NTO) and Logentries acquisitions due to 2016 including a full year of expense, partially offset by $0.6 million in proceeds received from a Northern Ireland grant. Our increase in research and development expense also included a $3.7 million increase in allocated overhead driven largely by an increase in IT and facilities costs. These cost increases were offset by a $0.5 million reduction related to a charge taken in 2015 for the write off of capitalized product development costs, and a $0.1 million decrease in other expenses.
Sales and Marketing Expense
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Sales and marketing |
$ | 90,524 | $ | 67,365 | $ | 23,159 | 34.4% | |||||||||
| % of revenue |
57.5% | 60.9% | ||||||||||||||
Sales and marketing expense increased by $23.2 million in 2016 compared to 2015 primarily due to a $13.2 million increase in personnel costs, resulting from an increase in headcount from 314 as of December 31, 2015 to 346 as of December 31, 2016 as well as the timing effect of when our headcount additions were hired in
60
Table of Contents
2016 and 2015, to actively market and develop additional sales of our products and services. Included in the increase in personnel cost was a $3.5 million increase in stock-based compensation expense and $2.6 million of additional costs attributable to the Logentries acquisition due to 2016 including a full year of expense. Our increase in sales and marketing expense also included a $3.3 million increase in allocated overhead driven largely by an increase in IT and facilities costs, a $2.2 million increase in marketing expense driven largely by continued investments in attracting new customers, a $2.1 million increase in partner referral fees, a $1.2 million increase in travel and entertainment expense, a $0.7 million increase in recruiting and training costs, a $0.3 million increase in professional fees and $0.2 million of other expenses.
General and Administrative Expense
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| General and administrative |
$ | 28,282 | $ | 21,731 | $ | 6,551 | 30.1% | |||||||||
| % of revenue |
18.0% | 19.7% | ||||||||||||||
General and administrative expense increased by $6.6 million in 2016 compared to 2015 primarily due to a $3.7 million increase in personnel costs as a result of an increase in headcount from 97 as of December 31, 2015 to 126 as of December 31, 2016 as well as the timing effect of when our headcount additions were hired in 2016 and 2015, to support our overall company growth as well as operations as a public company. Included in the increase in personnel costs was a $2.0 million increase in stock-based compensation expense. Our increase in general and administrative expense also included a $0.9 million increase in professional fees related to global structuring of our intellectual property and international business operations, a $0.6 million increase in allocated overhead, driven by higher IT and facilities costs, a $0.4 million increase in recruiting and relocation costs related to certain key employees, a $0.5 million increase in amortization expense largely due to the Logentries acquisition, a $0.4 million increase in insurance costs, and $0.4 million related to a settlement and licensing agreement with a third party, partially offset by a $0.3 million decrease in other expenses.
Interest Income (Expense), Net
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Interest income (expense), net |
$ | 131 | $ | (2,523 | ) | $ | 2,654 | NM | ||||||||
| % of revenue |
0.1 | % | (2.3 | )% | ||||||||||||
Interest income (expense), net increased by $2.7 million in 2016 compared to 2015 primarily due to the repayment in full and termination of our term loan in July 2015.
Other Income (Expense), Net
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Other income (expense), net |
$ | (109 | ) | $ | (278 | ) | $ | 169 | 60.8 | % | ||||||
| % of revenue |
(0.1 | )% | (0.2 | )% | ||||||||||||
Other income (expense), net reflected a $0.2 million decrease in expense in 2016 compared to 2015 primarily due to realized and unrealized foreign currency gains and losses.
61
Table of Contents
Income Tax (Benefit) Provision
| Year Ended December 31, |
Change | |||||||||||||||
| 2016 | 2015 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Income tax (benefit) expense |
$ | (27 | ) | $ | 496 | $ | (523 | ) | 105.4 | % | ||||||
| % of revenue |
— | % | 0.4 | % | ||||||||||||
Income tax (benefit) expense decreased by $0.5 million in 2016 compared to 2015 primarily due to recognition of research and development tax credits in Canada, Ireland and the UK, as well as the impact related to the restructuring of our international business operations.
Year Ended December 31, 2015 Compared to the Year Ended December 31, 2014
Revenue
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Revenue: |
||||||||||||||||
| Products |
$ | 63,407 | $ | 47,030 | $ | 16,377 | 34.8% | |||||||||
| Maintenance and support |
26,903 | 19,016 | 7,887 | 41.5 | ||||||||||||
| Professional services |
20,216 | 10,834 | 9,382 | 86.6 | ||||||||||||
|
|
|
|
|
|
|
|||||||||||
| Total revenue |
$ | 110,526 | $ | 76,880 | $ | 33,646 | 43.8% | |||||||||
|
|
|
|
|
|
|
|||||||||||
Total revenue increased by $33.6 million in 2015 compared to 2014 primarily due to an increase of $17.8 million in revenue recognized from our deferred revenue balance. The remaining increase was the result of increased purchases of additional products and services of $8.9 million by our existing customers and $6.9 million from increased sales to new customers. The increase in total revenue in 2015 was comprised of $29.0 million from North America and $4.6 million from the rest of the world. We added 1,399 net new customers in 2015, bringing our total customer count to 5,123 as of December 31, 2015, as compared to adding 1,000 net new customers in 2014, resulting in a total customer count of 3,733 as of December 31, 2014. Products revenue and maintenance and support revenue increased by $16.3 million and $7.9 million, respectively, primarily due to the same contributors that drove our increase in total revenue. Professional services revenue increased by $9.4 million primarily due to increased demand for security advisory services.
Cost of Revenue
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Cost of revenue: |
||||||||||||||||
| Products |
$ | 6,921 | $ | 4,557 | $ | 2,364 | 51.9% | |||||||||
| Maintenance and support |
6,002 | 4,495 | 1,507 | 33.5 | ||||||||||||
| Professional services |
16,321 | 9,420 | 6,901 | 73.3 | ||||||||||||
|
|
|
|
|
|
|
|||||||||||
| Total cost of revenue |
$ | 29,244 | $ | 18,472 | $ | 10,772 | 58.3% | |||||||||
|
|
|
|
|
|
|
|||||||||||
| Gross margin %: |
||||||||||||||||
| Products |
89.1% | 90.3% | ||||||||||||||
| Maintenance and support |
77.7 | 76.4 | ||||||||||||||
| Professional services |
19.3 | 13.1 | ||||||||||||||
|
|
|
|
|
|||||||||||||
| Total gross margin % |
73.5% | 76.0% | ||||||||||||||
|
|
|
|
|
|||||||||||||
62
Table of Contents
Total cost of revenue increased by $10.8 million in 2015 compared to 2014 due to a $7.1 million increase in personnel costs, primarily as a result of our increase in headcount from 104 as of December 31, 2014 to 140 as of December 31, 2015 to support our growing customer base. Our increase in total cost of revenue also included a $1.8 million increase in allocated overhead, a $1.1 million increase in hardware and AWS cloud computing costs, a $0.5 million increase in travel and entertainment expenses and a $0.3 million increase in amortization expense. The same factors were the primary contributors to the increases in products, maintenance and support and professional services cost of revenue.
Total gross margin percentage decreased due to our revenue mix.
Operating Expenses
Research and Development Expense
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Research and development |
$ | 38,746 | $ | 25,570 | $ | 13,176 | 51.5% | |||||||||
| % of revenue |
35.1% | 33.3% | ||||||||||||||
Research and development expense increased by $13.2 million in 2015 compared to 2014 primarily due to a $10.9 million increase in personnel costs resulting from an increase in headcount from 114 as of December 31, 2014 to 205 as of December 31, 2015 to support our product innovation. Included in the increase in personnel cost was a $4.5 million increase in stock-based compensation expense and $3.1 million of additional cost attributable to the Logentries and NTO acquisitions. Our increase in research and development expense also included a $1.3 million increase in allocated overhead primarily due to IT related costs to support our growing headcount, a $0.5 million charge for the write off of capitalized product development costs due to changes in future product development plans, a $0.3 million increase in travel and entertainment expense and a $0.2 million increase in professional fees.
Sales and Marketing Expense
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Sales and marketing |
$ | 67,365 | $ | 49,007 | $ | 18,358 | 37.5% | |||||||||
| % of revenue |
60.9% | 63.7% | ||||||||||||||
Sales and marketing expense increased by $18.4 million in 2015 compared to 2014 primarily due to a $13.4 million increase in personnel costs, resulting from an increase in headcount from 227 as of December 31, 2014 to 314 as of December 31, 2015 to drive additional sales of our products and services and higher commissions expense as a result of increased customer orders. Included in the increase in personnel cost was a $2.6 million increase in stock-based compensation expense and $2.5 million of additional personnel costs attributable to the Logentries and NTO acquisitions. Our increase in sales and marketing expense also included a $2.9 million increase in allocated overhead primarily due to IT related costs to support our growing headcount, a $1.7 million increase in marketing programs, driven largely by our customer conferences and increased advertising, and a $0.4 million increase in travel and entertainment expense.
63
Table of Contents
General and Administrative Expense
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| General and administrative |
$ | 21,731 | $ | 12,972 | $ | 8,759 | 67.5% | |||||||||
| % of revenue |
19.7% | 16.9% | ||||||||||||||
General and administrative expense increased by $8.8 million in 2015 compared to 2014 primarily due to a $3.8 million increase in professional fees. The increase in professional fees was the result of costs indirectly related to our IPO, costs related to operating as a public company and $1.3 million of NTO and Logentries acquisition-related expenses. Our increase in general and administrative expense also included a $3.4 million increase in personnel costs as a result of an increase in headcount from 66 as of December 31, 2014 to 97 as of December 31, 2015 to support our overall company growth as well as operation as a public company. Included in the increase in personnel costs was a $1.0 million increase in stock-based compensation expense and $0.4 million of additional costs attributable to the acquisition of Logentries and NTO. We also had an increase of $1.3 million in allocated overhead primarily due to IT related costs to support our growing headcount and a $0.3 million increase in travel and entertainment expense.
Interest Income (Expense), Net
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Interest income (expense), net |
$ | (2,523) | $ | (2,802) | $ | 279 | 10.0% | |||||||||
| % of revenue |
(2.3)% | (3.6)% | ||||||||||||||
Interest income (expense), net increased by $0.3 million in 2015 compared to 2014 primarily due to the decreased interest expense on our term loan of $1.0 million, partially offset by an increase in debt discount amortization of $0.6 million. The increase of debt discount amortization and decrease in interest expense was due to the repayment in full and termination of our term loan in July 2015.
Other Income (Expense), Net
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Other income (expense), net |
$ | (278) | $ | (305) | $ | 27 | (8.9)% | |||||||||
| % of revenue |
(0.2)% | (0.4)% | ||||||||||||||
Other income (expense), net increased nominally in 2015 compared to 2014 primarily due to realized and unrealized foreign currency gains and losses.
Provision for Income Taxes
| Year Ended December 31, |
Change | |||||||||||||||
| 2015 | 2014 | $ | % | |||||||||||||
| (dollars in thousands) | ||||||||||||||||
| Provision for income taxes |
$ | 496 | $ | 379 | $ | 117 | 30.9% | |||||||||
| % of revenue |
0.4% | 0.5% | ||||||||||||||
64
Table of Contents
Provision for income taxes increased by $0.1 million in 2015 compared to 2014 primarily due to increased foreign taxes resulting from growth of our international operations.
Liquidity and Capital Resources
Our principal sources of liquidity are cash and cash equivalents, investments and our accounts receivable. In connection with our initial public offering, or IPO, and concurrent private placement in July 2015, we received aggregate net proceeds to us of $112.3 million, after deducting underwriting discounts and commissions related to our IPO of $8.3 million and offering expenses of $3.1 million. Prior to our IPO, we funded our operations primarily through issuances of common and redeemable convertible preferred stock and debt, including net proceeds of $93.4 million from the sale of shares of common and preferred stock. As of December 31, 2016, we had $53.1 million in cash and cash equivalents and an accumulated deficit of $389.3 million. Since our inception, we have generated significant losses and expect to continue to generate losses for the foreseeable future.
We believe that our existing cash and cash equivalents together with cash generated from our operations will be sufficient to meet our working capital expenditure requirements for at least the next 12 months. Our future capital requirements will depend on many factors, including our growth rate, the timing and extent of spending to support research and development efforts, the expansion of sales and marketing activities, particularly internationally, the introduction of new and enhanced products and professional service offerings and the cost of any future acquisitions of technology or businesses. In the event that additional financing is required from outside sources, we may be unable to raise the funds on acceptable terms, if at all. If we are unable to raise additional capital on terms satisfactory to us when we require it, our business, operating results and financial condition could be adversely affected.
The following table shows a summary of our cash flows for the years ended December 31, 2016, 2015 and 2014:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| Cash and cash equivalents at beginning of period |
$ | 86,553 | $ | 36,823 | $ | 20,612 | ||||||
| Net cash provided by (used in) operating activities |
9,112 | (1,907) | (3,356) | |||||||||
| Net cash used in investing activities |
(43,475) | (42,947) | (7,082) | |||||||||
| Net cash provided by financing activities |
1,161 | 94,786 | 26,669 | |||||||||
| Effects of exchange rates on cash |
(203) | (202) | (20) | |||||||||
|
|
|
|
|
|
|
|||||||
| Cash and cash equivalents at end of period |
$ | 53,148 | $ | 86,553 | $ | 36,823 | ||||||
|
|
|
|
|
|
|
|||||||
Uses of Funds
Our historical uses of cash have primarily consisted of cash used for operating activities such as expansion of our sales and marketing operations, research and development activities and other working capital needs, as well as cash used for investing activities such as business acquisitions and purchases of property and equipment.
Operating Activities
Operating activities provided $9.1 million of cash in 2016. Cash provided by operating activities reflected our net loss of $49.0 million, offset by a decrease in our net operating assets and liabilities of $32.8 million and non-cash charges of $25.3 million related primarily to depreciation and amortization, stock-based compensation expense, provision for doubtful accounts and other non-cash charges. The decrease in our net operating assets and liabilities was primarily due to a $38.7 million increase in deferred revenue from sales of our products and
65
Table of Contents
services, a $1.6 million increase in accrued expenses, a $1.6 million increase in accounts payable and a $0.6 million increase in other liabilities, which all had a positive impact on operating cash flow. These factors were offset by a $6.2 million increase in accounts receivable and a $3.5 million increase in prepaid expenses and other assets, which each had a negative impact on operating cash flow.
Operating activities used $1.9 million in cash in 2015, which reflected continued growth in revenue, offset by continuing investment in our operations. Cash used in operating activities reflected our net loss of $49.9 million, partially offset by a net decrease in our net operating assets and liabilities of $29.0 million and non-cash charges of $19.0 million related to depreciation and amortization, stock-based compensation, provision for doubtful accounts and other non-cash charges such as amortization of debt discount, impairment of long-lived assets and non-cash interest expense. The decrease in our net operating assets and liabilities was primarily due to a $44.8 million increase in deferred revenue from sales of our products and services and a $6.7 million increase in accrued expenses, partially offset by a $18.4 million increase in accounts receivable, a $2.3 million decrease in accounts payable and a $1.8 million increase in prepaid expenses and other assets.
Operating activities used $3.4 million of cash in 2014, which reflected growth in revenue, offset by continuing investment in our operations. Cash used in operating activities reflected our net loss of $32.6 million, offset by a net decrease in our net operating assets and liabilities of $21.6 million and non-cash charges of $7.6 million related to depreciation and amortization, stock-based compensation and provision for doubtful accounts. The decrease in our net operating assets and liabilities was primarily due to a $25.2 million increase in deferred revenue from sales of our products and services, a $3.5 million increase in accrued expense, a $2.2 million increase in other liabilities and a $0.6 million increase in accounts payable, partially offset by an increase of $7.1 million in accounts receivable and an increase of $2.2 million in prepaid expenses.
Investing Activities
Investing activities used $43.5 million of cash in 2016, consisting of $39.0 million used for purchases of investments and $4.5 million in capital expenditures to purchase equipment and leasehold improvements.
Investing activities used $42.9 million in cash in 2015, primarily for the acquisition of Logentries and NTO for $35.5 million and $3.3 million, respectively. Additionally, $4.1 million was used to purchase property and equipment.
Investing activities used $7.1 million in cash in 2014, primarily for capital expenditures to purchase property and equipment, principally related to leasehold improvements for our new corporate headquarters.
Financing Activities
Financing activities provided $1.2 million of cash in 2016, which consisted primarily of $3.7 million in proceeds from the issuance of common shares purchased by employees under the Rapid7, Inc. 2015 Employee Stock Purchase Plan, or ESPP, $2.9 million in proceeds from the exercise of stock options and $0.1 million related to an excess tax benefit from stock-based compensation, partially offset by $4.1 million in withholding taxes paid for the net share settlement of equity awards and a $1.4 million payment related to the deferred acquisition consideration associated with the NTO acquisition in 2015.
Financing activities provided $94.8 million in 2015, which consisted of net proceeds from our IPO and concurrent private placement of $112.3 million and proceeds from stock option exercises of $1.3 million, partially offset by the repayment of our term loan and related termination payment of $18.5 million and payments on capital lease obligations of $0.3 million.
Financing activities provided $26.7 million in cash in 2014, which consisted primarily of $30.8 million in net proceeds from the issuance of shares of Series D redeemable convertible preferred stock and $0.5 million in
66
Table of Contents
proceeds from exercises of stock options, partially offset by $3.5 million in repurchases of common stock, $0.8 million in payments of contingent consideration related to acquisitions and $0.3 million in payments on capital lease obligations.
Contractual Obligations and Commitments
The following table summarizes our commitments to settle contractual obligations as of December 31, 2016:
| Less than 1 Year |
1 to 3 Years |
3 to 5 Years |
More than 5 Years |
Total | ||||||||||||||||
| (in thousands) | ||||||||||||||||||||
| Operating leases |
$ | 6,282 | $ | 9,583 | $ | 2,018 | $ | 1,767 | $ | 19,650 | ||||||||||
| Non-cancelable purchase obligations |
2,106 | 4,066 | — | — | 6,172 | |||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
| Total |
$ | 8,388 | $ | 13,649 | $ | 2,018 | $ | 1,767 | $ | 25,822 | ||||||||||
|
|
|
|
|
|
|
|
|
|
|
|||||||||||
The commitment amounts in the table above are associated with agreements that are enforceable and legally binding. The table does not include obligations under agreements that we can cancel without a significant penalty.
We lease our office facilities under non-cancellable operating leases. As of December 31, 2016, we have leases that expire at various dates through 2027.
Off-Balance Sheet Arrangements
We do not have any relationships with unconsolidated entities or financial partnerships, including entities sometimes referred to as structured finance or special purpose entities that were established for the purpose of facilitating off-balance sheet arrangements or other contractually narrow or limited purposes. We do not engage in off-balance sheet financing arrangements. In addition, we do not engage in trading activities involving non-exchange traded contracts. We therefore believe that we are not materially exposed to any financing, liquidity, market or credit risk that could arise if we had engaged in these relationships.
Critical Accounting Policies
Our consolidated financial statements are prepared in accordance with generally accepted accounting principles in the United States, or GAAP. The preparation of our consolidated financial statements requires us to make estimates, assumptions and judgments that affect the reported amounts of assets, liabilities, revenue, costs and expenses. We base our estimates and assumptions on historical experience and other factors that we believe to be reasonable under the circumstances. We evaluate our estimates and assumptions on an ongoing basis. Our actual results may differ from these estimates. Our most critical accounting policies are summarized below. See Note 2 to our consolidated financial statements included in this Annual Report on Form 10-K for a description of our other significant accounting policies.
Revenue Recognition
We generate revenue primarily from selling products, maintenance and support, and professional services through a variety of delivery models. We generally bill customers and collect payment for both our products and services up front.
We generate products revenue from the sale of (1) perpetual or term software licenses for our Nexpose, Metasploit and AppSpider products, and associated content subscriptions for our Nexpose and Metasploit products, (2) managed services for our Nexpose, AppSpider and InsightIDR products and (3) cloud-based
67
Table of Contents
subscriptions for our InsightIDR, Logentries and AppSpider products. We also generate an immaterial amount of appliance revenue that is included in our products revenue and that is associated with hardware sold as part of our Nexpose product to certain customers. We generate maintenance and support revenue associated with customers’ purchases of our software licenses for Nexpose, Metasploit, and AppSpider. We generate professional service revenue from the sale of our deployment and training services related to our solutions, incident response services and security advisory services.
Revenue is only recognized when all of the following criteria are met:
| • | Persuasive evidence of an arrangement exists. Binding agreements or purchase orders are generally evidence of an arrangement. |
| • | Delivery has occurred. Delivery occurs (1) upon delivery of the software license key or when the customer has access to the software product or (2) when we perform the services. |
| • | The sales price is fixed or determinable. Fees are considered fixed and determinable when the fees are contractually agreed upon with the customer. |
| • | Collectability is probable. Collectability is deemed probable based on review of a number of factors, including creditworthiness and customer payment history. If collectability is not probable, revenue is deferred until collection becomes probable, which is generally upon the receipt of payment. |
Substantially all of our software licenses are sold in multiple-element arrangements that include maintenance and support and content subscriptions, and in addition could include cloud-based subscriptions, professional services and/or managed services. All of these elements are considered to be software elements other than cloud-based subscriptions, which are non-software elements, and managed services, which can be either software elements or non-software elements. Non-software elements included in multiple-element arrangements consist of a single deliverable that has stand-alone value and that represents a single unit of accounting. We have determined that we do not have vendor-specific objective evidence, or VSOE, of the selling price for the elements comprising these multiple-element arrangements as our software licenses are generally not sold on a stand-alone basis and we purposefully employ variable pricing for our offerings in order to meet customer purchase requirements along the multiple price points of the demand curve.
When all of the elements of a multiple-element arrangement are software elements, the revenue for software licenses and any other products and services that are sold along with the license is generally deferred on our balance sheet and recognized as revenue on our consolidated statements of operations ratably over the contractual period of the maintenance and support, typically one to three years, which is longer than the period over which the professional services are performed. Revenue recognition begins upon delivery of the software license, assuming that all other criteria for revenue recognition have been met.
When a multiple-element arrangement includes both software elements and non-software elements, the total arrangement consideration is first allocated between the software elements and the non-software elements based on the selling price hierarchy, which includes (1) VSOE, if available, (2) third-party evidence, or TPE, if VSOE is not available or (3) best estimate of selling price, or BESP, if neither VSOE nor TPE is available. We have not been able to establish a selling price for any element using VSOE or TPE. We determine BESP by considering our overall pricing objectives and market conditions. Significant pricing practices taken into consideration include our discounting practices, the size and volume of our transactions, our price lists, our go-to-market strategy, historical standalone sales and contract prices. The determination of BESP is made in consultation with, and is approved by, our management. Our multiple-element arrangements can include a single non-software element, in which case the portion of the consideration allocated to the non-software element is recognized ratably over the service period of the non-software element, assuming all other criteria for revenue recognition have been met. The portion of the consideration allocated to software elements is recognized as described above.
68
Table of Contents
With respect to our managed services and cloud-based subscription offerings sold on a stand-alone basis, we recognize revenue ratably over the term of the managed service agreement or subscription, assuming that the other criteria for revenue recognition are met.
We recognize revenue from professional services sold on a stand-alone basis as those services are rendered.
For purposes of disclosing revenue by class, we allocate the arrangement consideration for multiple-element software arrangements among the individual elements utilizing BESP, as we do not have VSOE or TPE of selling price for any of the elements.
Stock-Based Compensation
We measure and recognize compensation expense for all stock options, restricted stock awards, or RSAs, and restricted stock units, or RSUs, based on the estimated fair value of the award on the grant date. The fair value is recognized as expense, net of estimated forfeitures, over the requisite service period, which is generally the vesting period of the respective award, on a straight-line basis when the only condition to vesting is continued service. If vesting is subject to a market or performance condition, recognition is based on the derived service period of the award. Expense for awards with performance conditions is estimated and adjusted on a quarterly basis based upon the assessment of the probability that the performance condition will be met.
We use the Black-Scholes option pricing model to estimate the fair value of stock option awards. The Black-Scholes option pricing model requires management to make a number of other assumptions, including the expected life of the option, the volatility of the underlying stock, the risk-free interest rate and expected dividends. The assumptions used in our Black-Scholes option-pricing model represent management’s best estimates at the time of grant. These estimates are complex, involve a number of variables, uncertainties and assumptions and the application of management’s judgment, as they are inherently subjective. If any assumptions change, our stock-based compensation expense could be materially different in the future.
These assumptions are estimated as follows:
| • | Fair Value of Common Stock. Prior to our IPO, we estimated the fair value of common stock considering a number of objective and subjective factors, including contemporaneous third-party valuations of our common stock. For stock options granted subsequent to our IPO in July 2015, the fair value of common stock is based on the closing price of our common stock as reported on the NASDAQ Global Market on the date of grant. |
| • | Expected Term. The expected term represents the period that our stock options are expected to be outstanding. We calculated the expected term using the simplified method based on the average of each option’s vesting term and the contractual period during which the option can be exercised, which is typically 10 years following the date of grant. |
| • | Expected Volatility. We determine the price volatility factor based on the historical volatilities of our publicly traded peer group as we do not have a significant trading history for our common stock. Industry peers consist of several public companies in the technology industry that are similar to us in size, stage of life cycle, and financial leverage. We used the same set of peer group companies in all the relevant valuation estimates. We intend to continue to consistently apply this process using the same or similar public companies until a sufficient amount of historical information regarding the volatility of our own common stock share price becomes available, or unless circumstances change such that the identified companies are no longer similar to us, in which case, more suitable companies whose share prices are publicly available would be utilized in the calculation. |
| • | Risk-Free Interest Rate. The risk-free interest rate was based on U.S. Treasury zero-coupon securities with maturities consistent with the estimated expected term. |
| • | Expected Dividend Yield. We have not paid dividends on our common stock nor do we expect to pay dividends in the foreseeable future. |
69
Table of Contents
The fair values of RSAs and RSUs are based on the closing market price of our common stock on the NASDAQ Global Market on the date of grant.
We estimate the fair value of the rights to acquire stock under our ESPP using the Black-Scholes option pricing formula. Our ESPP provides for a twelve-month offering period which contains two purchase periods of approximately six months in duration. We use our peer group volatility data in the valuation of ESPP shares. We recognize such compensation expense on a straight-line basis over the employee’s requisite service period.
Income Taxes
Income taxes are accounted for using the asset and liability method. Under this method, deferred tax assets and liabilities are recognized for differences between the financial statement carrying amounts of existing assets and liabilities and their respective income tax bases, and operating loss and tax credit carryforwards using tax rates expected to be in effect in the years in which the differences are expected to reverse. Deferred tax assets are reduced by a valuation allowance if it is more likely than not that all of, or a portion of, deferred tax assets will not be utilized in the future.
We account for unrecognized tax benefits using a more-likely-than-not threshold for financial statement recognition and measurement of tax positions taken or expected to be taken in a tax return. Interest and penalties associated with such uncertain tax positions are classified as a component of income tax expense.
Significant judgment is required in determining any valuation allowance recorded against deferred tax assets. In assessing the need for a valuation allowance, we consider all available evidence, including past operating results, estimates of future taxable income and the feasibility of tax planning strategies. In the event that we change our determination as to the amount of deferred tax assets that can be realized, we will adjust our valuation allowance with a corresponding impact to the provision for income taxes in the period in which such determination is made.
Estimates of future taxable income are based on assumptions that are consistent with our plans. Assumptions represent management’s best estimates and involve inherent uncertainties and the application of management’s judgment. Should actual amounts differ from our estimates, the amount of our tax expense and liabilities could be materially impacted.
Goodwill and Other Intangible Assets
Goodwill is an asset representing the future economic benefits arising from other assets acquired in a business combination that are not individually identified and separately recognized. We allocate the cost of an acquired entity to the assets acquired and liabilities assumed based on their estimated fair values at the date of acquisition. The excess of the purchase price for acquisitions over the fair value of the net assets acquired, including other intangible assets, is recorded as goodwill. Goodwill is not amortized but is tested for impairment at least annually or more frequently when events or circumstances occur that indicate that it is more likely than not that an impairment has occurred.
For our goodwill impairment analysis, we operate with a single reporting unit. We test goodwill for impairment on the last day of each fiscal year and whenever events or changes in circumstances indicate that the carrying amount of this asset may exceed its fair value. To test goodwill impairment, we perform the two-step goodwill impairment test to identify potential goodwill impairment. The two step impairment test begins with an estimation of the fair value of a reporting unit. Goodwill impairment exists when a reporting unit’s carrying value of goodwill exceeds its implied fair value. Significant judgment is applied when goodwill is assessed for impairment. In performing the first step of the goodwill impairment testing and measurement process, we estimated the fair value of our single reporting unit using our market capitalization. Based upon our assessment performed as of December 31, 2016, we concluded the fair value of our single reporting unit exceeded its carrying value and there was no impairment of goodwill.
70
Table of Contents
Other intangible assets acquired in a business combination are recognized at fair value using generally accepted valuation methods appropriate for the type of intangible asset and reported separately from goodwill. Intangible assets with definite lives are amortized over the estimated useful lives and are tested for impairment when events or circumstances occur that indicate that it is more likely than not that an impairment has occurred. For the year ended December 31, 2016, we determined there were no indicators of impairment of our other intangible assets.
Recent Accounting Pronouncements
In October 2016, the Financial Accounting Standards Board (FASB) issued Accounting Standards Update (ASU) 2016-16, Income Taxes (Topic 740): Intra-Entity Transfers of Assets Other Than Inventory. The ASU is intended to improve the accounting for the income tax consequences of intra-entity transfers of assets other than inventory. Current GAAP prohibits the recognition of current and deferred income taxes for an intra-entity asset transfer until the asset has been sold to an outside party. The ASU will allow an entity to recognize the income tax consequences of these transfers when the transfers occur. The ASU will be effective for us in the first quarter of 2018. We are currently evaluating the impact that the adoption of this ASU will have on our consolidated financial statements.
In March 2016, the FASB issued ASU 2016-09, Compensation-Stock Compensation (Topic 718): Improvements to Employee Share-Based Payment Accounting. The ASU is intended to simplify several aspects of the accounting for share-based payment transactions, including the accounting for income taxes, forfeitures and statutory tax withholding requirements, as well as classification on the statement of cash flows. The ASU will be effective for us in the first quarter of 2017. We do not expect this ASU to have a material impact on our consolidated financial statements.
In February 2016, the FASB issued ASU 2016-02, Leases (Topic 842). The ASU requires companies to recognize on the balance sheet the assets and liabilities for the rights and obligations created by leased assets. The ASU will be effective for us in the first quarter of 2019, with early adoption permitted. We are currently evaluating the impact that the adoption of this ASU will have on our consolidated financial statements.
In November 2015, the FASB issued ASU 2015-17, Income Taxes (Topic 740): Balance Sheet Classification of Deferred Taxes. The ASU requires that deferred tax liabilities and assets be classified as noncurrent in a classified balance sheet simplifying current GAAP, which requires an entity to separate deferred tax liabilities and assets into current and noncurrent amounts in the balance sheet. The ASU may be applied prospectively or retrospectively at our election. We early adopted this ASU effective December 31, 2016. As a result, we have presented all deferred tax assets and liabilities as noncurrent on our consolidated balance sheet as of December 31, 2016, but have not reclassified current deferred tax assets and liabilities on our consolidated balance sheet as of December 31, 2015. Our consolidated financial statements were not materially impacted as a result of the adoption of this ASU.
In September 2015, the FASB issued ASU 2015-16, Business Combinations (Topic 805): Simplifying the Accounting for Measurement-Period Adjustments. The ASU eliminates the requirement for an acquirer in a business combination to account for measurement-period adjustments retrospectively. The new guidance requires that the cumulative impact of a measurement-period adjustment (including the impact on prior periods) be recognized in the reporting period in which the adjustment is identified. This ASU was adopted on January 1, 2016 and did not have a material impact on our consolidated financial statements.
In April 2015, the FASB issued ASU 2015-05, Intangibles – Goodwill and Other – Internal Use Software (Subtopic 350-40): Customer’s Accounting for Fees Paid in a Cloud Computing Arrangement, which provides guidance on accounting for fees paid in a cloud computing arrangement. Under the ASU, if a cloud computing arrangement includes a software license, which also grants the contractual rights and practical ability to take possession of the software, the software license element should be accounted for consistent with the purchase of other software licenses. If the cloud computing arrangement does not include a software license, as defined, it
71
Table of Contents
should be accounted for as a service contract. This ASU was adopted on January 1, 2016 and did not have a material impact on our consolidated financial statements.
In August 2014, the FASB issued ASU 2014-15, Presentation of Financial Statements – Going Concern (Subtopic 201-40): Disclosure of Uncertainties about an Entity’s Ability to Continue as a Going Concern. The ASU provides guidance on how and when reporting entities must disclose going-concern uncertainties in their financial statements. This ASU became effective for us on January 1, 2016. Our consolidated financial statements were not materially impacted as a result of the adoption of this ASU.
In May 2014, the FASB issued ASU 2014-09, Revenue from Contracts with Customers (Topic 606). The ASU outlines a single, comprehensive model for accounting for revenue from contracts with customers and requires more detailed disclosure to enable users of financial statements to understand the nature, amount, timing and uncertainty of revenue and cash flows arising from such contracts. In August 2015, the FASB issued ASU 2015-14, which provides a one year deferral in the effective date of ASU 2014-09. ASU 2014-09 will now be effective for us beginning January 1, 2018; however, early adoption will be permitted as of the original effective date.
We will adopt ASU 2014-09 in the first quarter of 2018 and expect to adopt on a modified retrospective basis. Under this method of adoption, we would recognize the cumulative effect of initially applying the standard as an adjustment to the opening balance of retained earnings in the period of initial application. Comparative prior year periods would not be adjusted. We are currently evaluating the potential impact of this standard on our financial position and results of operations. Based on the analysis performed to date, we expect revenue recognition related to our perpetual and term software licenses, managed services, cloud-based subscriptions and stand-alone professional services to remain substantially unchanged. However, under the new standard, for software licenses that are sold with professional services in a multiple-element arrangement, the professional services will likely represent a separate performance obligation and we will recognize revenue associated with the professional services as such services are performed. Revenue associated with professional services in a multiple-element arrangement is currently recognized ratably over the related contractual period of maintenance and support (typically one to three years) due to the lack of VSOE of selling price for the elements. Additionally, under the new standard, we expect to capitalize and amortize commissions relating to multiyear contracts rather than expensing them as incurred in the period that the commissions are earned by our employees (which is typically upon signing of an arrangement).
Item 7A. Quantitative and Qualitative Disclosures About Market Risk.
Foreign Currency Exchange Risk
Our results of operations and cash flows are subject to fluctuations due to changes in foreign currency exchange rates. Substantially all of our customers enter into contracts that are denominated in U.S. dollars. Our expenses are generally denominated in the currencies of the countries where our operations are located, which is primarily in the United States and to a lesser extent in the United Kingdom, other Euro-zone countries within mainland Europe, Canada, Hong Kong, Singapore and Australia. Our results of operations and cash flows are, therefore, subject to fluctuations due to changes in foreign currency exchange rates and may be adversely affected in the future due to changes in foreign currency exchange rates. During the years ended December 31, 2016 and 2015, the effect of a hypothetical 10% adverse change in foreign currency exchange rates on monetary assets and liabilities would not have been material to our financial condition or results of operations. To date, we have not engaged in any hedging strategies. As our international operations grow, we will continue to reassess our approach to manage our risk relating to fluctuations in foreign currency rates.
Interest Rate Risk
Our portfolio of cash and cash equivalents and short- and long-term investments is maintained in a variety of securities, including money market funds, commercial paper, corporate bonds, U.S. government agencies and
72
Table of Contents
asset-backed securities. Investments are classified as available-for-sale securities and carried at their fair market value with cumulative unrealized gains or losses recorded as a component of accumulated other comprehensive loss within stockholders’ equity. A sharp rise in interest rates could have an adverse impact on the fair market value of certain securities in our portfolio. We do not currently hedge our interest rate exposure and do not enter into financial instruments for trading or speculative purposes.
During the years ended December 31, 2016 and 2015, the effect of a hypothetical 10% increase or decrease in overall interest rates would not have had a material impact on our financial statements.
Inflation Risk
We do not believe that inflation had a material effect on our business, financial condition or results of operations in the last three years. If our costs were to become subject to significant inflationary pressures, we may not be able to fully offset such higher costs through price increases. Our inability or failure to do so could harm our business, financial condition and results of operations.
73
Table of Contents
Item 8. Financial Statements and Supplementary Data.
INDEX TO CONSOLIDATED FINANCIAL STATEMENTS
| Consolidated Financial Statements: |
||||
| 75 | ||||
| 76 | ||||
| 77 | ||||
| 78 | ||||
| 79 | ||||
| 80 | ||||
| 81 |
74
Table of Contents
REPORT OF INDEPENDENT REGISTERED PUBLIC ACCOUNTING FIRM
The Board of Directors and Stockholders
Rapid7, Inc.:
We have audited the accompanying consolidated balance sheets of Rapid7, Inc. and subsidiaries as of December 31, 2016 and 2015, and the related consolidated statements of operations, comprehensive loss, changes in redeemable convertible preferred stock and stockholders’ equity (deficit), and cash flows for each of the years in the three-year period ended December 31, 2016. These consolidated financial statements are the responsibility of the Company’s management. Our responsibility is to express an opinion on these consolidated financial statements based on our audits.
We conducted our audits in accordance with the standards of the Public Company Accounting Oversight Board (United States). Those standards require that we plan and perform the audit to obtain reasonable assurance about whether the financial statements are free of material misstatement. An audit includes examining, on a test basis, evidence supporting the amounts and disclosures in the financial statements. An audit also includes assessing the accounting principles used and significant estimates made by management, as well as evaluating the overall financial statement presentation. We believe that our audits provide a reasonable basis for our opinion.
In our opinion, the consolidated financial statements referred to above present fairly, in all material respects, the financial position of Rapid7, Inc. and subsidiaries as of December 31, 2016 and 2015, and the results of their operations and their cash flows for each of the years in the three-year period ended December 31, 2016, in conformity with U.S. generally accepted accounting principles.
/s/ KPMG LLP
Boston, Massachusetts
March 9, 2017
75
Table of Contents
CONSOLIDATED BALANCE SHEETS
(in thousands, except share and per share data)
| December 31, 2016 | December 31, 2015 | |||||||
| Assets |
||||||||
| Current assets: |
||||||||
| Cash and cash equivalents |
$ 53,148 | $ 86,553 | ||||||
| Short-term investments |
18,779 | — | ||||||
| Accounts receivables, net |
49,154 | 44,164 | ||||||
| Prepaid expenses and other current assets |
9,152 | 6,148 | ||||||
|
|
|
|
|
|||||
| Total current assets |
130,233 | 136,865 | ||||||
| Long-term investments |
20,162 | — | ||||||
| Property and equipment, net |
8,088 | 7,532 | ||||||
| Goodwill |
75,110 | 74,565 | ||||||
| Intangible assets, net |
8,946 | 11,385 | ||||||
| Other assets |
764 | 214 | ||||||
|
|
|
|
|
|||||
| Total assets |
$ 243,303 | $ 230,561 | ||||||
|
|
|
|
|
|||||
| Liabilities and Stockholders’ Equity |
||||||||
| Current liabilities: |
||||||||
| Accounts payable |
4,012 | 2,038 | ||||||
| Accrued expenses |
23,499 | 24,707 | ||||||
| Deferred revenue, current portion |
116,903 | 87,917 | ||||||
| Other current liabilities |
1,195 | 1,105 | ||||||
|
|
|
|
|
|||||
| Total current liabilities |
145,609 | 115,767 | ||||||
| Deferred revenue, non-current portion |
52,160 | 42,400 | ||||||
| Other long-term liabilities |
3,496 | 4,319 | ||||||
|
|
|
|
|
|||||
| Total liabilities |
201,265 | 162,486 | ||||||
| Stockholders’ equity: |
||||||||
| Preferred stock, $0.01 par value per share; 10,000,000 shares authorized at December 31, 2016 and 2015; 0 shares issued and outstanding at December 31, 2016 and 2015 |
— | — | ||||||
| Common stock, $0.01 par value; 100,000,000 shares authorized at December 31, 2016 and 2015; 43,018,737 and 41,942,026 shares issued at December 31, 2016 and 2015, respectively; 42,554,683 and 41,540,400 shares outstanding at December 31, 2016 and 2015, respectively |
426 | 415 | ||||||
| Treasury stock, at cost, 464,054 and 401,626 shares at December 31, 2016 and 2015, respectively |
(4,391) | (3,526) | ||||||
| Additional paid-in-capital |
435,360 | 411,524 | ||||||
| Accumulated other comprehensive loss |
(19) | — | ||||||
| Accumulated deficit |
(389,338) | (340,338) | ||||||
|
|
|
|
|
|||||
| Total stockholders’ equity |
42,038 | 68,075 | ||||||
|
|
|
|
|
|||||
| Total liabilities and stockholders’ equity |
$ 243,303 | $ 230,561 | ||||||
|
|
|
|
|
|||||
See accompanying notes to consolidated financial statements.
76
Table of Contents
CONSOLIDATED STATEMENTS OF OPERATIONS
(in thousands, except share and per share data)
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Revenue: |
||||||||||||
| Products |
$ 89,404 | $ 63,407 | $ 47,030 | |||||||||
| Maintenance and support |
37,403 | 26,903 | 19,016 | |||||||||
| Professional services |
30,630 | 20,216 | 10,834 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total revenue |
157,437 | 110,526 | 76,880 | |||||||||
| Cost of revenue: |
||||||||||||
| Products |
12,447 | 6,921 | 4,557 | |||||||||
| Maintenance and support |
7,105 | 6,002 | 4,495 | |||||||||
| Professional services |
20,173 | 16,321 | 9,420 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total cost of revenue |
39,725 | 29,244 | 18,472 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total gross profit |
117,712 | 81,282 | 58,408 | |||||||||
|
|
|
|
|
|
|
|||||||
| Operating expenses: |
||||||||||||
| Research and development |
47,955 | 38,746 | 25,570 | |||||||||
| Sales and marketing |
90,524 | 67,365 | 49,007 | |||||||||
| General and administrative |
28,282 | 21,731 | 12,972 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total operating expenses |
166,761 | 127,842 | 87,549 | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss from operations |
(49,049) | (46,560) | (29,141) | |||||||||
| Other income (expense), net: |
||||||||||||
| Interest income (expense), net |
131 | (2,523) | (2,802) | |||||||||
| Other income (expense), net |
(109) | (278) | (305) | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss before income taxes |
(49,027) | (49,361) | (32,248) | |||||||||
| Income tax (benefit) expense |
(27) | 496 | 379 | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss |
(49,000) | (49,857) | (32,627) | |||||||||
| Accretion of preferred stock to redemption value |
— | (35,061) | (52,336) | |||||||||
| Beneficial conversion charge relating to IPO participation payment |
— | (14,161) | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss attributable to common stockholders |
$ (49,000) | $ (99,079) | $ (84,963) | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss per share attributable to common stockholders, basic and diluted |
$ (1.19) | $ (4.00) | $ (6.65) | |||||||||
|
|
|
|
|
|
|
|||||||
| Weighted-average common shares outstanding, basic and diluted |
41,248,473 | 24,740,480 | 12,770,916 | |||||||||
|
|
|
|
|
|
|
|||||||
See accompanying notes to consolidated financial statements.
77
Table of Contents
CONSOLIDATED STATEMENTS OF COMPREHENSIVE LOSS
(in thousands)
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Net loss |
$ (49,000) | $ (49,857) | $ (32,627) | |||||||||
| Other comprehensive loss: |
||||||||||||
| Net unrealized loss on investments |
(19) | — | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Comprehensive loss |
$ (49,019) | $ (49,857) | $ (32,627) | |||||||||
|
|
|
|
|
|
|
|||||||
See accompanying notes to consolidated financial statements.
78
Table of Contents
CONSOLIDATED STATEMENTS OF CHANGES IN REDEEMABLE CONVERTIBLE PREFERRED STOCK AND STOCKHOLDERS’ EQUITY (DEFICIT)
(in thousands)
| Redeemable convertible preferred stock |
Common stock | Treasury stock | Additional paid-in-capital |
Accumulated other comprehensive income |
Accumulated deficit |
Total stockholders’ equity (deficit) |
||||||||||||||||||||||||||||||||||
| Shares | Amount | Shares | Amount | Shares | Amount | |||||||||||||||||||||||||||||||||||
| Balance, December 31, 2013 |
13,696 | $ | 128,444 | 12,764 | $ | 128 | — | $ | — | $ | — | $ | — | $ | (161,149) | $ | (161,021) | |||||||||||||||||||||||
| Stock-based compensation |
— | — | — | — | — | — | 2,159 | — | — | 2,159 | ||||||||||||||||||||||||||||||
| Accretion of preferred stock to redemption value |
— | 52,336 | — | — | — | — | (2,650) | — | (49,686) | (52,336) | ||||||||||||||||||||||||||||||
| Issuance of Series D redeemable convertible preferred stock, net of issuance costs |
2,686 | 30,818 | — | — | — | — | — | — | — | — | ||||||||||||||||||||||||||||||
| Issuance of common stock upon exercise of stock options |
— | — | 201 | 2 | — | — | 487 | — | — | 489 | ||||||||||||||||||||||||||||||
| Purchase of common stock |
— | — | (402) | (4) | 402 | (3,526) | 4 | — | — | (3,526) | ||||||||||||||||||||||||||||||
| Net loss |
— | — | — | — | — | — | — | — | (32,627) | (32,627) | ||||||||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||||
| Balance, December 31, 2014 |
16,382 | $ | 211,598 | 12,563 | $ | 126 | 402 | $ | (3,526) | $ | — | $ | — | $ | (243,462) | $ | (246,862) | |||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||||
| Stock-based compensation |
— | — | — | — | — | — | 10,685 | — | — | 10,685 | ||||||||||||||||||||||||||||||
| Accretion of preferred stock to redemption value |
— | 35,061 | — | — | — | — | (2,203) | — | (32,858) | (35,061) | ||||||||||||||||||||||||||||||
| Conversion of preferred stock to common stock |
(16,382) | (246,659) | 16,382 | 164 | — | — | 246,495 | — | — | 246,659 | ||||||||||||||||||||||||||||||
| IPO participation payment and beneficial conversion charge |
— | — | 1,940 | 19 | — | — | 14,142 | — | (14,161) | — | ||||||||||||||||||||||||||||||
| Issuance of common stock in relation to IPO and concurrent private placement, net of offering costs |
— | — | 7,730 | 77 | — | — | 112,198 | — | — | 112,275 | ||||||||||||||||||||||||||||||
| Issuance of common stock and options associated with acquisitions |
— | — | 1,262 | 13 | — | — | 31,962 | — | — | 31,975 | ||||||||||||||||||||||||||||||
| Issuance of restricted stock |
— | — | 1,358 | 13 | — | — | (13) | — | — | — | ||||||||||||||||||||||||||||||
| Shares withheld for employee taxes |
— | — | (134) | (1) | — | — | (3,086) | — | — | (3,087) | ||||||||||||||||||||||||||||||
| Issuance of common stock upon exercise of stock options and warrants |
— | — | 439 | 4 | — | — | 1,344 | — | — | 1,348 | ||||||||||||||||||||||||||||||
| Net loss |
— | — | — | — | — | — | — | — | (49,857) | (49,857) | ||||||||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||||
| Balance, December 31, 2015 |
— | $ | — | 41,540 | $ | 415 | 402 | $ | (3,526) | $ | 411,524 | $ | — | $ | (340,338) | $ | 68,075 | |||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||||
| Stock-based compensation |
— | — | — | — | — | — | 17,316 | — | — | 17,316 | ||||||||||||||||||||||||||||||
| Issuance of common stock under ESPP |
— | — | 346 | 4 | — | — | 3,720 | — | — | 3,724 | ||||||||||||||||||||||||||||||
| Vesting of restricted stock units |
— | — | 91 | 1 | — | — | (1) | — | — | — | ||||||||||||||||||||||||||||||
| Forfeiture of restricted stock awards |
— | — | (27) | — | — | — | — | — | — | — | ||||||||||||||||||||||||||||||
| Shares withheld for employee taxes |
— | — | (74) | (1) | 62 | (865) | (160) | — | — | (1,026) | ||||||||||||||||||||||||||||||
| Excess tax benefit from stock-based compensation |
— | — | — | — | — | — | 87 | — | — | 87 | ||||||||||||||||||||||||||||||
| Issuance of common stock upon exercise of stock options and warrants |
— | — | 679 | 7 | — | — | 2,874 | — | — | 2,881 | ||||||||||||||||||||||||||||||
| Net unrealized loss on investments |
— | — | — | — | — | — | — | (19) | — | (19) | ||||||||||||||||||||||||||||||
| Net loss |
— | — | — | — | — | — | — | — | (49,000) | (49,000) | ||||||||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||||
| Balance, December 31, 2015 |
— | $ | — | 42,555 | $ | 426 | 464 | $ | (4,391) | $ | 435,360 | $ | (19) | $ | (389,338) | $ | 42,038 | |||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||||||
See accompanying notes to consolidated financial statements.
79
Table of Contents
CONSOLIDATED STATEMENTS OF CASH FLOWS
(in thousands)
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Cash flows from operating activities: |
||||||||||||
| Net loss |
$ | (49,000) | $ | (49,857) | $ | (32,627) | ||||||
| Adjustments to reconcile net loss to net cash provided by (used in) operating activities: |
||||||||||||
| Depreciation and amortization |
6,725 | 5,352 | 4,140 | |||||||||
| Amortization of debt discount |
— | 1,129 | 553 | |||||||||
| Stock-based compensation expense |
17,316 | 10,685 | 2,159 | |||||||||
| Provision for doubtful accounts |
931 | 828 | 581 | |||||||||
| Impairment of long-lived assets |
— | 483 | — | |||||||||
| Deferred income taxes |
75 | 119 | 196 | |||||||||
| Foreign currency re-measurement loss |
58 | 153 | — | |||||||||
| Other non-cash expenses |
222 | 209 | — | |||||||||
| Changes in assets and liabilities: |
||||||||||||
| Accounts receivables |
(6,195) | (18,370) | (7,127) | |||||||||
| Prepaid expenses and other assets |
(3,523) | (1,787) | (2,165) | |||||||||
| Accounts payable |
1,619 | (2,302) | 567 | |||||||||
| Accrued expenses |
1,578 | 6,702 | 3,534 | |||||||||
| Deferred revenue |
38,748 | 44,868 | 25,200 | |||||||||
| Contingent consideration |
— | — | (560) | |||||||||
| Other liabilities |
558 | (119) | 2,193 | |||||||||
|
|
|
|
|
|
|
|||||||
| Net cash provided by (used in) operating activities |
9,112 | (1,907) | (3,356) | |||||||||
|
|
|
|
|
|
|
|||||||
| Cash flows from investing activities: |
||||||||||||
| Business acquisitions, net of cash acquired |
— | (38,811) | — | |||||||||
| Purchases of investments |
(38,976) | — | — | |||||||||
| Purchases of property and equipment |
(4,499) | (4,136) | (7,082) | |||||||||
|
|
|
|
|
|
|
|||||||
| Net cash used in investing activities |
(43,475) | (42,947) | (7,082) | |||||||||
|
|
|
|
|
|
|
|||||||
| Cash flows from financing activities: |
||||||||||||
| Proceeds from initial public offering and concurrent private placement, net of offering costs of $3,097 |
— | 112,275 | — | |||||||||
| Proceeds from issuance of Series D redeemable convertible preferred stock, net |
— | — | 30,818 | |||||||||
| Repayments of term loan and related termination fee |
— | (18,540) | — | |||||||||
| Deferred business acquisition payment |
(1,392) | — | — | |||||||||
| Payments of contingent consideration related to business acquisitions |
— | — | (856) | |||||||||
| Repurchase of common and preferred stock |
— | — | (3,526) | |||||||||
| Payments of capital lease obligations |
(68) | (253) | (256) | |||||||||
| Taxes paid related to net share settlement of equity awards |
(4,114) | — | — | |||||||||
| Excess tax benefit from stock-based compensation |
87 | — | — | |||||||||
| Proceeds from employee stock purchase plan |
3,724 | — | — | |||||||||
| Proceeds from stock option exercises |
2,924 | 1,304 | 489 | |||||||||
|
|
|
|
|
|
|
|||||||
| Net cash provided by financing activities |
1,161 | 94,786 | 26,669 | |||||||||
|
|
|
|
|
|
|
|||||||
| Effect of exchange rate changes on cash and cash equivalents |
(203) | (202) | (20) | |||||||||
|
|
|
|
|
|
|
|||||||
| Net (decrease) increase in cash and cash equivalents |
(33,405) | 49,730 | 16,211 | |||||||||
| Cash and cash equivalents, beginning of period |
86,553 | 36,823 | 20,612 | |||||||||
|
|
|
|
|
|
|
|||||||
| Cash and cash equivalents, end of period |
$ | 53,148 | $ | 86,553 | $ | 36,823 | ||||||
|
|
|
|
|
|
|
|||||||
| Supplemental cash flow information: |
||||||||||||
| Cash paid for income taxes |
$ | 556 | $ | 341 | $ | 61 | ||||||
| Cash paid for interest |
$ | 5 | $ | 1,427 | $ | 2,095 | ||||||
| Supplemental non-cash investing and financing information: |
||||||||||||
| Common stock issued for acquisitions |
$ | — | $ | 27,481 | $ | — | ||||||
| Vested stock options issued for acquisition |
$ | — | $ | 4,494 | $ | — | ||||||
See accompanying notes to consolidated financial statements.
80
Table of Contents
NOTES TO CONSOLIDATED FINANCIAL STATEMENTS
| (1) | Nature of the Business |
Rapid7, Inc. and subsidiaries (“we,” “us” or “our”) is a leading provider of analytics for security and IT operations that enable organizations to implement an active, analytics-driven approach to cyber security and IT operations.
| (2) | Summary of Significant Accounting Policies |
| (a) | Basis of Presentation and Consolidation |
The accompanying consolidated financial statements include our results of operations and those of our wholly-owned subsidiaries. All intercompany transactions and balances have been eliminated in consolidation. The accompanying consolidated financial statements have been prepared in accordance with accounting principles generally accepted in the United States of America (U.S. GAAP).
| (b) | Use of Estimates |
The preparation of financial statements in conformity with U.S. GAAP requires management to make estimates, judgments and assumptions that affect the reported amounts of assets, liabilities, revenue and expenses, together with amounts disclosed in the accompanying notes to the financial statements. Actual results could differ from those estimates. Significant items subject to such estimates and assumptions include revenue recognition, provision for doubtful accounts, stock-based compensation expense, deferred tax valuation allowances and goodwill and intangible assets. We base our estimates on historical experience and also on assumptions that we believe are reasonable. Changes in facts or circumstances may cause us to change our assumptions and estimates in future periods and it is possible that actual results could differ from our current or revised future estimates.
| (c) | Revenue Recognition |
We generate revenue primarily from selling products, maintenance and support, and professional services through a variety of delivery models. We generally bill customers and collect payment for both our products and services up front.
We generate products revenue from the sale of (1) perpetual or term software licenses for our Nexpose, Metasploit and AppSpider products, and associated content subscriptions for our Nexpose and Metasploit products, (2) managed services for our Nexpose, AppSpider and InsightIDR products and (3) cloud-based subscriptions for our InsightIDR, Logentries and AppSpider products. We also generate an immaterial amount of appliance revenue that is included in our products revenue and that is associated with hardware sold as part of our Nexpose product to certain customers. We generate maintenance and support revenue associated with customers’ purchases of our software licenses for Nexpose, Metasploit and AppSpider. We generate professional service revenue from the sale of our deployment and training services related to our solutions, incident response services and security advisory services.
Revenue is only recognized when all of the following criteria are met:
| • | Persuasive evidence of an arrangement exists. Binding agreements or purchase orders are generally evidence of an arrangement. |
| • | Delivery has occurred. Delivery occurs (1) upon delivery of the software license key or when the customer has access to the software product or (2) when we perform the services. |
| • | The sales price is fixed or determinable. Fees are considered fixed and determinable when the fees are contractually agreed upon with the customer. |
81
Table of Contents
| • | Collectability is probable. Collectability is deemed probable based on review of a number of factors, including creditworthiness and customer payment history. If collectability is not probable, revenue is deferred until collection becomes probable, which is generally upon the receipt of payment. |
Substantially all of our software licenses are sold in multiple-element arrangements that include maintenance and support and content subscriptions, and in addition could include cloud-based subscriptions, professional services and/or managed services. All of these elements are considered to be software elements other than cloud-based subscriptions, which are non-software elements, and managed services, which can be either software elements or non-software elements. Non-software elements included in multiple-element arrangements consist of a single deliverable that has stand-alone value and that represents a single unit of accounting. We have determined that we do not have vendor-specific objective evidence, or VSOE, of the selling price for the elements comprising these multiple-element arrangements as our software licenses are generally not sold on a stand-alone basis and we purposefully employ variable pricing for our offerings in order to meet customer purchase requirements along the multiple price points of the demand curve.
When all of the elements of a multiple-element arrangement are software elements, the revenue for software licenses and any other products and services that are sold along with the license is generally deferred on our balance sheet and recognized as revenue on our consolidated statements of operations ratably over the contractual period of the maintenance and support, typically one to three years, which is longer than the period over which the professional services are performed. Revenue recognition begins upon delivery of the software license, assuming that all other criteria for revenue recognition have been met.
When a multiple-element arrangement includes both software elements and non-software elements, the total arrangement consideration is first allocated between the software elements and the non-software elements based on the selling price hierarchy, which includes (1) VSOE, if available, (2) third-party evidence, or TPE, if VSOE is not available or (3) best estimate of selling price, or BESP, if neither VSOE nor TPE is available. We have not been able to establish a selling price for any element using VSOE or TPE. We determine BESP by considering our overall pricing objectives and market conditions. Significant pricing practices taken into consideration include our discounting practices, the size and volume of our transactions, our price lists, our go-to-market strategy, historical standalone sales and contract prices. Our multiple-element arrangements can include a single non-software element, in which case the portion of the consideration allocated to the non-software element is recognized ratably over the service period of the non-software element, assuming all other criteria for revenue recognition have been met. The portion of the consideration allocated to software elements is recognized as described above.
With respect to our managed services and cloud-based subscription offerings sold on a stand-alone basis, we recognize revenue ratably over the term of the managed service agreement or subscription, assuming that the other criteria for revenue recognition are met.
We recognize revenue from professional services sold on a stand-alone basis as those services are rendered.
For purposes of disclosing revenue by class, we allocate the arrangement consideration for multiple-element software arrangements among the individual elements utilizing BESP, as we do not have VSOE or TPE of selling price for any of the elements.
| (d) | Deferred Revenue |
Deferred revenue consists of amounts that have been invoiced but that have not been recognized as revenue. Deferred revenue that will be realized during the succeeding 12-month period is recorded as current, and the remaining deferred revenue is recorded as non-current.
82
Table of Contents
| (e) | Cash and Cash Equivalents |
We consider all highly liquid instruments with original maturities of three months or less at the date of purchase to be cash equivalents. Cash and cash equivalents are recorded at cost, which approximates fair value. As of December 31, 2016, $11.0 million of our cash equivalents were invested in money market funds and commercial paper.
| (f) | Investments |
We classify our investments as available-for-sale and record these investments at fair value. We currently invest primarily in commercial paper, corporate bonds, U.S. government agencies and asset-backed securities. Investments with an original maturity of greater than three months at the date of purchase and less than one year from the date of the balance sheet are classified as short-term and those with maturities of more than one year from the date of the balance sheet are classified as long-term in the consolidated balance sheet. Additionally, we do not invest in any securities with contractual maturities greater than 24 months. Unrealized gains and losses that are considered temporary are reported as a component of other comprehensive loss. Realized gains and losses are determined based on the specific identification method, and are reflected in our consolidated statements of operations. We regularly review our investment portfolio to identify and evaluate investments that have indicators of possible impairment. Factors considered in determining whether a loss is other-than-temporary include, but are not limited to: the length of time and extent a security’s fair value has been below its cost, the financial condition and near-term prospects of the investee, the credit quality of the security’s issuer, likelihood of recovery and our intent and ability to hold the security for a period of time sufficient to allow for any anticipated recovery in value. For our debt instruments, we also evaluate whether we have the intent to sell the security or it is more likely than not that we will be required to sell the security before recovery of its cost basis.
| (g) | Accounts Receivable and Allowance for Doubtful Accounts |
Accounts receivable are recorded at the invoiced amount, net of allowances for doubtful accounts. Management regularly reviews the adequacy of the allowance for doubtful accounts by considering the age of outstanding invoices, the customer’s expected ability to pay and the collection history, when applicable, to determine whether an allowance is appropriate. Accounts receivable are charged against the allowance for doubtful accounts after all means of collection have been exhausted and the potential for recovery is considered remote. Additions to the allowance for doubtful accounts are recorded in general and administrative expense in the consolidated statement of operations. We do not have any off balance sheet credit exposure related to our customers. The following table displays the changes in our allowance for doubtful accounts:
| Amount | ||||
| (in thousands) | ||||
| Balance at December 31, 2013 |
$ | 711 | ||
| Additions |
581 | |||
| Less write-offs, net of recoveries |
(1,016) | |||
|
|
|
|||
| Balance at December 31, 2014 |
276 | |||
| Additions |
828 | |||
| Less write-offs, net of recoveries |
(374) | |||
|
|
|
|||
| Balance at December 31, 2015 |
730 | |||
| Additions |
931 | |||
| Less write-offs, net of recoveries |
(600) | |||
|
|
|
|||
| Balance at December 31, 2016 |
$ | 1,061 | ||
|
|
|
|||
83
Table of Contents
| (h) | Concentration of Credit Risk |
Financial instruments that potentially expose us to concentrations of credit risk consist primarily of cash and cash equivalents, accounts receivable and short-term and long-term investments. We maintain a substantial portion of our cash and cash equivalents in money market funds invested in U.S. Treasury related obligations. Deposits held with banks may exceed the amount of insurance provided on such deposits. We have not experienced any losses in such accounts and believe that we are not exposed to any significant risk.
We provide credit to customers in the normal course of business. Collateral is not required for accounts receivable, but ongoing credit evaluations of customers’ financial condition are performed. We maintain reserves for potential credit losses. No single customer accounted for 10% or more of our total revenues in 2016, 2015 or 2014 or accounts receivable as of December 31, 2016 and 2015.
Our short-term and long-term investments primarily consist of commercial paper, corporate bonds, U.S. government agencies and asset-backed securities. All of our investments are highly-rated by credit rating agencies and are issued by organizations with reputable credit, and therefore bear minimal credit risk.
| (i) | Property and Equipment |
Property and equipment are recorded at cost and depreciated over their estimated useful lives using the straight-line method. Leasehold improvements are amortized over the shorter of the lease term or the estimated useful life of the related asset. All other asset categories are depreciated over three to five years. Upon sale, the cost of assets disposed and the related accumulated depreciation are removed from the accounts and any resulting gain or loss is recognized in the consolidated statements of operations. Repairs and maintenance costs are expensed as incurred.
| (j) | Capitalized Software Costs |
We capitalize certain costs related to software acquired for internal use and software developed for sale.
With respect to software acquired for internal use, we capitalize qualifying software costs, which include software license fees and third-party implementation and related costs. Total unamortized capitalized costs relating to software acquired for internal use as of December 31, 2016 and 2015 were $0.3 million and $0.6 million, respectively.
All costs capitalized relating to software developed for sale were fully amortized as of December 31, 2016 and 2015.
| (k) | Long-Lived Assets |
We review the carrying value of our long-lived assets for impairment whenever events or changes in circumstances indicate that the carrying value of these assets may not be recoverable. When such events or changes in circumstances occur, recoverability of these assets is measured by a comparison of the carrying value of an asset to the future net undiscounted cash flows directly associated with the asset. If assets are considered to be impaired, the impairment recognized is the amount by which the carrying value exceeds the fair value of the asset. We use a discounted cash flow approach or other methods, if appropriate, to assess fair value.
| (l) | Goodwill and Other Intangible Assets |
Goodwill is an asset representing the future economic benefits arising from other assets acquired in a business combination that are not individually identified and separately recognized. We allocate the cost of an acquired entity to the assets acquired and liabilities assumed based on their estimated fair values at the date of acquisition. The excess of the purchase price for acquisitions over the fair value of the net assets acquired, including other intangible assets, is recorded as goodwill. Goodwill is not
84
Table of Contents
amortized but is tested for impairment at least annually or more frequently when events or circumstances occur that indicate that it is more likely than not that an impairment has occurred.
For our goodwill impairment analysis, we operate with a single reporting unit. We test goodwill for impairment on the last day of each fiscal year and whenever events or changes in circumstances indicate that the carrying amount of this asset may exceed its fair value. To test goodwill impairment, we perform the two-step goodwill impairment test to identify potential goodwill impairment. The two step impairment test begins with an estimation of the fair value of a reporting unit. Goodwill impairment exists when a reporting unit’s carrying value of goodwill exceeds its implied fair value. Significant judgment is applied when goodwill is assessed for impairment. In performing the first step of the goodwill impairment testing and measurement process, we estimated the fair value of our single reporting unit using our market capitalization. Based upon our assessment performed as of December 31, 2016, we concluded the fair value of our single reporting unit exceeded its carrying value and there was no impairment of goodwill.
Other intangible assets acquired in a business combination are recognized at fair value using generally accepted valuation methods appropriate for the type of intangible asset and reported separately from goodwill. Intangible assets with definite lives are amortized over the estimated useful lives and are tested for impairment when events or circumstances occur that indicate that it is more likely than not that an impairment has occurred. For the year ended December 31, 2016, we determined there were no indicators of impairment of our other intangible assets.
| (m) | Translation of Foreign Currencies |
The functional currency of our foreign subsidiaries is the U.S. dollar. We translate all monetary assets and liabilities denominated in foreign currencies into U.S. dollars using the exchange rates in effect at the balance sheet dates and other assets and liabilities using historical exchange rates. Foreign currency denominated revenue and expenses have been re-measured using the average exchange rates in effect during each period. Foreign currency transactional and re-measurement gains and losses are included in other income (expense), net. In 2016, we recorded nominal foreign currency transactional losses and $0.1 million of foreign currency re-measurement losses. In 2015, we recorded foreign currency transactional losses and foreign currency re-measurement losses of $0.1 million and $0.2 million, respectively. Foreign currency transactional and re-measurement gains and losses were not significant in 2014.
| (n) | Stock-Based Compensation |
We measure and recognize compensation expense for all stock options, restricted stock awards (RSAs), restricted stock units (RSUs) and common stock issued pursuant to our employee stock purchase plan based on the estimated fair value of the award on the grant date. Stock-based compensation expense is recognized on a straight-line basis over the requisite service period, which is generally the same as the vesting period.
| (o) | Sales Commissions |
Sales commissions are recognized in the period that the commissions are earned by our employees, which is typically upon signing of an arrangement. Under our sales commission policy, the amount of sales commissions expense attributable to the sales arrangement signed in the period is recognized fully in that period; however, the revenue from the sales arrangement is generally recognized ratably over the contractual period of the applicable agreement.
| (p) | Advertising |
Advertising costs are expensed as incurred, and are recorded in sales and marketing expense in our consolidated statement of operations. We incurred $6.0 million, $4.3 million and $3.2 million in advertising expense in 2016, 2015 and 2014, respectively.
85
Table of Contents
| (q) | Income Taxes |
Income taxes are accounted for using the asset and liability method. Under this method, deferred tax assets and liabilities are recognized for differences between the financial statement carrying amounts of existing assets and liabilities and their respective income tax bases, and operating loss and tax credit carryforwards using tax rates expected to be in effect in the years in which the differences are expected to reverse. Deferred tax assets are reduced by a valuation allowance if it is more likely than not that all of, or a portion of, deferred tax assets will not be utilized in the future.
We account for unrecognized tax benefits using a more-likely-than-not threshold for financial statement recognition and measurement of tax positions taken or expected to be taken in a tax return. Interest and penalties associated with such uncertain tax positions are classified as a component of income tax expense.
| (r) | Net Loss per Share Attributable to Common Stockholders |
Basic net loss per share attributable to common stockholders is computed by dividing our net loss attributable to common stockholders by the weighted-average number of common shares used in the loss per share calculation during the period. Diluted net loss per share attributable to common stockholders is computed by giving effect to all potentially dilutive securities, including stock options, restricted stock awards, warrants and redeemable convertible preferred stock. Basic and diluted net loss per share attributable to common stockholders was the same for all periods presented as the inclusion of all potentially dilutive securities outstanding was anti-dilutive.
| (s) | Recent Accounting Pronouncements |
In October 2016, the Financial Accounting Standards Board (FASB) issued Accounting Standards Update (ASU) 2016-16, Income Taxes (Topic 740): Intra-Entity Transfers of Assets Other Than Inventory. The ASU is intended to improve the accounting for the income tax consequences of intra-entity transfers of assets other than inventory. Current GAAP prohibits the recognition of current and deferred income taxes for an intra-entity asset transfer until the asset has been sold to an outside party. The ASU will allow an entity to recognize the income tax consequences of these transfers when the transfers occur. The ASU will be effective for us in the first quarter of 2018. We are currently evaluating the impact that the adoption of this ASU will have on our consolidated financial statements.
In March 2016, the FASB issued ASU 2016-09, Compensation-Stock Compensation (Topic 718): Improvements to Employee Share-Based Payment Accounting. The ASU is intended to simplify several aspects of the accounting for share-based payment transactions, including the accounting for income taxes, forfeitures and statutory tax withholding requirements, as well as classification on the statement of cash flows. The ASU will be effective for us in the first quarter of 2017. We do not expect this ASU to have a material impact on our consolidated financial statements.
In February 2016, the FASB issued ASU 2016-02, Leases (Topic 842). The ASU requires companies to recognize on the balance sheet the assets and liabilities for the rights and obligations created by leased assets. The ASU will be effective for us in the first quarter of 2019, with early adoption permitted. We are currently evaluating the impact that the adoption of this ASU will have on our consolidated financial statements.
In November 2015, the FASB issued ASU 2015-17, Income Taxes (Topic 740): Balance Sheet Classification of Deferred Taxes. The ASU requires that deferred tax liabilities and assets be classified as noncurrent in a classified balance sheet simplifying current GAAP, which requires an entity to separate deferred tax liabilities and assets into current and noncurrent amounts in the balance sheet. The ASU may be applied prospectively or retrospectively at our election. We early adopted this ASU effective December 31, 2016. As a result, we have presented all deferred tax assets and liabilities as noncurrent on our consolidated balance sheet as of December 31, 2016, but have not
86
Table of Contents
reclassified current deferred tax assets and liabilities on our consolidated balance sheet as of December 31, 2015. Our consolidated financial statements were not materially impacted as a result of the adoption of this ASU.
In September 2015, the FASB issued ASU 2015-16, Business Combinations (Topic 805): Simplifying the Accounting for Measurement-Period Adjustments. The ASU eliminates the requirement for an acquirer in a business combination to account for measurement-period adjustments retrospectively. The new guidance requires that the cumulative impact of a measurement-period adjustment (including the impact on prior periods) be recognized in the reporting period in which the adjustment is identified. This ASU was adopted on January 1, 2016 and did not have a material impact on our consolidated financial statements.
In April 2015, the FASB issued ASU 2015-05, Intangibles – Goodwill and Other – Internal Use Software (Subtopic 350-40): Customer’s Accounting for Fees Paid in a Cloud Computing Arrangement, which provides guidance on accounting for fees paid in a cloud computing arrangement. Under the ASU, if a cloud computing arrangement includes a software license, which also grants the contractual rights and practical ability to take possession of the software, the software license element should be accounted for consistent with the purchase of other software licenses. If the cloud computing arrangement does not include a software license, as defined, it should be accounted for as a service contract. This ASU was adopted on January 1, 2016 and did not have a material impact on our consolidated financial statements.
In August 2014, the FASB issued ASU 2014-15, Presentation of Financial Statements – Going Concern (Subtopic 201-40): Disclosure of Uncertainties about an Entity’s Ability to Continue as a Going Concern. The ASU provides guidance on how and when reporting entities must disclose going-concern uncertainties in their financial statements. This ASU became effective for us on January 1, 2016. Our consolidated financial statements were not materially impacted as a result of the adoption of this ASU.
In May 2014, the FASB issued ASU 2014-09, Revenue from Contracts with Customers (Topic 606). The ASU outlines a single, comprehensive model for accounting for revenue from contracts with customers and requires more detailed disclosure to enable users of financial statements to understand the nature, amount, timing and uncertainty of revenue and cash flows arising from such contracts. In August 2015, the FASB issued ASU 2015-14, which provides a one year deferral in the effective date of ASU 2014-09. ASU 2014-09 will now be effective for us beginning January 1, 2018; however, early adoption will be permitted as of the original effective date.
We will adopt ASU 2014-09 in the first quarter of 2018 and expect to adopt on a modified retrospective basis. Under this method of adoption, we would recognize the cumulative effect of initially applying the standard as an adjustment to the opening balance of retained earnings in the period of initial application. Comparative prior year periods would not be adjusted. We are currently evaluating the potential impact of this standard on our financial position and results of operations. Based on the analysis performed to date, we expect revenue recognition related to our perpetual and term software licenses, managed services, cloud-based subscriptions and stand-alone professional services to remain substantially unchanged. However, under the new standard, for software licenses that are sold with professional services in a multiple-element arrangement, the professional services will likely represent a separate performance obligation and we will recognize revenue associated with the professional services as such services are performed. Revenue associated with professional services in a multiple-element arrangement is currently recognized ratably over the related contractual period of maintenance and support (typically one to three years) due to the lack of VSOE of selling price for the elements. Additionally, under the new standard, we expect to capitalize and amortize commissions relating to multiyear contracts rather than expensing them as incurred in the period that the commissions are earned by our employees (which is typically upon signing of an arrangement).
87
Table of Contents
| (3) | Business Combinations |
RevelOps, Inc.
On October 13, 2015, we acquired 100% of the outstanding equity of RevelOps, Inc. (d/b/a Logentries) for total consideration of $68.1 million. We made an initial payment of $36.2 million in cash, issued 1,252,627 shares of our common stock with an aggregate fair value of $27.4 million, inclusive of a discount from the quoted market price due to certain trading restrictions associated with the shares, and issued vested replacement options with respect to 221,759 shares of our common stock to certain continuing employees with an aggregate fair value of $4.5 million upon the closing of the acquisition. The fair value of the vested replacement options included in the purchase price was based on the fair value of the vested Logentries options on the acquisition date. The excess fair value when comparing the fair value of the new vested replacement options and the vested Logentries options of $0.3 million was expensed immediately in the post-combination financial statements of the combined entity.
The assets acquired and liabilities assumed were recorded at their estimated fair values as of the acquisition date. The excess of the purchase price over the assets acquired and liabilities assumed was recorded as goodwill. The fair value of goodwill, intangible assets and net tangible assets were $59.2 million, $9.4 million and $(0.5) million, respectively.
NT OBJECTives, Inc.
On April 30, 2015, we acquired 100% of the outstanding equity of NT OBJECTives, Inc. (NTO) for total consideration of $6.1 million. We made an initial cash payment of $3.4 million and issued 9,091 shares of our common stock with an aggregate fair value of $0.1 million upon the closing of the acquisition. We were also obligated to pay $0.1 million in cash for the settlement of a working capital adjustment and make two additional payments of $1.5 million each, less the amount of any indemnity claims. The net present value of these two additional payments, or $2.5 million, was included in the total purchase consideration paid. In December 2016, we paid the first of the two additional payments of $1.5 million, as well as the $0.1 million working capital adjustment.
The assets acquired and liabilities assumed were recorded at their estimated fair values as of the acquisition date. The excess of the purchase price over the assets acquired and liabilities assumed was recorded as goodwill. The fair value of goodwill, intangible assets and net tangible assets were $4.6 million, $2.1 million and $(0.6) million, respectively.
In May 2015, we entered into loan agreements with certain retained employees of NTO in the aggregate amount of $0.5 million. The terms of these agreements required the employees to pay us the total amount borrowed, with accrued interest at 1.7% per annum, within 18 months of the agreement date. The loan agreements were secured by restricted stock awards granted to the employees. The loans have been repaid in full.
| (4) | Fair Value Measurements and Investments |
We measure certain financial assets and liabilities at fair value. Fair value is determined based upon the exit price that would be received to sell an asset or paid to transfer a liability in an orderly transaction between market participants, as determined by either the principal market or the most advantageous market. Inputs used in the valuation techniques to derive fair values are classified based on a three-level hierarchy, as follows:
| • | Level 1: Observable inputs that reflect quoted prices (unadjusted) for identical assets or liabilities in active markets. |
| • | Level 2: Observable inputs other than Level 1 prices such as quoted prices for similar assets or liabilities; quoted prices in markets with insufficient volume or infrequent transactions (less active markets); or model-derived valuations in which all significant inputs are observable or can be derived principally from or corroborated by observable market data for substantially the full term of the assets or liabilities. |
88
Table of Contents
| • | Level 3: Unobservable inputs that are supported by little or no market activity and that are significant to the fair value of the asset or liability. |
We consider an active market to be one in which transactions for the asset or liability occur with sufficient frequency and volume to provide pricing information on an ongoing basis, and consider an inactive market to be one in which there are infrequent or few transactions for the asset or liability, the prices are not current, or price quotations vary substantially either over time or among market makers.
The following table presents our financial assets and liabilities measured and recorded at fair value on a recurring basis using the above input categories:
| As of December 31, 2016 | ||||||||||||||||
| Level 1 | Level 2 | Level 3 | Total | |||||||||||||
| (in thousands) | ||||||||||||||||
| Description: |
||||||||||||||||
| Assets: |
||||||||||||||||
| Money market funds |
$ | 10,085 | $ | — | $ | — | $ | 10,085 | ||||||||
| U.S. Government agencies |
14,982 | — | — | 14,982 | ||||||||||||
| Commercial paper |
— | 8,078 | — | 8,078 | ||||||||||||
| Corporate bonds |
— | 10,314 | — | 10,314 | ||||||||||||
| Asset-backed securities |
— | 6,467 | — | 6,467 | ||||||||||||
|
|
|
|
|
|
|
|
|
|||||||||
| Total assets |
$ | 25,067 | $ | 24,859 | $ | — | $ | 49,926 | ||||||||
|
|
|
|
|
|
|
|
|
|||||||||
We had no liabilities measured and recorded at fair value on a recurring basis as of December 31, 2016. We had no assets or liabilities measured and recorded at fair value on a recurring basis as of December 31, 2015.
Our investments, which are all classified as available-for-sale, consisted of the following:
| As of December 31, 2016 | ||||||||||||||||
| Amortized Cost |
Gross Unrealized Gains |
Gross Unrealized Losses |
Fair Value | |||||||||||||
| (in thousands) | ||||||||||||||||
| Description: |
||||||||||||||||
| U.S. Government agencies |
$ | 14,992 | $ | 3 | $ | (13) | $ | 14,982 | ||||||||
| Commercial paper |
7,178 | — | — | 7,178 | ||||||||||||
| Corporate bonds |
10,326 | 1 | (13) | 10,314 | ||||||||||||
| Asset-backed securities |
6,464 | 4 | (1) | 6,467 | ||||||||||||
|
|
|
|
|
|
|
|
|
|||||||||
| Total |
$ | 38,960 | $ | 8 | $ | (27) | $ | 38,941 | ||||||||
|
|
|
|
|
|
|
|
|
|||||||||
For all of our investments for which the amortized cost basis was greater than the fair value at December 31, 2016, we have concluded that there is no plan to sell the security nor is it more likely than not that we would be required to sell the security before its anticipated recovery. In making the determination as to whether the unrealized loss is other-than-temporary, we considered the length of time and extent the investment has been in an unrealized loss position, the financial condition and near-term prospects of the issuers, the issuers’ credit rating and the time to maturity.
89
Table of Contents
| (5) | Property and Equipment |
Property and equipment are recorded at cost and consist of the following:
| As of December 31, | ||||||||
| 2016 | 2015 | |||||||
| (in thousands) | ||||||||
| Computer equipment and software |
$ | 12,844 | $ | 9,858 | ||||
| Furniture and fixtures |
3,131 | 2,409 | ||||||
| Leasehold improvements |
8,077 | 6,943 | ||||||
|
|
|
|
|
|||||
| Total |
24,052 | 19,210 | ||||||
| Less accumulated depreciation |
(15,964) | (11,678) | ||||||
|
|
|
|
|
|||||
| Property and equipment, net |
$ | 8,088 | $ | 7,532 | ||||
|
|
|
|
|
|||||
We recorded depreciation expense of $4.3 million, $4.1 million and $3.3 million in 2016, 2015 and 2014, respectively.
| (6) | Goodwill and Intangible Assets |
Goodwill was $75.1 million and $74.6 million as of December 31, 2016 and 2015, respectively. There were no goodwill impairment charges in 2016, 2015 or 2014. The following table displays the changes in the gross carrying amount of goodwill:
| Amount | ||||
| (in thousands) | ||||
| Balance at December 31, 2014 |
$ | 11,265 | ||
| NTO acquisition accounting adjustments |
4,590 | |||
| Logentries acquisition accounting adjustments |
58,710 | |||
|
|
|
|||
| Balance at December 31, 2015 |
$ | 74,565 | ||
| Logentries acquisition accounting adjustments |
545 | |||
|
|
|
|||
| Balance at December 31, 2016 |
$ | 75,110 | ||
|
|
|
|||
Identifiable intangible assets consist of the following:
| As of December 31, 2016 | As of December 31, 2015 | |||||||||||||||||||||||||||
| Weighted- Average Life (years) |
Gross Carrying Amount |
Accumulated Amortization |
Net Book Value | Gross Carrying Amount |
Accumulated Amortization |
Net Book Value | ||||||||||||||||||||||
| (in thousands) | ||||||||||||||||||||||||||||
| Intangible assets subject to amortization: |
||||||||||||||||||||||||||||
| Developed technology |
6.3 | $ | 11,231 | $ | (3,118) | $ | 8,113 | $ | 12,851 | $ | (2,955) | $ | 9,896 | |||||||||||||||
| Customer relationships |
6.7 | 1,000 | (197) | 803 | 1,000 | (43) | 957 | |||||||||||||||||||||
| Trade names |
6.1 | 519 | (496) | 23 | 719 | (389) | 330 | |||||||||||||||||||||
| Non-compete agreements |
2.0 | 40 | (33) | 7 | 540 | (338) | 202 | |||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Total intangible assets |
$ | 12,790 | $ | (3,844) | $ | 8,946 | $ | 15,110 | $ | (3,725) | $ | 11,385 | ||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
Intangible assets are expensed on a straight-line basis over the useful life of the asset. We recorded amortization expense of $2.4 million, $1.3 million and $0.9 million in 2016, 2015 and 2014, respectively.
During the third quarter of 2016, we discontinued our Mobilisafe product offering and accelerated the amortization of the remaining $0.2 million net book value. In addition, we wrote-off the $2.3 million gross carrying amount and related accumulated amortization.
90
Table of Contents
Estimated future amortization expense of the acquired identifiable intangible assets as of December 31, 2016 is as follows (in thousands):
| 2017 |
$ | 1,930 | ||
| 2018 |
1,886 | |||
| 2019 |
1,859 | |||
| 2020 |
1,837 | |||
| 2021 |
1,332 | |||
| 2022 and thereafter |
102 | |||
|
|
|
|||
| Total |
$ | 8,946 | ||
|
|
|
| (7) | Long-term Debt and Line of Credit |
| (a) | Term Loan |
On December 27, 2013, we entered into a Subordinated Loan and Security Agreement (term loan agreement) with a financial institution, whereby we borrowed $18.0 million. Interest was paid monthly at a rate of 12% per annum, commencing in January 2014. Pursuant to the term loan agreement, we pledged certain assets as collateral, including intellectual property and accounts receivable.
Additionally, warrants to purchase up to 200,000 shares of our common stock were issued to the financial institution in connection with the term loan agreement. These warrants have a contractual life of 10 years and were issued with an exercise price of $10.00 per share of common stock underlying such warrants. The warrants are classified as permanent equity. Accordingly, we recorded the term loan net of an original issuance discount of $1.0 million, representing the calculated relative fair value of the warrants, which was amortized over the four-year term of the loan using the effective interest method.
On July 23, 2015, we repaid in full and terminated the term loan. The aggregate amount paid was $18.7 million, which included the full principal amount of $18.0 million, a termination payment of $0.5 million and $0.2 million of accrued interest. Upon the repayment and termination of the term loan, we recorded a $0.8 million charge to interest expense for the unamortized portion of the debt discount.
| (b) | Line of Credit |
On April 22, 2013, we entered into a Loan and Security Agreement for a line of credit (line of credit agreement) with a financial institution, which was subsequently modified on December 27, 2013. Under the line of credit agreement, we were able to borrow up to the lesser of $10.0 million or 80% of eligible accounts receivable. The line of credit carried a floating interest rate equal to the prime rate plus 1.25%. On August 5, 2015, we terminated the line of credit agreement, under which there was no outstanding balance.
| (8) | Stockholders’ Equity (Deficit) |
| (a) | Redeemable Convertible Preferred Stock |
Upon the closing of the IPO in 2015, all of our outstanding preferred stock automatically converted into 18,322,605 shares of common stock, which included 1,939,990 additional shares of common stock issued upon conversion of our Series D preferred stock (IPO Participation Payment). As a result of the IPO Participation Payment, we recorded a $14.2 million beneficial conversion charge during the year ended December 31, 2015. The amount of the beneficial conversion charge was calculated by multiplying the total number of shares of common stock issued upon the conversion of our Series D preferred stock, including the additional shares of common stock issued in connection
91
Table of Contents
with the IPO Participation Payment, by the difference between the fair market value of our common stock at the time of the original issuance of the Series D preferred stock and the effective conversion price of the Series D preferred stock, which is calculated as the aggregate proceeds from the sale of Series D preferred stock, divided by the total number of shares of common stock issued upon conversion of our Series D preferred stock, including the additional shares of common stock issued in connection with the IPO Participation Payment..
No redeemable convertible preferred stock was outstanding as of December 31, 2016 or 2015.
| (b) | Common Stock |
On October 13, 2015, we issued 1,252,627 shares of our common stock in connection with our acquisition of Logentries.
On July 22, 2015, we closed our IPO of 7,417,500 shares of common stock at an offering price of $16.00 per share, including 967,500 shares pursuant to the underwriters’ option to purchase additional shares, resulting in net proceeds of $107.3 million, after deducting underwriting discounts and commissions of $8.3 million and offering expenses of $3.1 million.
On July 22, 2015, concurrently with the closing of our IPO, we issued and sold to entities affiliated with Technology Crossover Ventures 312,500 shares of our common stock in a private placement at a price equal to the IPO price of $16.00 per share, resulting in net proceeds to us of $5.0 million.
Additionally, in connection with the closing of our IPO, we filed an amended and restated certificate of incorporation to, among other things (i) increase the total number of shares of our common stock that we are authorized to issue to 100,000,000 and (ii) eliminate all references to the various series of preferred stock that were previously authorized (including certain protective measures held by the various series of preferred stock), except for the reference to 10,000,000 shares of undesignated preferred stock that may be issued, and with terms to be set, by our board of directors.
On April 30, 2015, we issued 9,091 shares of our common stock in connection with our acquisition of NTO.
| (c) | Treasury Stock |
In 2016, we repurchased 62,428 shares of common stock for an aggregate amount of $0.9 million to settle employee withholding taxes upon the vesting of restricted stock awards. In 2014, we repurchased 401,626 shares of common stock from certain employees and non-employees, for an aggregate amount of $3.5 million.
| (d) | Common Stock Warrants |
In December 2013, we issued warrants to purchase 200,000 shares of common stock to a financial institution in connection with the term loan agreement. In each of the years 2016 and 2015, warrants with respect to 100,000 shares of common stock were exercised, with net shares issued of 28,774 and 53,535, respectively. As of December 31, 2016, no warrants remained unexercised.
| (9) | Stock-Based Compensation |
| (a) | General |
In connection with our IPO, our board of directors resolved not to make future grants under our 2011 Stock Option and Grant Plan (the 2011 Plan). The 2011 Plan will continue to govern outstanding awards granted thereunder. The 2011 Plan provided for the grant of qualified incentive stock options and nonqualified stock options or other awards such as RSAs to our employees, officers, directors and outside consultants.
In July 2015, our board of directors adopted and our stockholders approved our 2015 Equity Incentive Plan (the 2015 Plan). We initially reserved 800,000 shares of our common stock for the
92
Table of Contents
issuance of awards under the 2015 Plan plus the number of shares of common stock reserved for issuance under the 2011 Plan at the time the 2015 Plan became effective. The 2015 Plan also provides that (i) any shares subject to awards granted under the 2011 Plan that would have otherwise returned to the 2011 Plan (such as upon the expiration or termination of a stock award prior to vesting) will be added to, and available for issuance under, the 2015 Plan and (ii) the number of shares reserved and available for issuance under the 2015 Plan automatically increases each January 1, beginning on January 1, 2016, by 4% of the outstanding number of shares of our common stock on the immediately preceding December 31 (known as the “evergreen” provision) or such lesser number of shares as determined by our board of directors. Additionally, on October 8, 2015, our board of directors amended, effective as of the acquisition of Logentries, the 2015 Plan to reserve an additional 1,500,000 shares of our common stock for issuance of inducement awards.
In March 2016, we increased the number of shares authorized to be issued under the 2015 Plan by 1,661,616 shares, which represents the amount automatically added pursuant to the evergreen provision contained therein. As of December 31, 2016, shares of common stock authorized to be issued under the 2015 Plan totaled 8,423,745 and there were 1,792,488 shares of common stock available for grant.
We recognize stock-based compensation expense for all awards on a straight-line basis over the applicable vesting period, which is generally four years.
Stock-based compensation expense for restricted stock, restricted stock units, stock options and issuances of common stock pursuant to our employee stock purchase plan was classified in the accompanying consolidated statements of operations as follows:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| Stock-based compensation expense: |
||||||||||||
| Cost of revenue |
$ | 610 | $ | 532 | $ | 167 | ||||||
| Research and development |
6,054 | 5,010 | 499 | |||||||||
| Sales and marketing |
6,607 | 3,139 | 496 | |||||||||
| General and administrative |
4,045 | 2,004 | 997 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total stock-based compensation expense |
$ | 17,316 | $ | 10,685 | $ | 2,159 | ||||||
|
|
|
|
|
|
|
|||||||
93
Table of Contents
| (b) | Restricted Stock and Restricted Stock Units |
Restricted stock and restricted stock unit activity during 2016, 2015 and 2014 was as follows:
| Restricted Stock | Restricted Stock Units | |||||||||||||||
| Shares | Weighted- Average Grant Date Fair Value |
Shares | Weighted- Average Grant Date Fair Value |
|||||||||||||
| Unvested balance as of December 31, 2013 |
68,781 | $ 1.35 | — | $ | — | |||||||||||
| Granted |
— | — | — | — | ||||||||||||
| Vested |
(64,596) | 1.35 | — | — | ||||||||||||
|
|
|
|
|
|||||||||||||
| Unvested balance as of December 31, 2014 |
4,185 | 1.35 | — | — | ||||||||||||
| Granted |
1,358,505 | 19.29 | — | — | ||||||||||||
| Vested |
(204,732) | 18.48 | — | — | ||||||||||||
| Forfeited |
(8,701) | 23.01 | — | — | ||||||||||||
|
|
|
|
|
|||||||||||||
| Unvested balance as of December 31, 2015 |
1,149,257 | 19.34 | — | — | ||||||||||||
| Granted |
— | — | 919,397 | 13.37 | ||||||||||||
| Vested |
(538,896) | 20.67 | (91,020) | 12.93 | ||||||||||||
| Forfeited |
(25,357) | 20.96 | (93,800) | 12.97 | ||||||||||||
|
|
|
|
|
|||||||||||||
| Unvested balance as of December 31, 2016 |
585,004 | $ | 18.05 | 734,577 | $ | 13.47 | ||||||||||
|
|
|
|
|
|||||||||||||
As of December 31, 2016, the unrecognized compensation cost related to shares of unvested restricted stock and restricted stock units expected to vest was $14.7 million. This unrecognized compensation will be recognized over an estimated weighted-average amortization period of 2.5 years.
94
Table of Contents
| (c) | Stock Options |
The following table summarizes information about stock option activity during the reporting periods:
| Shares | Weighted Average Exercise Price |
Weighted Average Remaining Contractual Life (in years) |
Aggregate Intrinsic Value (in thousands) |
|||||||||||||
| Outstanding as of December 31, 2013 |
3,202,335 | $ 3.77 | ||||||||||||||
| Granted |
791,865 | 7.74 | ||||||||||||||
| Exercised |
(201,200) | 2.41 | $ | 1,069 | ||||||||||||
| Forfeited/cancelled |
(231,696) | 5.45 | ||||||||||||||
|
|
|
|||||||||||||||
| Outstanding as of December 31, 2014 |
3,561,304 | 4.62 | ||||||||||||||
| Granted |
1,035,459 | 11.13 | ||||||||||||||
| Options assumed from acquisition |
221,759 | 1.65 | ||||||||||||||
| Exercised |
(385,238) | 3.50 | $ | 3,472 | ||||||||||||
| Forfeited/cancelled |
(186,669) | 8.33 | ||||||||||||||
|
|
|
|||||||||||||||
| Outstanding as of December 31, 2015 |
4,246,525 | 5.99 | ||||||||||||||
| Granted |
1,454,626 | 13.43 | ||||||||||||||
| Exercised |
(650,185) | 4.43 | $ | 6,409 | ||||||||||||
| Forfeited/cancelled |
(470,591) | 9.65 | ||||||||||||||
|
|
|
|||||||||||||||
| Outstanding as of December 31, 2016 |
4,580,375 | $ 8.20 | 7.2 | $ | 20,626 | |||||||||||
|
|
|
|||||||||||||||
| Vested and exercisable as of December 31, 2016 |
2,854,734 | $ 5.60 | 6.3 | $ | 19,131 | |||||||||||
| Vested and expected to vest as of December 31, 2016 |
4,250,315 | $ 7.83 | 7.1 | $ | 20,454 | |||||||||||
As of December 31, 2016, the unrecognized compensation cost related to 1,395,581 unvested stock options expected to vest was $7.3 million. This unrecognized compensation will be recognized over an estimated weighted-average amortization period of 2.7 years.
The total fair value of stock options vested in 2016, 2015 and 2014 was $3.4 million, $3.4 million and $2.4 million, respectively. The weighted-average grant date fair value per share of stock options granted in 2016, 2015 and 2014 was $6.38, $5.01 and $4.09 per share, respectively.
| (d) | Determining the Fair Value of Options |
We use the Black-Scholes option pricing model to estimate the fair value of stock option awards. The Black-Scholes option pricing model requires management to make a number of other assumptions, including the expected life of the option, the volatility of the underlying stock, the risk-free interest rate and expected dividends. The assumptions used in our Black-Scholes option-pricing model represent management’s best estimates at the time of grant. These estimates are complex, involve a number of variables, uncertainties and assumptions and the application of management’s judgment, as they are inherently subjective. If any assumptions change, our stock-based compensation expense could be materially different in the future.
Expected Term
The expected term represents the period that our stock options are expected to be outstanding. We calculated the expected term using the simplified method based on the average of each option’s vesting term and the contractual period during which the option can be exercised, which is typically 10 years following the date of grant.
95
Table of Contents
Expected Volatility
We determine the price volatility factor based on the historical volatilities of our publicly traded peer group as we do not have a significant trading history for our common stock. Industry peers consist of several public companies in the technology industry that are similar to us in size, stage of life cycle, and financial leverage. We used the same set of peer group companies in all the relevant valuation estimates. We intend to continue to consistently apply this process using the same or similar public companies until a sufficient amount of historical information regarding the volatility of our own common stock share price becomes available, or unless circumstances change such that the identified companies are no longer similar to us, in which case, more suitable companies whose share prices are publicly available would be utilized in the calculation.
Risk-Free Interest Rate
The risk-free interest rate was based on U.S. Treasury zero-coupon securities with maturities consistent with the estimated expected term.
Expected Dividend Yield
We have not paid dividends on our common stock nor do we expect to pay dividends in the foreseeable future.
The following table reflects the range of assumptions for options granted during 2016, 2015 and 2014:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Expected term (in years) |
5.5 – 6.3 | 6.3 | 6.3 | |||||||||
| Expected volatility |
48 – 50% | 42 – 48% | 47 – 49% | |||||||||
| Risk-free interest rate |
1.2 – 1.9% | 1.5 – 1.8% | 1.5 – 1.7% | |||||||||
| Expected dividend yield |
— | — | — | |||||||||
| Grant date fair value per share |
$ | 5.53 – 8.35 | $ | 4.39 – 10.09 | $ | 3.74 – 4.88 | ||||||
| (e) | Employee Stock Purchase Plan |
On July 17, 2015, we filed a registration statement on Form S-8 with the Securities and Exchange Commission registering 800,000 shares of our common stock reserved under our 2015 Employee Stock Purchase Plan (ESPP). Under the ESPP, employees may set aside after-tax withholdings to purchase our common shares at a discounted price. In March 2016, we increased the number of shares to be authorized under the ESPP by 415,404 shares, which represents the amount automatically added pursuant to the evergreen provision of the ESPP. As of December 31, 2016, shares of common stock authorized to be issued under the ESPP totaled 1,215,404 and there were 869,126 shares of common stock available for grant.
Under the ESPP, employees may set aside up to 15% of their gross earnings, on an after-tax basis, to purchase our common shares at a discounted price, which is calculated at 85% of the lesser of: (i) the market value of our common stock at the beginning of each offering period and (ii) the market value of our common stock on the applicable purchase date.
The following table reflects the assumptions used in the Black Scholes option pricing model to calculate the expense related to the ESPP:
| Year Ended December 31, | ||||||||
| 2016 | 2015 | |||||||
| Expected term (in years) |
0.5 – 1.0 | 0.5 – 1.2 | ||||||
| Expected volatility |
42 – 49% | 37 – 41% | ||||||
| Risk-free interest rate |
0.5 – 0.7% | 0.1 – 0.3% | ||||||
| Expected dividend yield |
— | — | ||||||
| Grant date fair value per share |
$ | 3.58 – 5.49 | $ | 4.33 – 7.91 | ||||
96
Table of Contents
On March 15, 2016, we issued 192,676 shares of common stock to employees for aggregate proceeds of $2.1 million. The purchase price of the shares of common stock was $10.88 per share, which was discounted in accordance with the terms of the ESPP from the closing price of our common stock on March 15, 2016 of $12.80.
On September 15, 2016, we issued 153,602 shares of common stock to employees for aggregate proceeds of $1.6 million. The purchase price of the shares of common stock was $10.60 per share, which was discounted in accordance with the terms of the ESPP from the closing price of our common stock on March 16, 2016 of $12.47.
| (10) | Income Taxes |
Loss before income taxes included in the consolidated statements of operations was as follows:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| United States. |
$ | (41,466) | $ | (43,020) | $ | (32,937) | ||||||
| Foreign |
(7,561) | (6,341) | 689 | |||||||||
|
|
|
|
|
|
|
|||||||
| Loss before income taxes |
$ | (49,027) | $ | (49,361) | $ | (32,248) | ||||||
|
|
|
|
|
|
|
|||||||
Income tax (benefit) expense included in the consolidated statements of operations was as follows:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| Current: |
||||||||||||
| Federal |
$ | 493 | $ | — | $ | — | ||||||
| State and local |
61 | 116 | 22 | |||||||||
| Foreign |
(656) | 261 | 161 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total current (benefit) expense |
(102) | 377 | 183 | |||||||||
|
|
|
|
|
|
|
|||||||
| Deferred: |
||||||||||||
| Federal |
98 | 98 | 180 | |||||||||
| State and local |
13 | 11 | 14 | |||||||||
| Foreign |
(36) | 10 | 2 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total deferred expense |
75 | 119 | 196 | |||||||||
|
|
|
|
|
|
|
|||||||
| Income tax (benefit) expense |
$ | (27) | $ | 496 | $ | 379 | ||||||
|
|
|
|
|
|
|
|||||||
The table below reconciles the differences between income taxes computed at the federal statutory rate of 34% and our provision for income taxes:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Expected income tax |
34.0% | 34.0% | 34.0% | |||||||||
| State taxes, net of federal benefit |
(0.1) | (0.1) | (0.1) | |||||||||
| Permanent differences |
(1.4) | (3.0) | (0.5) | |||||||||
| Federal research and development credit |
2.4 | 0.6 | 0.8 | |||||||||
| Foreign rate differential |
(3.0) | (3.3) | 0.2 | |||||||||
| Change in valuation allowance |
(31.9) | (29.9) | (35.6) | |||||||||
| Other |
0.1 | 0.7 | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Total income tax benefit (expense) |
0.1% | (1.0)% | (1.2)% | |||||||||
|
|
|
|
|
|
|
|||||||
97
Table of Contents
Net deferred tax assets and liabilities, as set forth in the table below, reflect the impact of temporary differences between the amounts of assets and liabilities recorded for financial statement purposes and such amounts measured in accordance with tax laws:
| As of December 31, | ||||||||
| 2016 | 2015 | |||||||
| (in thousands) | ||||||||
| Deferred tax assets: |
||||||||
| Accruals and reserves |
$ | 458 | $ | 300 | ||||
| Net operating loss carryforwards |
35,492 | 37,744 | ||||||
| Deferred revenue |
16,471 | 9,971 | ||||||
| Amortization |
3,356 | 3,318 | ||||||
| Research and development credits |
1,775 | 1,269 | ||||||
| Stock-based compensation |
4,999 | 2,436 | ||||||
| Other |
3,959 | 3,312 | ||||||
|
|
|
|
|
|||||
| Total deferred tax assets |
66,510 | 58,350 | ||||||
|
|
|
|
|
|||||
| Deferred tax liabilities: |
||||||||
| Intangible assets |
(534) | (417) | ||||||
| Depreciation |
(102) | (51) | ||||||
|
|
|
|
|
|||||
| Total deferred tax liabilities |
(636) | (468) | ||||||
|
|
|
|
|
|||||
| Less: Valuation allowance |
(66,395) | (58,328) | ||||||
|
|
|
|
|
|||||
| Net deferred tax liabilities |
$ | (521) | $ | (446) | ||||
|
|
|
|
|
|||||
In connection with the global structuring of our intellectual property and international business operations in the fourth quarter of 2016, we transferred certain intellectual property rights to our wholly owned subsidiary in the United Kingdom. Although the transfer of intellectual property rights between consolidated entities did not result in any gain in the consolidated results of operations, we generated a taxable gain in the U.S. that was substantially offset by our existing net operating loss carryforwards. However, we recorded $0.2 million of current U.S. federal income taxes related to Alternative Minimum Tax (AMT). This amount is offset by a current foreign income tax benefit due to refundable tax credits that arose after we completed our research and development studies in Canada, Ireland and the UK.
We recorded a deferred tax provision of $0.1 million for 2016, 2015 and 2014 relating to tax amortization of goodwill with a corresponding increase to the deferred tax liability. As of December 31, 2016, we have evaluated the need for a valuation allowance on deferred tax assets. In assessing whether the deferred tax assets are realized, management considered whether it is more likely than not that some portion or all of the deferred tax assets will not be realized. Due to our history of generating losses in the U.S. and Ireland, we continue to record a full valuation allowance against our U.S. and Ireland deferred tax assets. As of December 31, 2016, we expect to generate losses in the United Kingdom for the foreseeable future. Therefore, in addition to the U.S. and Ireland, a full valuation allowance has been recorded against all deferred tax assets in the United Kingdom. If we achieve future profitability, a significant portion of these deferred tax assets could be available to offset future income taxes.
The valuation allowance increased by $8.1 million for the year ended December 31, 2016, due primarily to additional operating losses generated during the year.
We have not provided for U.S. income taxes on the undistributed earnings of our non-U.S. subsidiaries, as we plan to permanently reinvest these amounts.
As of December 31, 2016, we had federal and state net operating loss carryforwards of $93.8 million and $69.2 million, respectively. The federal and state net operating loss carryforward expire at various dates beginning in 2023. As of December 31, 2016, we had foreign net operating loss carryforwards of
98
Table of Contents
$25.6 million that can be carried forward indefinitely. Of these amounts, $8.8 million relate to stock-based compensation tax deductions greater than compensation recognized for financial reporting purposes (APIC NOLs). As a result, the APIC NOLs are included in the net operating loss carryforwards, however, are not reflected in deferred tax assets as of December 31, 2016 and 2015. The APIC NOLs will be credited to additional paid-in capital if and when such deductions reduce taxes payable as determined based on a “with-and-without” approach.
We also had federal and state research and development credit carryforwards of $1.4 million and $0.5 million as of December 31, 2016, respectively. These credit carryforwards expire at various dates beginning in 2023.
We believe that a change of ownership within the meaning of Section 382 and 383 of the Internal Revenue Code of 1986, as amended, occurred in 2011. Under Section 382 and 383 of the Internal Revenue Code of 1986, as amended, if a corporation undergoes an “ownership change,” generally defined as a greater than 50% change (by value) in its equity ownership over a three-year period, the corporation’s ability to use its pre-change net operating loss carryforwards, or NOLs, and other pre-change tax attributes, such as research and development credits, to offset its post-change income may be limited. As a result, our U.S. federal net operating loss and research and development credit utilization will be limited to an amount equal to the market capitalization at the time of the ownership change multiplied by the federal long-term tax exempt rate. We do not believe that any of our net operating losses or research and development credits will expire as a result of this limitation.
We file income tax returns in all jurisdictions in which we operate. We have established reserves to provide for additional income taxes that management believes will more likely or not be due in future years. The reserves have been established based upon our assessment as to the potential exposure. Changes in our reserves for unrecognized income tax benefits are as follows:
| Amount | ||||
| (in thousands) | ||||
| Balance at December 31, 2014 |
$ | 35 | ||
| Additions based on current year tax positions |
106 | |||
|
|
|
|||
| Balance at December 31, 2015 |
141 | |||
| Additions based on prior year tax positions |
247 | |||
|
|
|
|||
| Balance at December 31, 2016 |
$ | 388 | ||
|
|
|
|||
In the normal course of business, we are subject to examination by federal, state, and foreign jurisdictions, where applicable. The statute of limitations for these jurisdictions is generally three to six years. However, to the extent we utilize net operating losses or other similar carryforward attributes such as credits, the statute remains open to the extent of the net operating losses or credits that are utilized. We have no tax returns under examination as of December 31, 2016. We record interest and penalties on any income tax liability as income tax expense. We recorded $0.1 million of interest and penalties in 2016, and recorded nominal interest and penalties in 2015. We believe it is reasonably possible that our gross unrecognized tax benefits could decrease (whether by payment, release or a combination of both) in the next 12 months by up to $0.3 million.
99
Table of Contents
| (11) | Net Loss Per Share |
The following table summarizes the computation of basic and diluted net loss per share of our common stock for 2016, 2015 and 2014:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands, except share and per share data) | ||||||||||||
| Numerator: |
||||||||||||
| Net loss |
$ | (49,000) | $ | (49,857) | $ | (32,627) | ||||||
| Accretion of preferred stock to redemption value |
— | (35,061) | (52,336) | |||||||||
| Beneficial conversion charge relating to IPO participation payment |
— | (14,161) | — | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss attributable to common stockholders, basic and diluted |
$ | (49,000) | $ | (99,079) | $ | (84,963) | ||||||
|
|
|
|
|
|
|
|||||||
| Denominator: |
||||||||||||
| Weighted-average common shares outstanding, basic and diluted |
41,248,473 | 24,740,480 | 12,770,916 | |||||||||
|
|
|
|
|
|
|
|||||||
| Net loss per share attributable to common stockholders, basic and diluted |
$ | (1.19) | $ | (4.00) | $ | (6.65) | ||||||
|
|
|
|
|
|
|
|||||||
The following potentially dilutive securities outstanding, prior to the use of the treasury stock method or if-converted method, have been excluded from the computation of diluted weighted-average shares outstanding for the respective periods below because they would have been anti-dilutive:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| Options to purchase common stock |
4,580,375 | 4,246,525 | 3,561,304 | |||||||||
| Unvested restricted stock |
585,004 | 1,149,257 | 4,185 | |||||||||
| Unvested restricted stock units |
734,577 | — | — | |||||||||
| Warrants to purchase common stock |
— | 100,000 | 200,000 | |||||||||
| Shares to be issued under ESPP |
91,815 | 114,271 | — | |||||||||
| Redeemable convertible preferred stock |
— | — | 16,382,615 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total |
5,991,771 | 5,610,053 | 20,148,104 | |||||||||
|
|
|
|
|
|
|
|||||||
In 2014, we have excluded shares of common stock issuable in connection with the IPO Participation Payment from the table above and the calculation of diluted net loss per share. The number of shares of common stock to be issued in connection with the IPO Participation Payment was dependent on the offering price of common stock of at least $14.55 per share and aggregate gross proceeds of at least $60.0 million (Qualified Public Offering) and therefore was not determinable until the occurrence of such Qualified Public Offering. See Note 8 to the consolidated financial statements.
| (12) | Commitments and Contingencies |
| (a) | Leases |
We have operating lease commitments for our facilities that expire at various dates through 2020. For operating leases that contain rent escalation or rent concession provisions, we record the total rent expense on a straight-line basis over the term of the lease. We record the difference between the rent paid and the straight-line rent as a deferred rent liability on the accompanying consolidated balance sheets.
100
Table of Contents
Rent expense was $5.0 million, $4.0 million and $3.5 million for 2016, 2015 and 2014, respectively.
We have also leased certain equipment and furniture under non-cancelable capital lease agreements, which are included in other current liabilities in the accompanying consolidated balance sheets. As of December 31, 2015, we had one capital lease for equipment. Capital leases are capitalized using interest rates considered appropriate at the inception of each lease. We had $0.3 million of capital lease obligations as of December 31, 2015. We had no capital lease obligations as of December 31, 2016.
The approximate future minimum payments under non-cancelable operating leases as of December 31, 2016 are as follows:
| 2017 |
$ | 6,282 | ||
| 2018 |
5,431 | |||
| 2019 |
4,152 | |||
| 2020 |
1,452 | |||
| 2021 |
566 | |||
|
|
|
|||
| Total |
$ | 17,883 | ||
|
|
|
| (b) | Purchase Obligations |
As of December 31, 2016, we have non-cancellable firm purchase commitments relating to software and services that will be payable in the amounts of $2.1 million, $2.1 million and $2.0 million for 2017, 2018 and 2019, respectively.
| (c) | Warranty |
We provide limited product warranties. Historically, any payments made under these provisions have been immaterial.
| (d) | Litigation and Claims |
From time to time, we may be a party to litigation or subject to claims incident to the ordinary course of business. Although the results of litigation and claims cannot be predicted with certainty, we currently believe that the final outcome of these ordinary course matters will not have a material adverse effect on our business. Regardless of the outcome, litigation can have an adverse impact on us because of defense and settlement costs, diversion of management resources and other factors.
During the third quarter of 2016, we entered into a settlement and licensing agreement, which requires us to make a total cash payment of $0.4 million to a third party. The settlement expense has been recorded as general and administrative expense.
| (e) | Indemnification Obligations |
We agree to standard indemnification provisions in the ordinary course of business. Pursuant to these provisions, we agree to indemnify, hold harmless and reimburse the indemnified party for losses suffered or incurred by the indemnified party, generally our customers, in connection with any United States patent, copyright or other intellectual property infringement claim by any third party arising from the use of our products or services in accordance with the agreement or arising from our gross negligence, willful misconduct or violation of the law (provided that there is not gross or willful misconduct on the part of the other party) with respect to our products or services. The term of these indemnification provisions is generally perpetual from the time of execution of the agreement. We carry insurance that covers certain third-party claims relating to our services and limits our exposure. We have never incurred costs to defend lawsuits or settle claims related to these indemnification provisions.
101
Table of Contents
| (f) | Contingent Grant from Northern Ireland |
In 2016, we received a $0.6 million grant from Invest Northern Ireland to create and maintain a certain number of jobs in Northern Ireland over a certain period of time. The grant proceeds were recorded as a reduction to operating expense, as we determined there is reasonable assurance that we will meet the compliance criteria related to the grant. If we fail to meet the compliance criteria, then a pro rata portion of the grant proceeds would be required to be returned.
| (13) | Employee Benefit Plan |
In December 2008, we established a discretionary 401(k) plan in which all full-time employees above age 18 are eligible to participate 90 days following the applicable date of hire. We did not make any contributions to the plan in 2016, 2015 or 2014.
| (14) | Segment Information and Information about Geographic Areas |
We operate in one segment. Our chief operating decision maker is our Chief Executive Officer, who makes operating decisions, assesses performance and allocates resources on a consolidated basis.
Net revenues by geographic area presented based upon the location of the customer are as follows:
| Year Ended December 31, | ||||||||||||
| 2016 | 2015 | 2014 | ||||||||||
| (in thousands) | ||||||||||||
| North America |
$ | 134,988 | $ | 96,416 | $ | 67,390 | ||||||
| Other |
22,449 | 14,110 | 9,490 | |||||||||
|
|
|
|
|
|
|
|||||||
| Total |
$ | 157,437 | $ | 110,526 | $ | 76,880 | ||||||
|
|
|
|
|
|
|
|||||||
Of the total net revenues generated in North America, 95% was generated in the United States in 2016, and 96% was generated in the United States in 2015 and 2014.
Property and equipment, net by geographic area as of December 31, 2016 and 2015 is presented in the table below:
| As of December 31, | ||||||||
| 2016 | 2015 | |||||||
| (in thousands) | ||||||||
| United States |
$ | 7,063 | $ | 6,633 | ||||
| Other |
1,025 | 899 | ||||||
|
|
|
|
|
|||||
| Total |
$ | 8,088 | $ | 7,532 | ||||
|
|
|
|
|
|||||
| (15) | Related Party Transactions |
In October 2015, Intel Security announced the end-of-sale for the McAfee Vulnerability Manager to customers and partners, effective January 11, 2016, with end-of-life to follow, and announced that we were named their exclusive vulnerability management partner. Under the terms of the commercial agreement, we incur partner referral fees as customers transition from McAfee Vulnerability Manager to Nexpose. During the year ended December 31, 2016, we recognized sales and marketing expense of $2.1 million related to partner referral fees paid to Intel Security. On February 6, 2017, Michael Berry, a member of our Board of Directors, became the Chief Financial Officer of Intel Security (McAfee).
In July 2015, entities affiliated with Technology Crossover Ventures purchased $5.0 million of our common stock (312,500 shares) in a private placement concurrent with the completion of our IPO at a price per share equal to the IPO price of $16.00 per share. Entities affiliated with Technology Crossover Ventures are holders of more than 5% of our capital stock and Timothy McAdam, a member of our board of directors, is affiliated with such entities.
102
Table of Contents
In December 2014, we entered into a Series D Convertible Preferred Stock Purchase Agreement pursuant to which we issued and sold to investors, including certain executive officers and funds affiliated with certain of our directors and 5% stockholders, an aggregate of 2,686,516 shares of our Series D stock at a purchase price of $11.554 per share, for aggregate consideration of $31.0 million. These shares were subsequently converted to common shares in conjunction with our IPO (see Note 8).
Supplementary Data
The following table sets forth our unaudited quarterly consolidated statements of operations data for each of the eight quarters. We have prepared the quarterly financial data on the same basis as the audited consolidated financial statements included in this Annual Report on Form 10-K. In our opinion, the quarterly financial data reflects all adjustments, consisting only of normal recurring adjustment that we consider necessary for a fair presentation of this data. This quarterly financial data should be read in conjunction with our consolidated financial statements and related notes included elsewhere in this Annual Report on Form 10-K. Our historical results are not necessarily indicative of the results to be expected in the future.
| Three Months Ended | ||||||||||||||||||||||||||||||||
| December 31, 2016 |
September 30, 2016 |
June 30, 2016 |
March 31, 2016 |
December 31, 2015 |
September 30, 2015 |
June 30, 2015 |
March 31, 2015 |
|||||||||||||||||||||||||
| (in thousands) | ||||||||||||||||||||||||||||||||
| (unaudited) | ||||||||||||||||||||||||||||||||
| Consolidated Statements of Operations Data: |
||||||||||||||||||||||||||||||||
| Revenue: |
||||||||||||||||||||||||||||||||
| Products |
$ | 24,695 | $ | 23,108 | $ | 21,456 | $ | 20,145 | $ | 18,883 | $ | 16,240 | $ | 14,639 | $ | 13,645 | ||||||||||||||||
| Maintenance and support |
10,366 | 9,694 | 8,962 | 8,381 | 7,849 | 7,002 | 6,253 | 5,799 | ||||||||||||||||||||||||
| Professional services |
9,973 | 7,537 | 6,850 | 6,270 | 6,121 | 5,070 | 4,898 | 4,127 | ||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Total revenue |
45,034 | 40,339 | 37,268 | 34,796 | 32,853 | 28,312 | 25,790 | 23,571 | ||||||||||||||||||||||||
| Cost of revenue: |
||||||||||||||||||||||||||||||||
| Products |
3,747 | 3,415 | 2,687 | 2,598 | 2,532 | 1,504 | 1,339 | 1,546 | ||||||||||||||||||||||||
| Maintenance and support |
1,865 | 1,801 | 1,758 | 1,681 | 1,875 | 1,505 | 1,412 | 1,210 | ||||||||||||||||||||||||
| Professional services |
6,070 | 4,822 | 4,848 | 4,433 | 4,555 | 4,054 | 3,976 | 3,736 | ||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Total cost of revenue |
11,682 | 10,038 | 9,293 | 8,712 | 8,962 | 7,063 | 6,727 | 6,492 | ||||||||||||||||||||||||
| Operating expenses: |
||||||||||||||||||||||||||||||||
| Research and development |
11,065 | 11,616 | 12,932 | 12,342 | 14,256 | 9,945 | 8,131 | 6,414 | ||||||||||||||||||||||||
| Sales and marketing |
24,792 | 21,284 | 21,680 | 22,768 | 23,413 | 16,265 | 14,457 | 13,230 | ||||||||||||||||||||||||
| General and administrative |
7,440 | 7,605 | 6,644 | 6,593 | 7,093 | 5,537 | 5,048 | 4,053 | ||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Total operating expense |
43,297 | 40,505 | 41,256 | 41,703 | 44,762 | 31,747 | 27,636 | 23,697 | ||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Loss from operations |
(9,945) | (10,204) | (13,281) | (15,619) | (20,871) | (10,498) | (8,573) | (6,618) | ||||||||||||||||||||||||
| Interest income (expense), net |
76 | 44 | 26 | (15) | (34) | (1,067) | (737) | (685) | ||||||||||||||||||||||||
| Other income (expense), net |
(293) | 36 | (48) | 196 | (87) | (49) | 163 | (305) | ||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Loss before income taxes |
(10,162) | (10,124) | (13,303) | (15,438) | (20,992) | (11,614) | (9,147) | (7,608) | ||||||||||||||||||||||||
| Income tax (benefit) expense |
(388) | 70 | 149 | 142 | 114 | 211 | 97 | 74 | ||||||||||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
| Net loss |
$ | (9,774) | $ | (10,194) | $ | (13,452) | $ | (15,580) | $ | (21,106) | $ | (11,825) | $ | (9,244) | $ | (7,682) | ||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||||||||||
103
Table of Contents
Item 9. Changes in and Disagreements with Accountants on Accounting and Financial Disclosure.
None.
Item 9A. Controls and Procedures.
Evaluation of Disclosure Controls and Procedures
Our management, with the participation of our chief executive officer and chief financial officer, evaluated the effectiveness of our disclosure controls and procedures as of December 31, 2016. The term “disclosure controls and procedures,” as defined in Rules 13a-15(e) and 15d-15(e) under the Exchange Act of 1934, as amended, means controls and other procedures of a company that are designed to ensure that information required to be disclosed by a company in the reports that it files or submits under the Exchange Act is recorded, processed, summarized and reported, within the time periods specified in the SEC’s rules and forms. Disclosure controls and procedures include, without limitation, controls and procedures designed to ensure that information required to be disclosed by a company in the reports that it files or submits under the Exchange Act is accumulated and communicated to the company’s management, including its principal executive and principal financial officers, as appropriate to allow timely decisions regarding required disclosure. Management recognizes that any controls and procedures, no matter how well designed and operated, can provide only reasonable assurance of achieving their objectives and management necessarily applies its judgment in evaluating the cost-benefit relationship of possible controls and procedures. Based on the evaluation of our disclosure controls and procedures as of December 31, 2016, our chief executive officer and chief financial officer concluded that, as of such date, our disclosure controls and procedures were effective at the reasonable assurance level.
Management’s Report on Internal Control Over Financial Reporting
Our management is responsible for establishing and maintaining adequate internal control over financial reporting, as such term is defined in Rules 13a-15(f) and 15d-15(f) of the Exchange Act. Our management assessed the effectiveness of our internal control over financial reporting as of December 31, 2016 based on the criteria set forth by the Committee of Sponsoring Organizations of the Treadway Commission (COSO) in Internal Control – Integrated Framework (2013). Based on this assessment, management concluded that as of December 31, 2016, our internal control over financial reporting was effective.
This Annual Report on Form 10-K does not include an attestation report of our registered public accounting firm regarding internal control over financial reporting as required by Section 404(c) of Sarbanes Oxley Act of 2002. For as long as we remain an “emerging growth company” as defined in the JOBS Act, we are exempt from the requirement that our registered public accounting firm provide an attestation report on the effectiveness of our internal control over financial reporting.
Inherent Limitations of Internal Controls
Our management, including our chief executive officer and chief financial officer, does not expect that our disclosure controls and procedures or our internal controls will prevent all errors and all fraud. A control system, no matter how well conceived and operated, can provide only reasonable, not absolute, assurance that the objectives of the control system are met. Because of the inherent limitations in all control systems, no evaluation of controls can provide absolute assurance that all control issues and instances of fraud, if any, within the Company have been detected. These inherent limitations include the realities that judgments in decision-making can be faulty, and that breakdowns can occur because of a simple error or mistake. Additionally, controls can be circumvented by the individual acts of some persons, by collusion of two or more people, or by management override of the control. The design of any system of controls also is based in part upon certain assumptions about the likelihood of future events, and there can be no assurance that any design will succeed in achieving its stated goals under all potential future conditions. Over time, controls may become inadequate because of changes in conditions, or the degree of compliance with the policies or procedures may deteriorate. Because of the inherent limitations in a cost-effective control system, misstatements due to error or fraud may occur and not be detected.
104
Table of Contents
Changes in Internal Control over Financial Reporting
There was no change in our internal control over financial reporting identified in connection with the evaluation required by Rule 13a-15(d) and 15d-15(d) of the Exchange Act that occurred during the period covered by this Annual Report on Form 10-K that has materially affected, or is reasonably likely to materially affect, our internal control over financial reporting.
None.
105
Table of Contents
PART III
Item 10. Directors, Executive Officers and Corporate Governance.
The information required by this item is incorporated by reference to our Proxy Statement for our 2017 Annual Meeting of Stockholders to be filed with the SEC within 120 days after the end of the fiscal year ended December 31, 2016.
As part of our system of corporate governance, our board of directors has adopted a code of business conduct and ethics. The code applies to all of our employees, officers (including our principal executive officer, principal financial officer, principal accounting officer or controller, or persons performing similar functions), agents and representatives, including our independent directors and consultants, who are not employees of ours, with regard to their Company-related activities. Our code of business conduct and ethics is available on our website at www.rapid7.com. We intend to post on this section of our website any amendment to our code of business conduct and ethics, as well as any waivers of our code of business conduct and ethics, that are required to be disclosed by the rules of the SEC or the NASDAQ Stock Market.
Item 11. Executive Compensation.
The information required by this item is incorporated by reference to our Proxy Statement for our 2017 Annual Meeting of Stockholders to be filed with the SEC within 120 days after the end of the year ended December 31, 2016.
Item 12. Security Ownership of Certain Beneficial Owners and Management and Related Stockholder Matters.
The information required by this item is incorporated by reference to our Proxy Statement for our 2017 Annual Meeting of Stockholders to be filed with the SEC within 120 days after the end of the year ended December 31, 2016.
Item 13. Certain Relationships and Related Transactions, and Director Independence.
The information required by this item is incorporated by reference to our Proxy Statement for our 2017 Annual Meeting of Stockholders to be filed with the SEC within 120 days after the end of the year ended December 31, 2016.
Item 14. Principal Accounting Fees and Services.
The information required by this item is incorporated by reference to our Proxy Statement for our 2017 Annual Meeting of Stockholders to be filed with the SEC within 120 days after the end of the year ended December 31, 2016.
106
Table of Contents
PART IV
Item 15. Exhibits, Financial Statement Schedules.
(a)(1) Financial Statements
See Index to Consolidated Financial Statements on page 74 of this Annual Report on Form 10-K, which is incorporated into this item by reference.
(a)(3) Exhibits
See Exhibit Index to this Annual Report on Form 10-K, which is incorporated into this item by reference. Each management contract or compensatory plan or arrangement required to be filed has been identified.
(b) Exhibits
See Exhibit Index to this Annual Report on Form 10-K, which is incorporated into this item by reference.
(c) Financial Statement Schedules
All financial statement schedules are omitted because they are not applicable or the required information is shown in the financial statements or notes thereto.
Not applicable.
107
Table of Contents
SIGNATURES
Pursuant to the requirements of Section 13 or 15(d) of the Securities Exchange Act of 1934, as amended, the registrant has duly caused this report to be signed on its behalf by the undersigned, thereunto duly authorized.
| RAPID7, INC. | ||||
| Date: March 9, 2017 |
By: |
/s/ Corey E. Thomas | ||
| Name: Corey E. Thomas | ||||
| Title: President and Chief Executive Officer | ||||
108
Table of Contents
POWER OF ATTORNEY
KNOW ALL BY THESE PRESENTS, that each person whose signature appears below constitutes and appoints Corey E. Thomas and Jeff Kalowski, and each of them, as his true and lawful attorneys-in-fact and agents, each with the full power of substitution, for him and in his name, place or stead, in any and all capacities, to sign any and all amendments to this report, with exhibits thereto and other documents in connection therewith, with the Securities and Exchange Commission, granting unto said attorneys-in-fact and agents, and each of them, full power and authority to do and perform each and every act and thing requisite and necessary to be done in and about the premises, as fully to all intents and purposes as he might or could do in person, hereby ratifying and confirming all that said attorneys-in-fact and agents, or their, his substitute or substitutes, may lawfully do or cause to be done by virtue hereof.
Pursuant to the requirements of the Securities Exchange Act of 1934, as amended, this report has been signed below by the following persons on behalf of the registrant in the capacities and on the dates indicated.
| Name |
Title |
Date | ||
| /s/ Corey E. Thomas Corey E. Thomas |
President, Chief Executive Officer and Director (Principal Executive Officer) |
March 9, 2017 | ||
| /s/ Jeff Kalowski Jeff Kalowski |
Chief Financial Officer (Principal Financial Officer and Principal Accounting Officer) |
March 9, 2017 | ||
| /s/ Michael Berry Michael Berry |
Director |
March 9, 2017 | ||
| /s/ Marc Evan Brown Mark Evan Brown |
Director |
March 9, 2017 | ||
| /s/ Judy Bruner Judy Bruner |
Director |
March 9, 2017 | ||
| /s/ Benjamin Holzman Benjamin Holzman |
Director |
March 9, 2017 | ||
| /s/ Timothy McAdam Timothy McAdam |
Director |
March 9, 2017 | ||
| /s/ Alan Matthews Alan Matthews |
Director |
March 9, 2017 | ||
| /s/ J. Benjamin Nye J. Benjamin Nye |
Director |
March 9, 2017 | ||
| /s/ Thomas Schodorf Thomas Schodorf |
Director |
March 9, 2017 | ||
| /s/ John Sweeney John Sweeney |
Director |
March 9, 2017 | ||
109
Table of Contents
Exhibit Index
| Exhibit Number |
Description | |
| 2.1(1) | Agreement and Plan of Merger and Reorganization, dated October 9, 2015. | |
| 3.1(2) | Amended and Restated Certificate of Incorporation of Rapid7, Inc. | |
| 3.2(3) | Amended and Restated Bylaws of Rapid7, Inc. | |
| 4.1(4) | Form of common stock certificate of Rapid7, Inc. | |
| 4.2(5) | Amended and Restated Investors’ Rights Agreement by and among Rapid7, Inc. and certain of its stockholders, dated December 9, 2014. | |
| 4.3(6) | Amendment No. 1 to Investors’ Rights Agreement, dated October 13, 2015. | |
| 10.1+(7) | 2011 Stock Option and Grant Plan and Forms of Stock Option Agreement, Stock Option Exercise Notice and Restricted Stock Agreement thereunder. | |
| 10.2+(8) | Rapid7, Inc. 2015 Equity Incentive Plan, as amended. | |
| 10.3+(9) | Forms of Stock Option Agreement, Notice of Exercise, Stock Option Grant Notice and Restricted Stock Unit Agreement under the Rapid7, Inc. 2015 Equity Incentive Plan, as amended. | |
| 10.4+(10) | Rapid7, Inc. 2015 Employee Stock Purchase Plan. | |
| 10.5+(11) | Form of Indemnification Agreement by and between Rapid7, Inc. and each of its directors and executive officers. | |
| 10.6(12) | Office Lease Agreement, dated as of November 11, 2013, by and between Rapid7, Inc. and MA-100 Summer Street Owner, L.L.C. | |
| 10.7(13) | First Amendment to Office Lease Agreement, dated as of April 10, 2015 by and between Rapid7, Inc. and MA-100 Summer Street Owner, L.L.C. | |
| 10.8(14) | Second Amendment to Office Lease Agreement, dated as of August 17, 2015, by and between Rapid7, Inc. and MA-100 Summer Street Owner, L.L.C. | |
| 10.9(15) | Common Stock Purchase Agreement by and among Rapid7, Inc., TCV VII, L.P., TCV VII (A), L.P. and TCV Members Fund, L.P., dated June 25, 2015. | |
| 10.10+(16) | 2016 Bonus Plan of Rapid7, Inc. | |
| 10.11+(17) | Rapid7, Inc. Executive Incentive Bonus Plan | |
| 10.12+(18) | Non-Employee Director Compensation Policy of Rapid7, Inc. | |
| 10.13+(19) | Employment Agreement, dated as of January 3, 2013, by and between Rapid7, Inc. and Corey Thomas. | |
| 10.14+(20) | Offer Letter Agreement, dated as of December 4, 2012, by and between Rapid7, Inc. and Steven Gatoff. | |
| 10.15+(21) | Offer Letter Agreement, dated as of June 13, 2013, by and between Rapid7 UK Limited and Richard Moseley. | |
| 10.16+(22) | Amendment to Employment Agreement, dated as of April 4, 2016, by and between Rapid7, Inc. and Corey Thomas. | |
| 10.17+(23) | Amendment to Offer Letter, dated as of April 2, 2016, by and between Rapid7, Inc. and Steven Gatoff. | |
| 10.18+(24) | Form of Severance and Equity Award Vesting Acceleration Letter. | |
| 10.19+(25) | Third Amendment to Office Lease Agreement, dated as of March 23, 2016, by and between Rapid7, Inc. and MA-100 Summer Street Owner, L.L.C. | |
| 10.20+(26) | Transition and Release Agreement, dated as of August 5, 2016, by and between Rapid7, Inc. and Steven Gatoff. | |
| 10.21+(27) | Offer Letter Agreement, dated as of October 3, 2016, by and between Rapid7, Inc. and Andrew Burton. | |
| 10.22+(28) | Employment Agreement, dated as of November 28, 2016, by and between Rapid7, Inc. and Jeffrey Kalowski. | |
| 10.23* | Fourth Amendment to Office Lease Agreement, dated as of February 14, 2017, by and between Rapid7, Inc. and MA-100 Summer Street Owner, L.L.C. | |
110
Table of Contents
| Exhibit Number |
Description | |
| 21.1* | List of subsidiaries of Rapid7, Inc. | |
| 23.1* | Consent of KPMG, LLP. | |
| 24.1 | Power of Attorney (incorporated by reference to the signature pages of this Annual Report on Form 10-K). | |
| 31.1* | Certification of Principal Executive Officer Pursuant to Rules 13a-14(a) and 15d-14(a) under the Securities Exchange Act of 1934, as Adopted Pursuant to Section 302 of the Sarbanes-Oxley Act of 2002. | |
| 31.2* | Certification of Principal Financial Officer Pursuant to Rules 13a-14(a) and 15d-14(a) under the Securities Exchange Act of 1934, as Adopted Pursuant to Section 302 of the Sarbanes-Oxley Act of 2002. | |
| 32.1** | Certification of Principal Executive Officer Pursuant to 18 U.S.C. Section 1350, as Adopted Pursuant to Section 906 of the Sarbanes-Oxley Act of 2002. | |
| 32.2** | Certification of Principal Financial Officer Pursuant to 18 U.S.C. Section 1350, as Adopted Pursuant to Section 906 of the Sarbanes-Oxley Act of 2002. | |
| 101.INS | XBRL Instance Document. | |
| 101.SCH | XBRL Taxonomy Extension Schema Document. | |
| 101.CAL | XBRL Taxonomy Extension Calculation Linkbase Document. | |
| 101.DEF | XBRL Taxonomy Extension Definition Linkbase Document. | |
| 101.LAB | XBRL Taxonomy Extension Label Linkbase Document. | |
| 101.PRE | XBRL Taxonomy Extension Presentation Linkbase Document. | |
| (1) | Previously filed as Exhibit 2.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on October 13, 2015, and incorporated herein by reference. |
| (2) | Previously filed as Exhibit 3.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on July 22, 2015, and incorporated herein by reference. |
| (3) | Previously filed as Exhibit 3.2 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on July 22, 2015, and incorporated herein by reference. |
| (4) | Previously filed as Exhibit 4.1 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on July 6, 2015, and incorporated herein by reference. |
| (5) | Previously filed as Exhibit 4.2 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (6) | Previously filed as Exhibit 4.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on October 13, 2015, and incorporated herein by reference. |
| (7) | Previously filed as Exhibit 10.1 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (8) | Previously filed as Exhibit 10.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on October 13, 2015, and incorporated herein by reference. |
| (9) | Previously filed as Exhibit 10.3 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on July 6, 2015, and incorporated herein by reference. |
| (10) | Previously filed as Exhibit 10.3 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on July 6, 2015, and incorporated herein by reference. |
| (11) | Previously filed as Exhibit 10.5 to the Registrant’s Annual Report on Form 10-K (File No. 001-37496), filed with the Securities and Exchange Commission on March 10, 2016, and incorporated herein by reference. |
111
Table of Contents
| (12) | Previously filed as Exhibit 10.1 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (13) | Previously filed as Exhibit 10.1 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (14) | Previously filed as Exhibit 10.3 to the Registrant’s Quarterly Report on Form 10-Q (File No. 001-37496), filed with the Securities and Exchange Commission on August 19, 2015. |
| (15) | Previously filed as Exhibit 10.13 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 26, 2015, and incorporated herein by reference. |
| (16) | Previously filed as Exhibit 10.11 to the Registrant’s Annual Report on Form 10-K (File No. 001-37496), filed with the Securities and Exchange Commission on March 10, 2016, and incorporated herein by reference. |
| (17) | Previously filed as Exhibit 10.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on February 2, 2017, and incorporated herein by reference. |
| (18) | Previously filed as Exhibit 10.1 to the Registrant’s Quarterly Report on Form 10-Q (File No. 001-37496), filed with the Securities and Exchange Commission on November 12, 2015. |
| (19) | Previously filed as Exhibit 10.9 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (20) | Previously filed as Exhibit 10.10 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (21) | Previously filed as Exhibit 10.11 to the Registrant’s Registration Statement on Form S-1/A (File No. 333-204874), filed with the Securities and Exchange Commission on June 11, 2015, and incorporated herein by reference. |
| (22) | Previously filed as Exhibit 10.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on April 5, 2016, and incorporated herein by reference. |
| (23) | Previously filed as Exhibit 10.2 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on April 5, 2016, and incorporated herein by reference. |
| (24) | Previously filed as Exhibit 10.3 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on April 5, 2016, and incorporated herein by reference. |
| (25) | Previously filed as Exhibit 10.1 to the Registrant’s Quarterly Report on Form 10-Q (File No. 001-37496), filed with the Securities and Exchange Commission on May 12, 2016, and incorporated herein by reference. |
| (26) | Previously filed as Exhibit 10.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on August 8, 2016, and incorporated herein by reference. |
| (27) | Previously filed as Exhibit 10.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on October 4, 2016, and incorporated herein by reference. |
| (28) | Previously filed as Exhibit 10.1 to the Registrant’s Current Report on Form 8-K (File No. 001-37496), filed with the Securities and Exchange Commission on November 28, 2016, and incorporated herein by reference. |
| * | Filed herewith. |
| ** | This certification is deemed not filed for purposes of Section 18 of the Securities Exchange Act of 1934, as amended, or otherwise subject to the liability of that section, nor shall it be deemed incorporated by reference into any filing under the Securities Act of 1933, as amended, or the Securities Exchange Act of 1934, as amended. |
| + | Indicates management contract or compensatory plan. |
112
